Risk Assessments
Risk assessments help business leaders identify operational weaknesses before they turn into outages, fraud, compliance issues, or expensive cleanup. The real value is understanding what must be protected, what is most likely to fail, and what actions reduce exposure first.
At a 28-user distributor, Albert B. came in Monday to find the controller’s email account had been abused after password-spray attempts hit an old exposed login path that no risk assessment had flagged. Vendor banking details were changed, invoices were rerouted, and the company spent $59,000 on loss recovery, legal review, and emergency containment.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage secure infrastructure, maintain stable systems, reduce operational risk, and improve recovery readiness when outages or security failures occur. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Risk Assessments because competent reviews connect technical weaknesses to business continuity, secure infrastructure management, documentation quality, and operational resilience in the real business environments that Reno and Sparks organizations rely on every day.
This article explains common operational patterns, decision points, and verification practices, not legal advice or a substitute for a formal engagement. This is general technical information; specific network environments and compliance obligations change strategy.
A risk assessment is a structured review of how technology, people, vendors, and business processes can fail or be abused, and what that failure would cost the business. In mature environments, it is tied to asset inventory, business priorities, and ongoing managed IT oversight so the result is a remediation plan with ownership and dates, not a report that gets filed away.
- Scope: Identify the systems, data, vendors, locations, remote access paths, and business workflows that matter.
- Weaknesses: Review unsupported software, excessive access, logging gaps, single points of failure, and cloud or vendor exposure.
- Impact: Estimate downtime, revenue interruption, privacy exposure, contractual consequences, and recovery complexity.
- Treatment: Decide whether each risk should be fixed, reduced, transferred, or accepted with documented ownership and review dates.
Not every business has the same legal trigger, but many have practical, contractual, or regulatory reasons to perform assessments. Healthcare organizations handling ePHI are expected to perform risk analysis under the HHS HIPAA Security Rule, and Nevada businesses storing personal information should understand the reasonable security obligations in Nevada Revised Statutes NRS 603A. For medical offices, this usually supports broader HIPAA security planning, cyber-insurance requirements, vendor due diligence, and executive decisions about downtime tolerance.
What is a risk assessment in a business IT environment?
In business IT, a risk assessment is not just a vulnerability scan and not just a compliance form. It identifies what systems and data matter, how they could be disrupted or exposed, how likely that is, what controls already exist, and where the remaining risk still sits after those controls are considered. A common failure point is treating every finding as equally important; experienced teams rank issues by business impact so identity systems, finance workflows, line-of-business applications, and regulated data receive attention before low-value nuisance items.
Why do risk assessments matter beyond compliance?
The operational value is visibility. What usually separates a stable environment from a fragile one is not the software brand list; it is whether leadership knows which weaknesses can stop billing, scheduling, production, funds movement, or customer communication. Businesses that run structured managed IT services often have cleaner inventories, clearer system ownership, and faster remediation because risks are tied to named people, deadlines, and change control instead of informal habits. That usually improves budgeting, cyber-insurance readiness, and response speed when something abnormal happens.
What risks can a competent assessment reduce?
A competent assessment can reduce several expensive failure modes: stale administrator accounts that create unauthorized access risk, unsupported network equipment that leaves the perimeter exposed, undocumented SaaS platforms that hold business data with no retention plan, and single points of failure in internet, storage, or line-of-business systems. In practice, the issue is rarely the tool alone; it is the process around it. If patching exists but exceptions are never reviewed, or MFA exists but not for every privileged account, the business may believe it is protected while the real exposure remains.
How does a risk assessment work in practice?
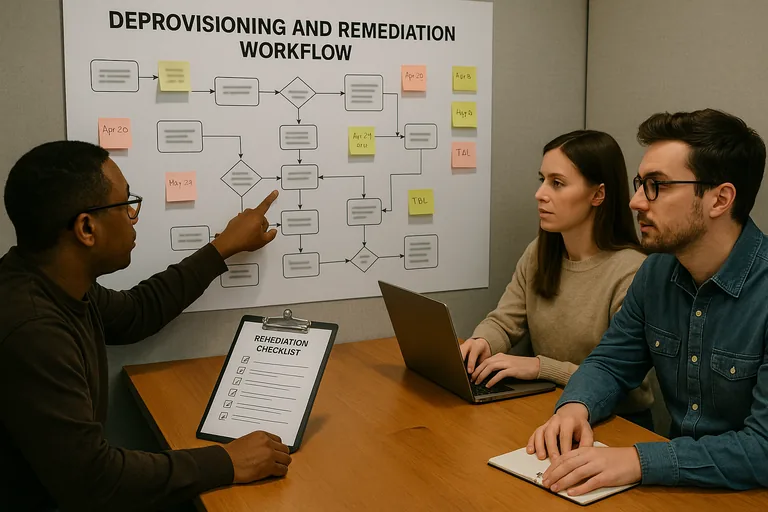
In practice, the work starts with scope, asset inventory, identity review, business process interviews, and a check of existing controls such as patching, endpoint protection, backup status, logging, and vendor access. The reason experienced teams borrow structure from the NIST Cybersecurity Framework is that it pushes the discussion beyond prevention and into detection, response, and recovery, which is where many losses become operationally expensive. During one routine review pattern, repeated failed logins against a dormant VPN group led to a deeper check and revealed three former contractors still had enabled accounts because offboarding depended on email requests rather than a documented access review; the lasting fix was clear ownership, review cadence, and verifiable deprovisioning records.
What evidence shows a risk assessment is being done competently?
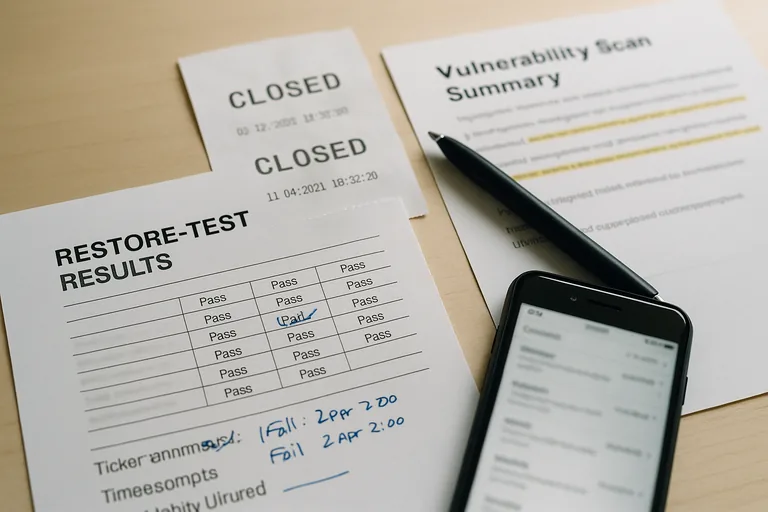
A mature risk assessment should produce evidence a business owner can inspect: an asset inventory with owners, a current list of privileged accounts, vulnerability scan summaries, remediation priorities, documented exceptions, and review dates for unresolved issues. If the assessment says backups reduce risk, there should also be restore test results and recovery sequence notes; if it says access is controlled, there should be access review logs and termination procedures. When none of that exists, the assessment is often interview-driven and optimistic rather than operationally proven.
How do you verify that assessment findings are actually fixed?
When should a business update or repeat a risk assessment?
If the last assessment predates a major cloud migration, remote work expansion, merger, insurance renewal, payment workflow change, healthcare system rollout, or serious security event, it is probably too old to trust. In environments that have not been reviewed recently, one of the first things experienced IT teams check is whether the documented risk picture still matches the actual network, users, vendors, and data flows. A practical next step is to rescope the environment, assign ownership for findings, rank issues by business impact, and review the assessment on a cadence that matches operational change rather than waiting for an incident to do the prioritizing.

