Risk Assessments & Security Readiness
Risk assessments and security readiness reviews show where a business is exposed before an outage, breach, or audit problem forces the issue. Done properly, they clarify priorities, strengthen planning, and improve resilience, accountability, and compliance preparation.
At quarter-end, Adeline B. discovered that an unreviewed Microsoft 365 admin account without enforced MFA had been used to create hidden mailbox rules and redirect payment conversations. The delayed risk assessment meant the exposure stayed open long enough to disrupt collections, trigger emergency remediation, and produce $52,500 in direct fraud, legal, and recovery costs.
The following situation represents a realistic incident pattern derived from real business IT environments. Identifying details have been changed to preserve confidentiality.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure stability, secure identities and endpoints, maintain recoverable systems, and reduce operational exposure before small gaps become expensive incidents. Scott Morris has 16+ years of managed IT and cybersecurity experience. His work is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience, including the realities of supporting Reno and Sparks business environments where uptime, accountability, and clear security ownership matter.
This is general technical information; specific network environments and compliance obligations change strategy. A formal assessment should account for your systems, vendors, data types, insurance conditions, and legal requirements.
The operational baseline usually starts with asset inventory, user accounts, privileged access, vendor access paths, cloud services, network dependencies, patch status, logging coverage, and recovery priorities. A common failure point is assuming those basics are already documented when the environment has changed for years without review. If a business is preparing for customer requirements, insurance questions, or audits, that same baseline often supports regulatory compliance support because auditors and insurers both ask for evidence, not assumptions.
Security readiness is the action side of the assessment. It turns findings into ownership, deadlines, testing, and exception handling so the organization is not relying on memory during an incident. In medical and adjacent service environments, this work often overlaps with HIPAA security requirements because access control, device management, incident handling, and documentation are operational safeguards long before they become compliance paperwork.
What does a risk assessment actually cover?
A competent assessment examines business processes, data sensitivity, user identities, administrative privileges, external access, vendor dependencies, endpoint posture, email security, logging, and recovery capability. A common failure point is treating the exercise as a vulnerability scan alone. Scans can identify missing patches, but they do not explain whether shared admin credentials exist, whether former staff accounts were removed properly, or whether a line-of-business application depends on an undocumented server that nobody planned to replace.
Why does security readiness matter to operations?
Security readiness matters because most business disruption starts as an ordinary operational gap: an account without MFA, a server with weak ownership, a vendor connection nobody reevaluated, or a policy that exists in a binder but not in active enforcement. What usually separates a stable environment from a fragile one is whether response roles, recovery priorities, and control ownership were defined before a pressure event. When they are not, the cost shows up as downtime, payment delays, overtime, emergency consulting, customer confidence issues, and slower decisions when leadership needs clarity fast.
Which risks are commonly missed until something breaks?
In environments that have not been reviewed recently, stale service accounts, inherited admin rights, undocumented remote access, disabled logging, and unsupported network devices are frequently missed because each item appears to belong to someone else. During one routine review, repeated failed sign-in attempts from a copier account led investigators to an old SMTP credential that still had mailbox permissions and no named owner. The deeper issue was not the copier; it was that identity lifecycle controls had never been applied to service accounts, which left a blind spot that normal helpdesk activity would not have caught.
How does a competent readiness process work in practice?
In mature environments, the work usually moves in a sequence: confirm assets and business dependencies, review identity and privilege assignments, check external exposure, examine patch and endpoint policy enforcement, validate logging and alert paths, and then compare the findings against business impact. A competent provider should be able to explain which systems are in scope, who approved exceptions, and how high-risk findings will be remediated or accepted. Guidance from NIST SP 800-63B matters here because authentication strength and account lifecycle management directly affect whether a stolen password becomes a contained event or a broader compromise.
What evidence shows controls are really working?
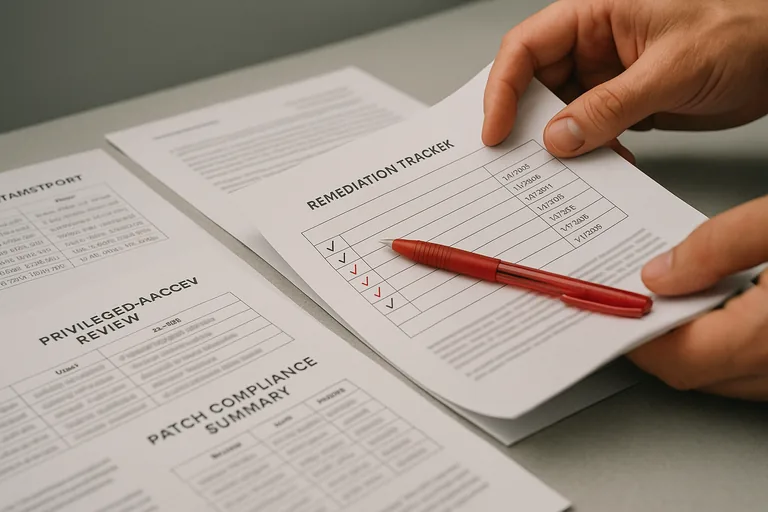
Real evidence looks like current asset inventories, privileged access review logs, MFA enrollment reports, patch compliance summaries, vulnerability scan results with remediation dates, alert escalation records, and documented exception registers showing who accepted residual risk and why. In practice, the issue is rarely the tool alone; it is the process around it. For Nevada businesses handling personal information, Nevada Revised Statutes NRS 603A is relevant because reasonable security is much easier to defend when the organization can show that controls were reviewed, enforced, and tracked over time rather than assumed to be working.
What warning signs suggest the assessment was superficial?
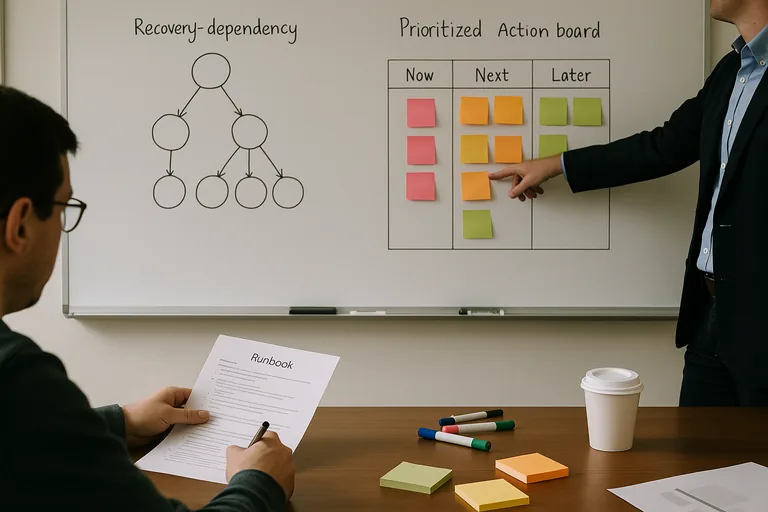
What should leadership do after the findings are delivered?
Leadership should convert the findings into a prioritized action plan tied to business processes, not just technical categories. That means assigning owners, funding deadlines, validating compensating controls, scheduling retesting, and documenting which risks are being accepted temporarily so they do not disappear into email threads. A useful readiness program is repeatable: it is revisited after major system changes, staffing changes, office moves, mergers, compliance pressure, or any incident that reveals a gap in how the environment is actually operated.

