Truckee Meadows
When a business is dealing with encrypted files, the failure usually started earlier. Poor safeguards, inconsistent records handling, and a slow response can weaken disaster recovery planning and recovery over time and leave manufacturing plants in The Truckee Meadows exposed when pressure hits. Addressing the problem means documenting safeguards, tightening response steps, and protecting sensitive data.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Encrypted Files Become a Legal Liability Failure
When files are encrypted inside a manufacturing environment in The Truckee Meadows, the immediate problem is lost access. The deeper problem is whether the business can prove what happened, what data was affected, what safeguards were in place, and how quickly it responded. That is where the legal liability issue begins. If customer records, quality documents, vendor contracts, or employee information are mixed into the same file shares as production data, an encryption event can quickly become a records integrity problem rather than a simple outage.
We see this most often in plants that have grown faster than their controls. Shared folders expand, permissions drift, backups run without regular restore testing, and incident response stays informal. In Northern Nevada, that creates a serious exposure because a company may be asked to explain not only why systems failed, but why it lacked documented safeguards before the event. As the local discussion often goes, “I didn’t know” is not a legal defense in a Reno court. Businesses trying to reduce that exposure usually need stronger disaster recovery planning and recovery in Northern Nevada so they can show a defensible process, not just a scramble after the fact.
- Records segregation failure: Sensitive client files, HR records, and production documents often sit in the same storage paths, which makes it harder to determine scope and reporting obligations after encryption.
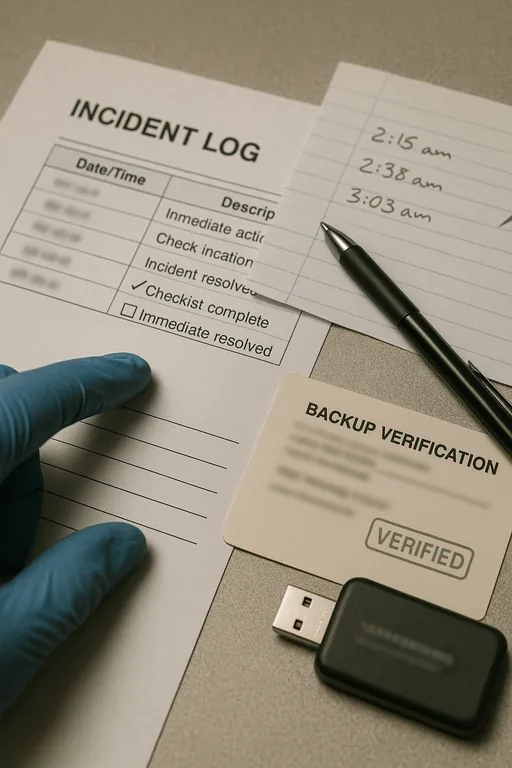
- Unverified backups: A backup job that reports success but has not been tested for clean restoration can extend downtime and weaken confidence in the recovery timeline.
- Slow escalation: Delayed reporting from the plant floor to management and IT increases the chance that encrypted files spread across mapped drives and line-of-business systems.
- Weak access control: Broad permissions and stale accounts allow one compromised credential to affect scheduling, purchasing, and finance at the same time.
- Documentation gaps: As seen in Eva’s case, incomplete logs and inconsistent handling records make legal review and insurance discussions harder than they should be.
Practical Remediation for Recovery, Containment, and Defensible Response
The right fix is not just decrypting or restoring files. Manufacturing plants need a response structure that contains the event, preserves evidence, restores clean systems in the right order, and documents each decision. That usually starts with isolating affected endpoints, disabling compromised accounts, validating backup integrity, and identifying whether the incident touched regulated or contract-sensitive data. From there, the business needs a recovery sequence that prioritizes ERP access, scheduling, shipping, quality records, and finance based on operational impact.
We also recommend tightening frontline escalation and user support. Many incidents worsen because employees do not know when to stop using a workstation or who to call first. A disciplined IT support and help desk process for manufacturing operations helps contain damage early and creates a cleaner timeline for management, counsel, and insurers. For incident handling and recovery planning, the guidance from CISA’s ransomware guide remains practical and usable for small and mid-sized organizations.
- Backup validation: Test restores on a schedule and confirm that critical file shares, ERP data, and quality documentation can be recovered cleanly within target timeframes.
- MFA hardening: Enforce multifactor authentication for remote access, admin accounts, and cloud-connected file systems to reduce credential-driven spread.
- Network segmentation: Separate plant-floor systems, office users, and sensitive records repositories so one compromised endpoint does not expose the full operation.
- Incident logging: Maintain a written chain of actions, affected systems, user reports, and recovery steps to support legal, insurance, and compliance review.
- Endpoint control: Standardize patching, EDR, and device policy through proactive device and endpoint management so risky systems are identified before they become the entry point.
Field Evidence: Restoring Production Without Losing the Audit Trail
In one Truckee Meadows manufacturing environment, the initial state was familiar: shared drives had grown for years, old user groups still had access, and backups existed but had not been tested against a realistic plant outage. The business had no clean way to separate production records from customer-facing documents, so leadership could not immediately answer whether the event was only operational or also reportable.
After containment, the recovery plan was rebuilt around restore testing, access cleanup, documented escalation, and system prioritization. That mattered in a local setting where multi-building operations and warehouse traffic between Reno and Sparks can amplify even a short outage. Once the controls were in place, management had a clearer timeline, cleaner evidence, and a faster path to resuming shipping and invoicing.
- Result: Recovery testing reduced estimated file restoration time from more than 14 hours to under 4 hours, while access review cut unnecessary shared-folder permissions by 62 percent.
Operational Reference for Encrypted File Response
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Disaster Recovery Planning And Recovery and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.

Local Support in The Truckee Meadows
Manufacturing plants in Reno and Sparks often need fast coordination between office systems, plant-floor devices, file storage, and recovery planning. From our Reno office, the Kleppe Lane industrial area is typically about 12 minutes away under normal conditions, which matters when a file encryption event is affecting production schedules, receiving, or shipping. Local support is not just about arriving quickly; it is about understanding how Northern Nevada facilities actually operate and how to restore systems without losing the documentation needed for management and legal review.
What Manufacturing Leaders Should Take Away
Encrypted files in a manufacturing plant are rarely just a technical inconvenience. In The Truckee Meadows, they can interrupt production, delay shipping, compromise records, and create legal exposure if the business cannot show what protections were in place and how the response was handled. The real failure is usually upstream: weak segmentation, poor records discipline, untested backups, and unclear escalation.
The practical answer is to treat recovery and liability together. If systems can be restored quickly, evidence is preserved, and sensitive data is properly controlled, leadership is in a much stronger position operationally and legally. That is the standard businesses should aim for before the next outage forces the issue.

