Truckee’s Secure Files
When a business is dealing with encrypted files, the failure usually started earlier. Phishing clicks, password reuse, and weak account hygiene can weaken governance policy and audit preparation over time and leave manufacturing plants in The Truckee Meadows exposed when pressure hits. Addressing the problem means tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Encrypted Files Usually Point to a Human-Control Failure First
When files are suddenly encrypted in a manufacturing environment, the immediate question is how to restore operations. The more important question is what control failed before encryption started. In most Truckee Meadows incidents, the first break is not a firewall defect or an exotic software exploit. It is a user-level action tied to the human element: a fake reset-password message, password reuse across systems, weak multifactor enrollment, or an account that kept broader access than the employee actually needed.
That is why encrypted files are often a governance problem as much as a recovery problem. If account hygiene is weak, audit preparation also weakens because access reviews, logging, approval workflows, and exception handling are usually inconsistent in the same environments. We typically see this most clearly in plants that depend on shared folders, ERP exports, estimating files, and vendor documentation moving between office staff and production teams. A structured approach to governance policy and audit preparation in Northern Nevada helps reduce that exposure by making identity controls, access reviews, and user accountability part of normal operations instead of a once-a-year exercise.
In Roger’s case, the encryption event was only the visible symptom. The underlying issue was that one credential could still reach too much of the business too quickly. In Reno and Sparks manufacturing settings, where teams often balance front-office coordination with warehouse, fabrication, and field communication, that kind of access sprawl turns a single phishing click into a broader interruption.
- Identity sprawl: Shared credentials, stale permissions, and weak password discipline allow one compromised account to touch file shares, cloud storage, and line-of-business systems faster than most teams expect.
- Email trust abuse: Attackers routinely imitate password reset notices, vendor messages, and Microsoft prompts because they fit normal business traffic and are more likely to be opened during busy production cycles.
- Audit drift: When access approvals, MFA enforcement, and sign-in review are inconsistent, governance policy becomes harder to defend and incident response takes longer because no one is fully certain what is normal.
Practical Remediation for Manufacturing Environments Under Pressure
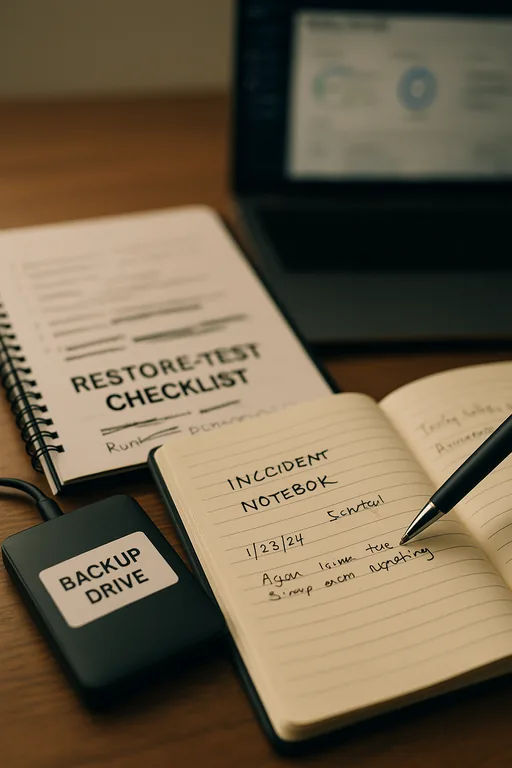
The first step is containment: disable affected accounts, revoke active sessions, isolate impacted endpoints, and preserve logs before cleanup starts. After that, the real remediation work is to reduce the chance that the same user-driven path works again. For most manufacturing plants, that means tightening Microsoft 365 conditional access, enforcing phishing-resistant MFA where possible, removing local admin rights, validating backups against actual restore objectives, and segmenting file access so office compromise does not automatically spread into broader operational data.
We also recommend formalizing response workflows through infrastructure management programs for multi-site operations so alerting, backup validation, endpoint isolation, and account review happen on a schedule rather than after an outage. For user-driven attack paths, the most useful external baseline remains CISA guidance on phishing-resistant authentication and account protection, which businesses can review at cisa.gov . In practice, the goal is not just stronger technology. It is reducing the number of routine decisions employees have to make under pressure.
- MFA hardening: Require multifactor authentication for all remote and cloud access, block legacy authentication, and review impossible-travel and risky sign-in alerts weekly.
- Access reduction: Remove broad shared-folder permissions, separate finance and production documentation where possible, and apply least-privilege access by role.
- Backup validation: Test restores for file shares, ERP exports, and critical admin data so recovery time is measured and not assumed.
- Endpoint control: Deploy EDR with isolation capability and tune alerts so suspicious script execution, credential theft behavior, and mass file changes are escalated quickly.
Field Evidence: Shared Access Cleanup Reduced Recovery Exposure
We worked with a Northern Nevada operation that had a familiar pattern: broad shared-drive access, inconsistent MFA enrollment, and too many users relying on saved credentials in browsers. Before remediation, a single suspicious sign-in created uncertainty across scheduling, purchasing, and document control because no one could immediately confirm what data the account could reach. The business was also dealing with the practical realities common around the Reno-Sparks industrial corridors: mixed office and warehouse workflows, vendor file exchanges, and staff moving between desks, shop floors, and mobile devices.
After access cleanup, conditional access enforcement, and documented restore testing, the same type of suspicious login event became a contained security incident instead of a business-wide disruption. Leadership also had clearer reporting because sign-in review, exception handling, and escalation paths were documented through IT consulting in Northern Nevada rather than handled informally.
- Result: Reduced privileged accounts by 42%, cut file-share exposure by department, and brought tested restore time for critical office data down to under 3 hours.
Reference Points for Preventing File Encryption Events
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Governance Policy And Audit Preparation and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.

Local Support in The Truckee Meadows
We support businesses across Reno, Sparks, and nearby industrial corridors where manufacturing, logistics, and office operations often depend on the same identity systems and shared data. From our Reno office, Montane Building Group HQ is typically about 17 minutes away, which reflects the practical service footprint for on-site response, planning meetings, and recovery coordination when account compromise or file encryption affects daily operations.
What Manufacturing Leaders Should Take Away
Encrypted files in a Truckee Meadows manufacturing business usually indicate that identity controls, user habits, and access governance were already drifting before the incident became visible. The technical cleanup matters, but the longer-term fix is reducing how much damage one compromised account can do and making audit-ready controls part of normal operations.
For most organizations, that means reviewing who has access to what, enforcing stronger sign-in controls, validating restores, and documenting response steps clearly enough that production, finance, and administration can keep moving even when an account has to be shut down quickly.

