Security Policies & Documentation
Security policies and documentation define how a business controls access, handles data, responds to incidents, and proves those controls exist. When they are current, enforced, and reviewable, they support governance, compliance readiness, and fewer preventable failures.
At quarter-end, Alec L. inherited finance approvals after an office administrator left. The offboarding policy was outdated, delegated mailbox access stayed active, and altered vendor payment instructions triggered $59,400 in fraud loss, legal review, and emergency account remediation.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
As documented on Scott Morris‘s author page, Scott Morris is a managed IT and cybersecurity professional who helps businesses secure infrastructure, govern access, maintain documentation, recover from incidents, and keep daily operations stable. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Security Policies & Documentation because these controls only reduce risk when they are tied to real asset inventories, user lifecycle management, incident procedures, business continuity planning, and operational resilience in live business environments, including Reno and Sparks organizations that need secure, compliant, and recoverable systems.
This article explains common operational patterns and decision points, not a one-size-fits-all policy template. This is general technical information; specific network environments and compliance obligations change strategy.
Security policies set the rules for access, data handling, device use, incident reporting, vendor connectivity, retention, and approval authority. Documentation is broader: procedures, asset inventories, network diagrams, access review records, exception logs, and sign-off trails that show how those rules are implemented and who is accountable when something changes.
A common failure point is treating policy as a binder for audits rather than a control system for daily operations. In mature environments, policy statements line up with onboarding and offboarding checklists, privileged access approvals, security awareness steps, and the ticketing and change records maintained through managed IT services; when those links do not exist, documents age quietly while risk accumulates in live systems.
- Governance records: Policy owners, review dates, exception approvals, and acknowledgement tracking.
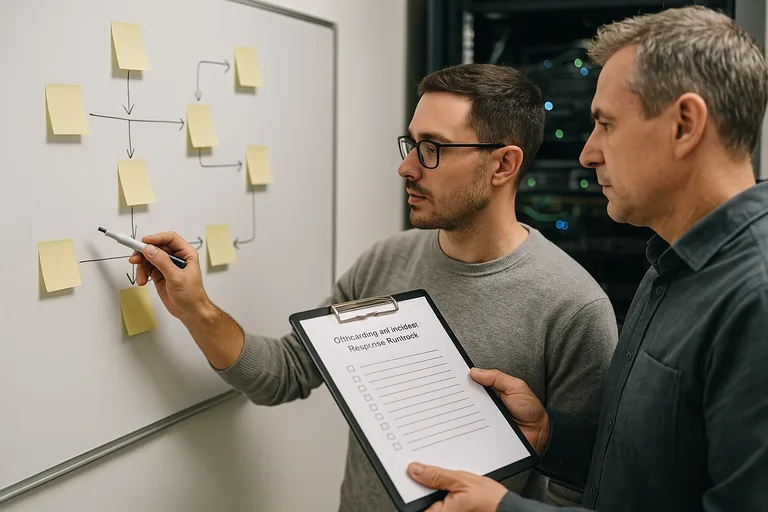
- Operational documents: Incident response playbooks, access provisioning procedures, vendor access rules, and change management steps.
- Evidence artifacts: Access review logs, training completion records, vulnerability findings, and documented corrective actions.
What are security policies and documentation in a business setting?
Policies state the rules. Standards define required baselines. Procedures explain how staff and IT follow the rule. Documentation captures the evidence that it happened. What usually separates a stable environment from a fragile one is that each document has an owner, scope, review cadence, approval history, and a clear connection to technical enforcement rather than existing as a disconnected file on a shared drive.
Why do they matter beyond a compliance binder?
They matter because most real business disruption starts with unclear responsibility, not a missing PDF. When a manager cannot tell who approved remote access, when a departing employee keeps mailbox delegation, or when an incident contact list is outdated, downtime and liability increase quickly. For Nevada businesses handling personal information, Nevada Revised Statutes NRS 603A matters because it expects reasonable security measures and breach response discipline. For medical practices, documentation tied to HIPAA security responsibilities is often what shows whether administrative safeguards actually exist or whether the office is relying on memory and informal habits.
What risks do they reduce when enforced properly?
Well-run policies and documentation reduce privilege creep, shared account use, unmanaged vendor access, inconsistent approval chains, missing security exceptions, and confusion during incidents. Guidance in NIST SP 800-63B matters here because authentication is not just a password setting; it is identity lifecycle management. In practice, documented joiner-mover-leaver procedures, multifactor enforcement, delegated access controls, and periodic access reviews reduce the chance that a stale account or hidden permission turns into unauthorized movement, payment fraud, or an avoidable audit problem.
How does this work in practice inside a real environment?
A competent program usually starts with policy ownership, version control, and a review schedule, then maps each rule to a procedure, system setting, and evidence source. During a routine access review, a sign-in alert may show a disabled employee account still sending mail through a legacy mobile profile; investigation often reveals that the offboarding checklist removed the main login but did not document delegated access, app passwords, or exception handling. The correction is operational, not cosmetic: update the identity procedure, tie it to ticket approvals and directory groups, and keep evidence such as access review logs, change records, and incident timelines consistent with guidance from CISA incident response training and guides, which exist because response quality depends on preparation, preserved evidence, and clear ownership before something goes wrong.
How can leadership tell whether implementation is competent?
- Ownership is visible: Each policy shows a business owner, technical owner, approval date, and next review date.
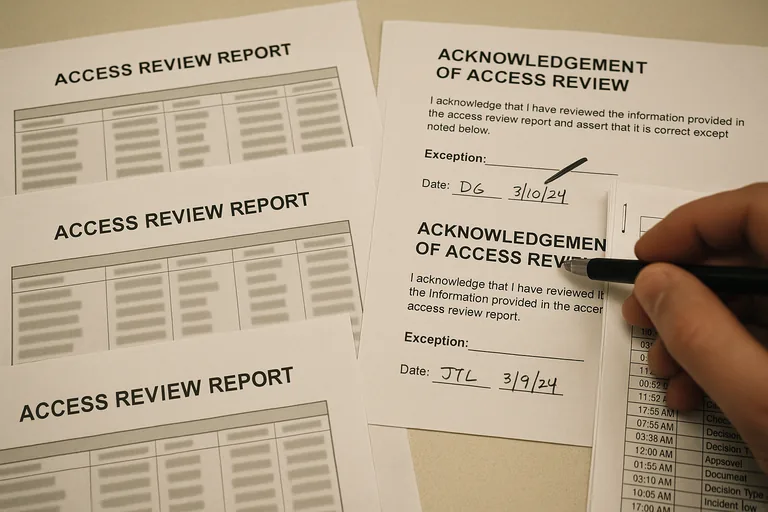
- Controls are provable: Access review reports, acknowledgement records, change tickets, and exception logs exist and can be produced without scrambling.
- Procedures match reality: Onboarding, offboarding, incident response, and vendor access steps match the actual tools and systems in use.
- Reviews have cadence: Leadership can see when privileged access, remote access, and policy exceptions were last reviewed and what was corrected.
When does weak documentation become dangerous?
What should happen next if the documentation is incomplete?
If your business would struggle to explain who approved delegated access, where exceptions are tracked, or how offboarding is verified, it is worth speaking with an experienced advisor before a documentation gap becomes the kind of fraud and emergency cleanup described at the start. A focused review now usually costs less than untangling access, accountability, and downtime after the fact.

