Sparks Plant Audit
The outage or lockout is usually the last symptom to appear, not the first. Phishing clicks, password reuse, and weak account hygiene create weak points that can disrupt endpoint and threat protection and put account security, access stability, and business continuity at risk. Reducing that risk starts with tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

How Human Error Becomes Encrypted Files in a Sparks Plant
When files are encrypted in a manufacturing environment, the root cause is often not a firewall failure or an exotic exploit. More often, it starts with a person trusting a convincing message, reusing a password, or working around a security prompt to keep production moving. In Sparks, problems like this often begin with phishing clicks, password reuse, and weak account hygiene. Left alone, they can disrupt endpoint and threat protection and put account security, access stability, and business continuity at risk.
We typically see the sequence unfold in stages. A user clicks a fake reset link, enters valid credentials, and the attacker uses that access to move into email, file shares, remote access tools, or line-of-business systems. Once that happens, the visible issue is the last stage: locked files, disabled accounts, or security tools being tampered with. That is why plants dealing with recurring user-driven risk often need stronger endpoint and threat protection in Northern Nevada tied directly to identity controls, mailbox monitoring, and rapid isolation procedures. In incidents like the one affecting Nil’s workflow, the real failure was not just the click itself. It was the absence of layered controls that should have limited what happened next.
- Credential exposure: A phishing page captures a valid password, giving an attacker a clean login path that looks legitimate in basic logs.
- Account hygiene weakness: Password reuse between Microsoft 365, VPN, plant systems, or vendor portals expands the blast radius quickly.
- Endpoint control gap: If local admin rights, weak EDR policies, or delayed alert review are present, encryption activity can spread before containment starts.
- Operational consequence: Production support teams lose access to work instructions, shipping documents, quality records, and shared folders needed to keep shifts moving.
Practical Remediation for Identity, Endpoint, and Recovery Control
The fix is not a single product. It is a control stack. First, compromised accounts need immediate containment: forced password resets, token revocation, MFA review, mailbox rule inspection, endpoint isolation, and confirmation that no persistence was left behind. After that, the environment needs hardening so the same event does not repeat under a different subject line.
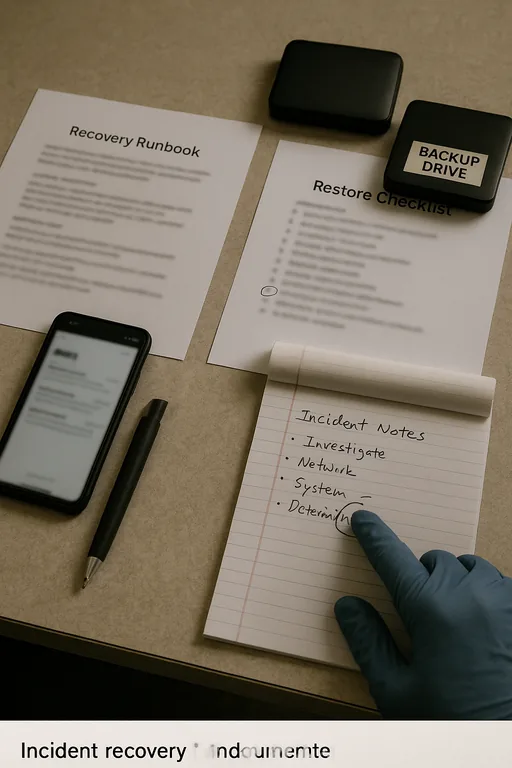
For manufacturing operations, we recommend separating office productivity risk from production-support risk wherever possible. That means stronger MFA enforcement, conditional access, removal of unnecessary admin rights, tuned EDR policies, and tested restoration procedures. Recovery planning matters just as much as prevention. Businesses that need to restore file access quickly after encryption events usually benefit from structured disaster recovery planning and recovery support that includes backup validation, recovery time targets, and role-based response steps. CISA’s guidance on strong passwords and phishing-resistant habits is also useful because it addresses the exact human behaviors that often open the door.
- MFA hardening: Require phishing-resistant MFA where possible and block legacy authentication that bypasses modern controls.
- Endpoint isolation: Configure EDR to quarantine suspicious encryption behavior and alert on credential theft indicators.
- Privilege reduction: Remove local admin access from standard users and separate admin credentials from daily work accounts.
- Backup validation: Test file-level and system-level restores on a schedule so recovery assumptions are proven before an incident.
- User conditioning: Run short, recurring phishing simulations and reinforce reporting habits instead of relying on annual awareness training alone.
Field Evidence: Shift Operations Stabilized After Identity and Backup Controls Were Tightened
We have seen this pattern in industrial and warehouse corridors from Sparks to the Reno-Sparks distribution areas: before remediation, one compromised account could interrupt shared folders, purchasing records, and shipping documentation for most of a day. After remediation, the same environment had segmented access, better alerting, and a recovery path that did not depend on guesswork.
In one comparable case, the business moved from reactive cleanup to a documented process that included MFA enforcement, mailbox rule review, endpoint isolation playbooks, and verified restore points. That reduced uncertainty during shift changes and gave operations managers a clear path for restoring access without exposing clean systems. Longer term, pairing those controls with business continuity and backup compliance planning helped leadership treat encrypted files as an operational risk to be managed, not just an IT event to survive.
- Result: Recovery time for critical shared files dropped from nearly a full workday to under 2 hours, and no repeat encryption event was observed in the following 12 months.
Human Element Audit Reference Points for Manufacturing Environments
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Endpoint And Threat Protection and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.

Local Support in Reno and Sparks
We support organizations across Reno and Sparks where fast response matters, especially when account compromise or encrypted files affect scheduling, production support, or shared business systems. From our Ryland Street office, the West University area is a short drive, and that proximity helps when a business needs on-site coordination, containment, and recovery planning tied to real operating conditions in Northern Nevada.
Why the Human Element Has to Be Audited Like Any Other Control
Encrypted files in a Sparks manufacturing environment usually point back to a chain of preventable decisions: a trusted-looking email, reused credentials, weak access controls, and untested recovery assumptions. The visible outage is only the final stage. The real work is reducing how easily a user action can become a business interruption.
That means treating identity protection, endpoint response, backup validation, and user behavior as one operating system for resilience. When those pieces are aligned, a phishing click is far less likely to become a plant-wide disruption, delayed shipments, or a long restoration window.

