Reno/Sparks Network Crash
What looks like a one-off issue is often tied to compliance gaps. In financial office environments, missing controls, weak documentation, and loose access policies can turn into audit findings, fines, and operational disruption long before anyone notices the warning signs. Closing those gaps early makes network server and cloud management far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Compliance Gaps Trigger Network Failures in Financial Offices
A network crash in a financial office is often not caused by a single bad switch, server fault, or cloud sync error. More often, the underlying issue is a compliance gap: access rights that were never reviewed, change logs that were never maintained, backup jobs that were assumed to be working, or policy requirements that changed faster than internal IT documentation. In Washoe County, we see this most often in offices that handle regulated financial records but still rely on informal processes for account control and system oversight.
That matters because compliance is operational, not just administrative. When a financial office lacks documented controls, routine changes become risky. A firewall update can interrupt line-of-business traffic. A server patch can expose old privilege assignments. A cloud identity change can lock out staff who need immediate access to client records. Businesses that depend on network server and cloud management in Washoe County need those controls tied directly to uptime, audit readiness, and recovery planning. In cases like Eddie’s, the visible outage is only the symptom; the real failure is that no one had a current, tested record of who had access, what changed, and how to roll back safely.
- Access governance: Loose permissions, inactive accounts, and undocumented admin rights create both compliance exposure and a higher chance of service interruption during routine changes.
- Documentation drift: Regulations such as HIPAA and CMMC evolve faster than many internal teams update diagrams, policies, and recovery procedures.
- Backup assumptions: A backup that exists but has not been validated against current workloads may not support a clean recovery when a server or cloud platform fails.
- Change control weakness: Financial offices with small teams often make urgent fixes without approval tracking, rollback planning, or post-change verification.
Practical Remediation for Stability, Audit Readiness, and Recovery
The fix is not a single appliance or one policy memo. The right response is to bring compliance controls into daily operations. That starts with a current asset inventory, role-based access review, documented change management, and backup validation tied to actual recovery objectives. For financial offices in Reno, Sparks, and broader Washoe County, we typically prioritize the systems that affect billing, document retention, identity management, and secure remote access first.
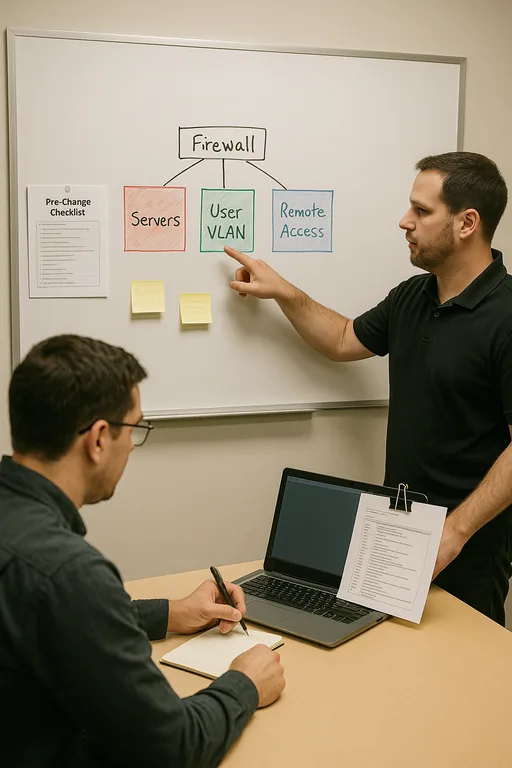
From there, the environment should be segmented and monitored so one failure does not spread across the office. That may include VLAN separation for workstations and servers, MFA hardening for privileged accounts, alerting on failed backup jobs, and tighter oversight through network infrastructure management for regulated offices . For control alignment, the CISA Cybersecurity Performance Goals provide a practical baseline for access control, logging, recovery, and resilience without turning the process into paperwork for its own sake.
- Identity review: Remove stale accounts, enforce MFA, and limit administrative access to named roles with documented approval.
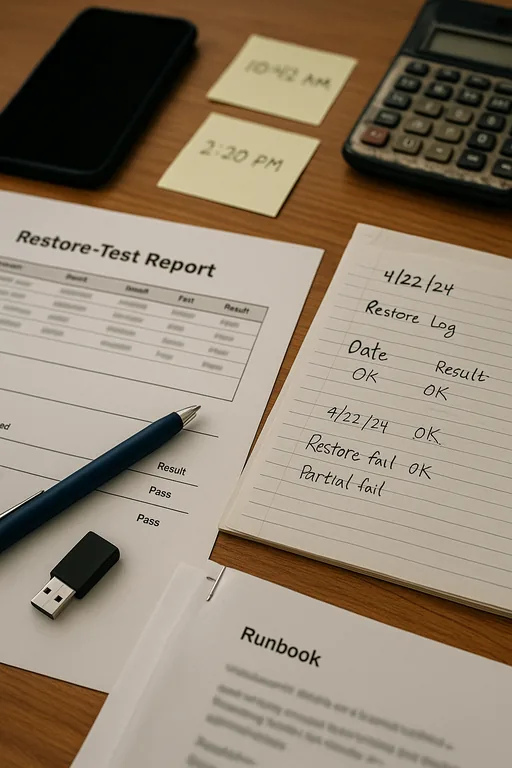
- Backup validation: Test restores against production data sets and confirm recovery time objectives for financial applications and file shares.
- Network segmentation: Separate critical servers, user devices, and remote access paths to reduce outage spread and simplify troubleshooting.
- Change control: Require pre-change documentation, rollback steps, and post-change verification for server, firewall, and cloud policy updates.
Field Evidence: From Audit Exposure to Controlled Recovery
We recently assessed a regulated office environment serving clients across Reno and north Washoe County where intermittent outages had been blamed on the ISP and aging hardware. The deeper issue was a mismatch between documented policy and actual system state. Admin rights had expanded over time, cloud file permissions no longer matched employee roles, and backup retention settings had changed without review. During a routine maintenance window, those gaps caused application failures and delayed access to shared records.
After rebuilding the access model, validating restore points, and standardizing hybrid server oversight through server and hybrid infrastructure management , the office moved from reactive troubleshooting to controlled operations. In a region where weather events, construction-related service interruptions, and multi-site travel between Reno and outlying areas can already complicate response time, that discipline matters.
- Result: Unplanned downtime dropped from repeated monthly interruptions to zero critical outages over the following quarter, and backup restore testing completed successfully within the office’s four-hour recovery target.
Compliance Controls That Reduce Network Crash Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Network Server And Cloud Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.
Local Support in Washoe County
Reno Computer Services supports financial offices across Reno, Sparks, Stead, and surrounding Washoe County locations where response planning has to account for both compliance requirements and practical travel realities. From our Ryland Street office, the Stead area is typically about 25 minutes away under normal conditions, which is why documented remote recovery procedures, tested backups, and stable network administration matter just as much as on-site support.
Closing the Compliance Gap Before It Becomes Downtime
For financial offices in Washoe County, a network crash is often the final stage of a longer control failure. Missing documentation, weak access discipline, and untested recovery processes create the conditions for outages, audit findings, and delayed client work. The earlier those gaps are identified, the easier it is to protect both uptime and compliance posture.
The practical takeaway is straightforward: treat compliance controls as part of infrastructure management, not as a separate paperwork exercise. When access, backups, network changes, and cloud administration are documented and tested together, the environment becomes more stable, easier to recover, and far less likely to fail at the worst possible time.

