Reno’s Hidden Threat
Seeing encrypted files is often the visible symptom of hidden threats, not the root problem itself. In manufacturing plants across Reno, issues like stolen credentials, MFA gaps, and weak monitoring can quietly undermine identity email and user security until work stops or risk spikes. The fix usually starts with hardening identity, watching for abnormal behavior, and closing blind spots across users and devices.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Encrypted Files Usually Point to an Identity Security Failure
When a Reno manufacturing plant suddenly sees encrypted files, the visible damage is often only the last stage of the incident. The more important question is how the attacker gained trusted access in the first place. In many cases, modern attackers do not force their way through the perimeter. They sign in with stolen usernames, reused passwords, or session tokens, then move through email, cloud storage, remote access tools, and local file shares as if they belong there.
That is the invisible threat gap. A plant may have a solid firewall, endpoint antivirus, and backup appliance, but still lack the controls needed to detect suspicious logins, impossible travel, MFA fatigue attempts, mailbox rule abuse, or unusual file access patterns. That is why businesses reviewing identity email and user security in Reno often find that the real weakness is not the server room. It is the trust placed in user accounts that are not being monitored closely enough. In manufacturing environments, where ERP access, vendor communication, CAD files, and production schedules all depend on user identity, one compromised account can interrupt operations quickly. We see this especially in multi-shift facilities around Reno and Sparks where shared systems stay active long after normal office hours. In a case like Jorge’s, encrypted files were the symptom; the root cause was a valid account being used in an invalid way.
- Credential misuse: A stolen or phished account can access email, file shares, and cloud apps without triggering traditional perimeter defenses.
- MFA weakness: MFA that is missing, inconsistently enforced, or vulnerable to push fatigue leaves identity systems exposed even when passwords are changed regularly.
- Monitoring blind spots: Without alerting on abnormal sign-ins, mailbox changes, privilege escalation, or mass file activity, attackers can operate quietly before encryption begins.
- Manufacturing dependency: Shared production documents, purchasing records, and scheduling systems create a broad blast radius when one user account is compromised.
Practical Remediation for Manufacturing Identity and File Risk
The right response is not limited to restoring files. Recovery has to include identity containment, evidence review, and control hardening. We typically start by isolating affected endpoints, disabling or resetting exposed accounts, revoking active sessions, reviewing mailbox rules, and validating whether the attacker touched cloud applications in addition to local systems. From there, the focus shifts to reducing the chance of the same login path being used again.
For manufacturing plants, that means enforcing phishing-resistant or at least hardened MFA, tightening conditional access, separating admin roles from daily user accounts, and validating backup recovery against real production data sets. It also helps to run structured security readiness reviews for Reno operations so hidden gaps are found before they become downtime. CISA provides a practical baseline for this work in its guidance on multi-factor authentication , especially for organizations trying to reduce account takeover risk without disrupting daily operations.
- Identity containment: Reset compromised credentials, revoke tokens, and review sign-in logs before restoring normal access.
- MFA hardening: Require MFA across email, VPN, cloud apps, and privileged accounts, with number matching or stronger methods where possible.
- Endpoint and EDR review: Confirm whether encryption activity came from one device or lateral movement across multiple systems.
- Backup validation: Test file recovery against current production folders, not just backup job success messages.
- Alerting improvements: Trigger notifications for impossible travel, repeated failed MFA prompts, mass file changes, and suspicious mailbox rules.
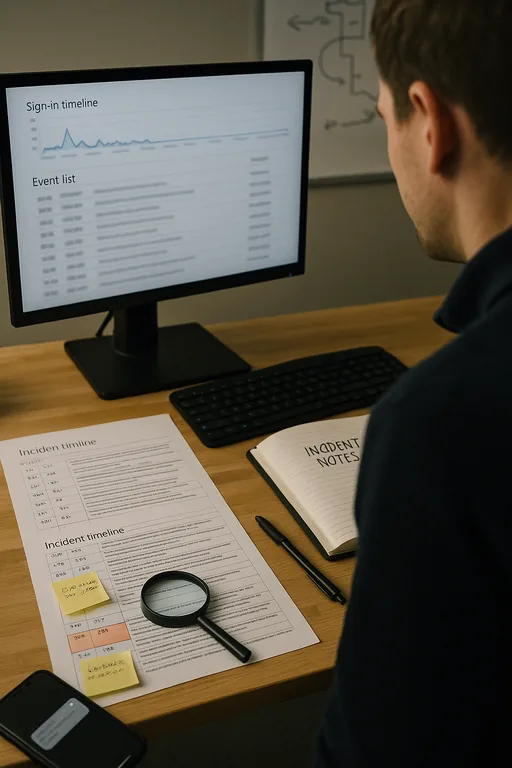
Field Evidence: Hidden Login Activity Before File Encryption
In one Northern Nevada manufacturing environment, the initial complaint was simple: shared folders would not open and several file names had changed overnight. The first review showed no obvious firewall breach and no major server outage. After tracing sign-in history, however, we found repeated access to cloud email from an unfamiliar location, followed by successful authentication to a user account that had broad access to production documentation. The account had been active outside normal shift patterns, but no one was watching for that behavior.
After containment, the business moved to stricter identity controls, segmented access to sensitive file shares, and formalized account review procedures tied to shift-based operations. In facilities along the Reno industrial corridors, where production, shipping, and office systems overlap, that governance layer matters as much as the technical stack. It is also where compliance-focused IT management helps turn one-off fixes into repeatable operating discipline. As a result, Jorge’s type of disruption becomes far less likely because abnormal access is identified earlier and user permissions are no longer left overly broad.
- Result: Recovery time dropped from a full business day of uncertainty to under 3 hours for account containment and prioritized file restoration, with measurable reduction in unauthorized after-hours access alerts.
Reference Table: Common Controls for the Invisible Threat Gap
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Identity Email And User Security and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno and Northern Nevada.
Local Support in Reno
We support manufacturers and other operationally sensitive businesses across Reno, Sparks, Carson City, and nearby sites where travel time matters during an incident. For locations near St. James Village, response planning has to account for both technical containment and the practical realities of getting the right people on site quickly when file access, identity systems, or production workflows are affected.
Closing the Gap Before Encryption Starts
Encrypted files in a Reno manufacturing plant usually mean the real failure happened earlier, at the identity layer. If attackers can log in with a trusted account, they can often reach email, cloud services, shared folders, and operational documents before anyone notices. That is why the most effective response combines recovery with account review, MFA hardening, endpoint visibility, and better alerting around abnormal user behavior.
For plant operators, the practical takeaway is straightforward: do not treat file encryption as only a backup problem. It is often an access-control and monitoring problem first. When identity, email, and user activity are governed properly, the business has a much better chance of catching the threat before production, scheduling, and billing are affected.

