Truckee Data Breach
When a business is dealing with a data breach, the failure usually started earlier. Unclear ownership, overlapping tools, and fragmented support can weaken backup and disaster recovery over time and leave construction firms in The Truckee Meadows exposed when pressure hits. Addressing the problem means clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

How Vendor Chaos Turns Into Breach Exposure
A data breach in a Truckee Meadows construction firm often starts with a management problem before it becomes a security event. We typically find overlapping vendors handling internet, phones, line-of-business applications, cloud storage, printers, and endpoint tools without one party owning the full escalation path. That leaves backup jobs unverified, former accounts still active, and critical systems patched inconsistently. For firms moving between job trailers, warehouses, and main offices across Reno and Sparks, those gaps compound quickly when field teams need immediate access to plans, change orders, and billing records.
The vendor-chaos pattern is especially common when an office manager is informally coordinating technical decisions that should sit inside a defined operational process. In cases like Walter’s, nobody can answer basic questions fast enough: who owns Microsoft 365 retention, who validates backup recovery, who disables old vendor access, and who has authority to isolate a compromised endpoint. Businesses trying to reduce that exposure usually need stronger backup and disaster recovery oversight in Northern Nevada so recovery ownership, retention policy, and restoration testing are not spread across disconnected providers.
- Fragmented ownership: When internet, cloud apps, endpoint security, and backup are managed by separate vendors without a single escalation owner, breach response slows down and recovery assumptions often prove wrong.
- Overlapping tools: Construction firms frequently inherit duplicate sync platforms, unmanaged file shares, and old remote-access utilities that expand the attack surface.
- Unverified recovery: A backup report that says “successful” does not confirm that estimating files, accounting data, and project documentation can actually be restored cleanly.
- Operational pressure: Tight bid deadlines, mobile crews, and after-hours vendor activity increase the chance that exceptions are made without documentation or review.
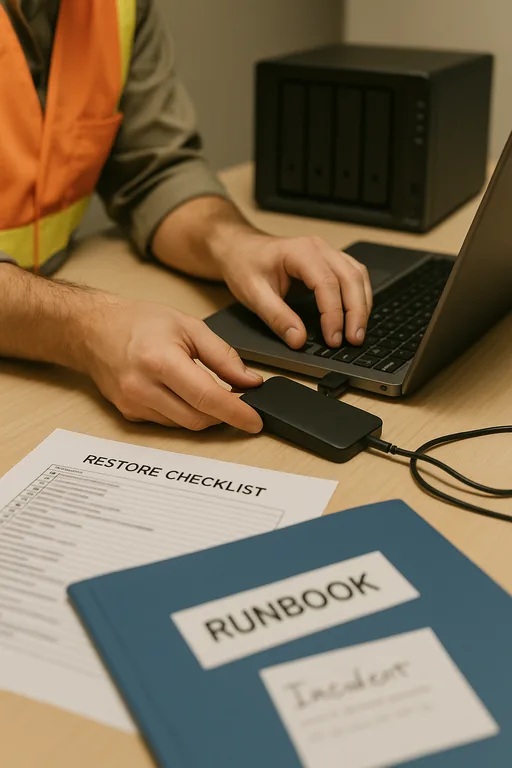
What Practical Remediation Looks Like
The fix is not adding another vendor. It is assigning clear ownership, reducing tool sprawl, and documenting who does what during an incident. We usually start by mapping every system that touches sensitive data: Microsoft 365, file shares, estimating platforms, accounting systems, mobile devices, VPN access, and backup repositories. From there, we remove duplicate tools, disable stale accounts, confirm MFA coverage, and test whether the business can restore priority data within an acceptable timeframe.
Construction firms also need a simple operating model for escalation. That means one accountable technical lead, one current asset and vendor register, and one documented incident path for outages, suspicious logins, and failed restores. This is where business IT operations management becomes important because it turns scattered vendor relationships into a controlled process. For breach-response planning and recovery controls, the guidance from CISA is practical and aligns well with what mid-sized Nevada businesses actually need to implement.
- Ownership matrix: Assign one internal decision-maker and one technical owner for backup, identity, endpoint security, and vendor escalation.
- Backup validation: Run scheduled restore tests for estimating data, accounting records, and shared project files instead of relying on status emails alone.
- MFA hardening: Enforce phishing-resistant MFA where possible and remove legacy authentication paths that bypass current controls.
- Endpoint containment: Deploy EDR with isolation capability so a compromised workstation can be cut off without shutting down the whole office.
- Access cleanup: Review former employee, subcontractor, and vendor accounts quarterly and remove unnecessary remote tools.
Field Evidence: Vendor Consolidation Reduced Recovery Delays
We worked through a similar pattern for a regional operation serving job sites between south Reno and Carson-area suppliers. Before cleanup, the company had separate contacts for internet, phones, Microsoft 365, backup, and line-of-business software, with no shared incident process. During one file-access disruption, staff spent hours deciding who should even open the ticket while accounting and project management worked from stale local copies.
After consolidating escalation ownership, documenting system dependencies, and standardizing support under managed IT support plans for multi-location operations , the business had a cleaner response path. Backup verification became a scheduled control instead of an assumption, and vendor handoffs stopped delaying containment decisions during busy project weeks.
- Result: Incident triage time dropped from most of a workday to under 45 minutes, backup restore testing moved to a documented monthly schedule, and untracked vendor access was reduced by more than 70 percent.
Construction Breach Control Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Backup And Disaster Recovery and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.

Local Support in The Truckee Meadows
Construction firms in Reno, Sparks, and nearby industrial corridors often need fast on-site coordination when vendor confusion affects access to plans, accounting, or backup recovery. From our Ryland Street office, Sierra Meadows and surrounding south Reno facilities are a routine service area, which makes it practical to support both remote triage and in-person escalation when systems, vendors, and business operations need to be aligned quickly.
Why This Audit Matters Before the Next Incident
For construction firms in The Truckee Meadows, a breach is often the visible result of a quieter operational problem: too many vendors, unclear ownership, and no tested recovery path. When backup, identity, endpoint protection, and escalation are spread across disconnected providers, the business loses time before it can even begin containment and restoration.
The practical takeaway is straightforward. Reduce overlap, assign accountability, verify recovery, and document who responds when systems fail. That approach protects billing, scheduling, project coordination, and client trust far more effectively than adding another disconnected tool to an already fragmented environment.

