Truckee Data Breach
When a business is dealing with a data breach, the failure usually started earlier. Phishing clicks, password reuse, and weak account hygiene can weaken identity email and user security over time and leave construction firms in The Truckee Meadows exposed when pressure hits. Addressing the problem means tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

How the Human Element Opens the Door to a Breach
For construction firms in The Truckee Meadows, a data breach often starts with identity compromise rather than a firewall failure. The pattern is familiar: a user receives a convincing email, reuses a password that has already been exposed elsewhere, or approves a login prompt without verifying the request. Once an attacker gets into email or a cloud account, they do not need much time to create operational damage. They can monitor conversations, alter payment instructions, harvest contact lists, and move laterally into file shares or project systems.
The human element matters because construction teams work under deadline pressure. Estimators, project managers, accounting staff, and field coordinators are constantly exchanging plans, change orders, lien documents, and vendor invoices. That pace makes it easier for fake reset notices and spoofed approval emails to blend in. We typically find that businesses reduce this exposure faster when they treat identity email and user security in Northern Nevada as an operational control, not just a user training topic. In cases like Madelyn’s, the breach was not caused by one careless moment alone; it was enabled by weak MFA enforcement, poor password discipline, and a lack of alerting around unusual sign-in behavior.
- Email identity compromise: Attackers commonly target Microsoft 365 accounts because they provide access to internal communication, shared files, and password reset paths for other business systems.
- Password reuse: Staff who reuse credentials across personal and business services increase the chance that a previously exposed password will work against company accounts.
- MFA fatigue and prompt abuse: Repeated authentication prompts can pressure users into approving a login they did not initiate.
- Construction workflow urgency: Fast-moving approvals, mobile device use, and frequent vendor communication make phishing messages harder to spot during busy project cycles.
Practical Remediation for Identity, Email, and Recovery Readiness
The fix is not a single product. It is a layered set of controls that reduces the chance of account takeover and limits the damage if one account is compromised. Start with phishing-resistant MFA where possible, conditional access policies, mailbox auditing, and sign-in risk monitoring. Then tighten password policy, disable legacy authentication, and review who can approve financial changes by email alone. Construction firms should also separate high-risk admin accounts from day-to-day user accounts and make sure project documentation platforms are not all tied to one identity without backup access paths.
Recovery planning matters just as much as prevention. If an attacker gets into email, the business needs a clean process for account lockout, session revocation, mailbox review, password resets, and restoration of trusted communications. That is where compliance-focused IT management for continuity and backup becomes operationally important. We also recommend aligning controls with guidance from CISA Secure Our World , especially around MFA, password managers, and phishing awareness.
- MFA hardening: Require strong multifactor authentication for all cloud email, VPN, and line-of-business access, with number matching or phishing-resistant methods where supported.
- Conditional access: Block risky logins by geography, impossible travel, unmanaged devices, and legacy protocols.
- Mailbox protection: Enable auditing, forwarding rule alerts, and executive impersonation filtering.
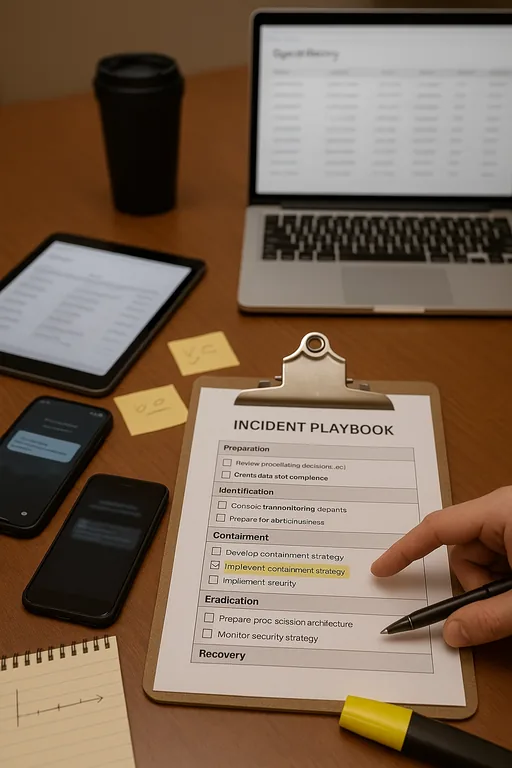
- Incident playbooks: Document who disables accounts, who validates invoices, and how staff communicate if email trust is broken.
- Backup validation: Test restoration of critical files, finance records, and project documentation so recovery is measured, not assumed.
Field Evidence: Stopping Invoice Fraud Before It Spread Across Job Sites
We worked through a similar pattern with a regional contractor operating between Reno, Sparks, and south county job locations. Before remediation, the company had inconsistent MFA enrollment, no review of suspicious mailbox rules, and no formal process for validating invoice changes sent by email. A compromised user account led to altered payment instructions and confusion between the office and field teams because document links could no longer be trusted.
After tightening identity controls, enforcing sign-in policy, and validating restore procedures through backup and recovery programs that support business operations , the company moved from reactive cleanup to controlled response. The office could isolate accounts quickly, restore trusted access, and continue dispatching crews even when one communication channel was under review. That matters in Northern Nevada, where teams may be coordinating from Reno offices to outlying sites with limited tolerance for document delays or billing disruption.
- Result: Suspicious login response time dropped to under 15 minutes, unauthorized mailbox forwarding was eliminated, and invoice verification errors were reduced through a documented approval process.
Identity and Email Security Control Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Identity Email And User Security and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.

Local Support in The Truckee Meadows
We support businesses throughout Reno, Sparks, and nearby south county corridors where construction teams often depend on cloud email, mobile approvals, and fast coordination between office staff and field personnel. From our Reno office, Pleasant Valley is typically about 23 minutes away depending on traffic, which is why response planning has to be documented before an identity incident disrupts billing or project communication.
What Construction Firms Should Take Away
A data breach tied to the human element is usually a control problem that built up over time. Phishing clicks, reused passwords, weak MFA practices, and poor verification habits create a path into email and cloud systems long before the business notices visible damage. For construction firms in The Truckee Meadows, that can quickly affect billing, vendor communication, project documentation, and trust in day-to-day approvals.
The practical response is to tighten identity controls, reduce reliance on email trust alone, and test recovery steps before an incident forces the issue. When those pieces are in place, a compromised account becomes a contained event instead of a business-wide disruption.

