Sparks Data Breach
The outage or lockout is usually the last symptom to appear, not the first. Poor safeguards, inconsistent records handling, and a slow response create weak points that can disrupt managed IT support plans and put legal exposure, reporting obligations, and client trust at risk. Reducing that risk starts with documenting safeguards, tightening response steps, and protecting sensitive data.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Where Legal Liability Starts After a Construction Data Breach
For a Sparks construction firm, the legal problem usually begins before anyone notices missing files or a lockout. It starts with weak account controls, inconsistent handling of bid documents, payroll records, vendor files, and project correspondence, then gets worse when nobody can clearly show who had access, what was exposed, and how quickly the business responded. In Nevada, saying the team did not realize the data was sensitive does not remove responsibility. If client data, employee records, or contract documents are lost or exposed, the business may face reporting duties, contract disputes, and questions about whether reasonable safeguards were in place.
We typically find that these incidents are not caused by one dramatic failure. They come from layered neglect: stale credentials, shared mailboxes, untracked file shares, weak password practices, and no tested incident workflow. That is why firms relying on managed IT support plans in Reno need more than basic help desk coverage. They need documented controls, access reviews, and clear response ownership. In cases like Russell’s, the technical issue and the legal issue arrive together because the business cannot quickly prove what happened or contain the spread.
- Access Governance: Former employees, temporary project staff, and shared admin accounts often remain active longer than they should, creating exposure across estimating systems, file servers, and cloud storage.
- Records Handling: Construction firms frequently move contracts, plans, change orders, and HR files between email, desktops, and shared folders without a retention standard or permission model.
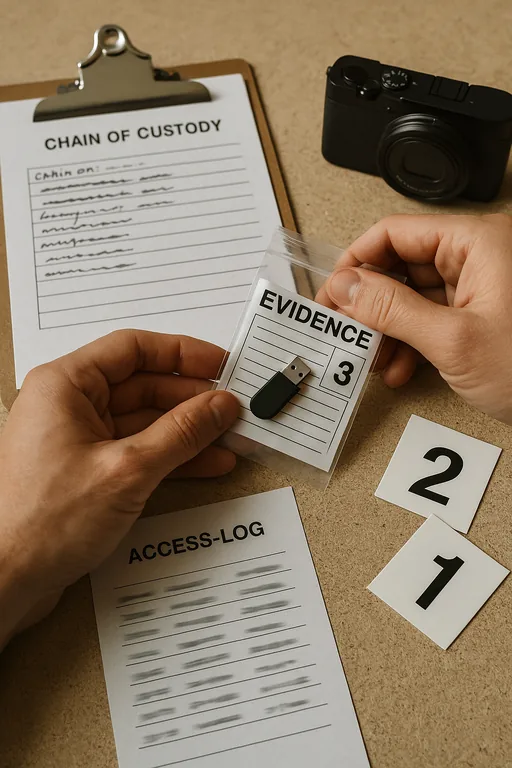
- Response Delay: When no one owns incident triage, the first hours are spent guessing instead of preserving logs, isolating systems, and determining whether notification obligations apply.
- Operational Consequence: Estimating, billing, scheduling, and subcontractor coordination slow down immediately, which turns a security event into a business continuity problem.
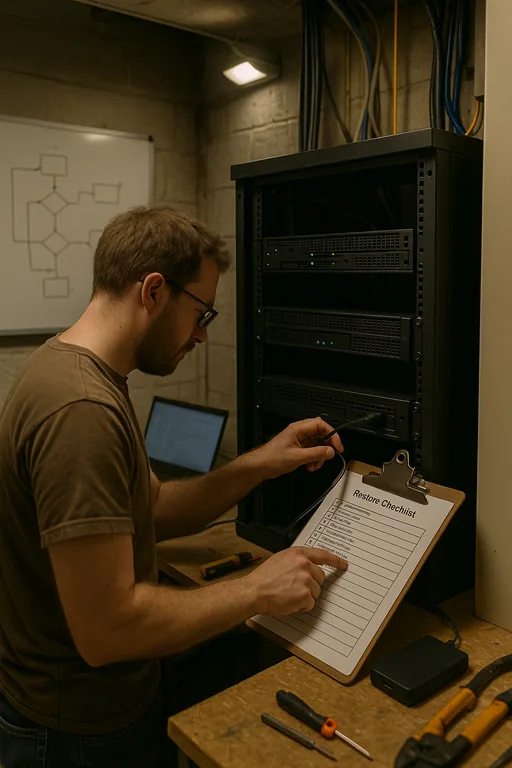
Practical Remediation for Security, Recovery, and Defensible Response
The fix is not a single product. It is a controlled process that reduces exposure and gives leadership a defensible record of what was done. Start by identifying where sensitive data actually lives: file shares, Microsoft 365, local desktops, accounting platforms, and project management systems. Then tighten identity controls with MFA, remove dormant accounts, restrict admin rights, and separate estimating, finance, and field operations access where practical. For firms with multiple trailers, offices, or jobsite connections, network segmentation and better logging matter just as much as endpoint protection.
Recovery also has to be provable. We recommend tested restore points, documented escalation steps, and preserved audit trails so the business can recover operations and answer legal questions with facts. That is where backup and recovery programs for business continuity become part of compliance, not just disaster recovery. For incident handling and reporting discipline, the CISA ransomware and incident response guidance is a practical baseline even when the event is not full ransomware.
- Identity Hardening: Enforce MFA on email, VPN, and cloud storage; disable stale accounts; and review privileged access monthly.
- Data Classification: Separate HR, financial, and contract records from general project files so exposure is easier to contain and assess.
- Backup Validation: Test restores for file shares, cloud data, and line-of-business systems instead of assuming backups are usable.
- Incident Workflow: Define who isolates devices, who contacts counsel or insurance, who reviews logs, and who handles client communication.
Field Evidence: Multi-Site Construction Operations Regain Control
We worked through a similar pattern with a Northern Nevada contractor operating between Sparks yard space, a Reno office, and active job sites where crews depended on shared drawings and accounting needed uninterrupted access to billing records. Before remediation, permissions had grown informally over time, backup status was assumed rather than tested, and there was no clean inventory of who could reach which folders. A single suspicious login created confusion because nobody could quickly determine whether the event was isolated or whether project and employee data had been copied.
After access cleanup, restore testing, and better oversight of file systems and cloud platforms through network, server, and cloud management , the business had a clear before-and-after change. Logs were retained, sensitive folders were segmented, and supervisors could escalate incidents without stopping the entire office. In practical terms, that meant fewer billing delays, faster containment, and a much stronger position if a customer, insurer, or attorney asked what controls were in place.
- Result: Administrative downtime during suspicious-access events dropped from most of a workday to under 90 minutes, and restore verification improved from untested to documented monthly checks.
Reference Table: Controls That Reduce Legal and Operational Exposure
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed It Support Plans and has spent his career building practical recovery, security, and operational continuity processes for businesses across Sparks, Reno, Carson City, and Northern Nevada and Northern Nevada.
Local Support in Sparks, Reno, Carson City, and Northern Nevada
Construction firms in Sparks often need fast on-site support because legal exposure and downtime rarely stay confined to one device or one office. From our Reno location, the Canal Street and industrial corridor areas are a short drive, which makes it practical to assess access issues, preserve evidence, and coordinate recovery steps without losing time between offices, yards, and field operations.
Construction Breach Response Has to Be Technical and Defensible
A data breach at a Sparks construction firm is not just an IT event. It is a records, operations, and legal liability issue that can affect contracts, payroll, billing, and client trust at the same time. The businesses that recover cleanly are usually the ones that can show where sensitive data lived, who had access, what controls were active, and how the response was documented.
That is the practical takeaway for Northern Nevada contractors: reduce exposure before the incident, and make sure recovery steps are tested before they are needed. When safeguards, backups, and access controls are aligned, the business is in a much better position to limit downtime and answer hard questions with evidence instead of assumptions.

