Reno/Sparks Network Crash
The outage or lockout is usually the last symptom to appear, not the first. Unclear ownership, overlapping tools, and fragmented support create weak points that can disrupt disaster recovery planning and recovery and put response time, accountability, and outage recovery at risk. Reducing that risk starts with clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Vendor Chaos Turns a Network Crash Into a Recovery Problem
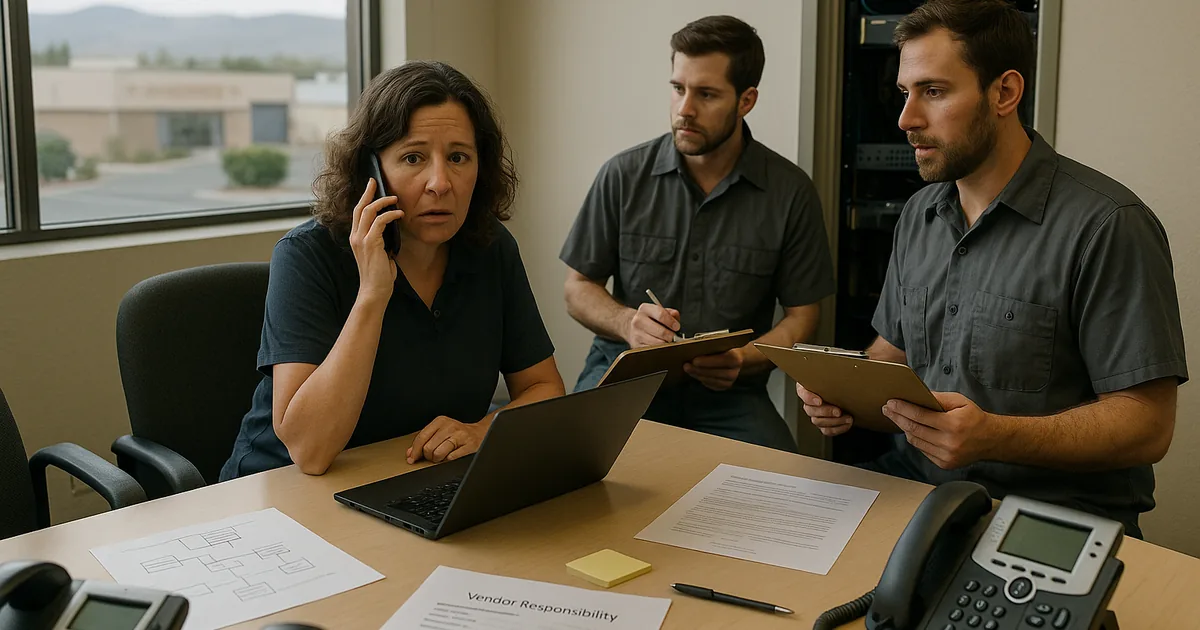
When a financial office in Sparks loses network access, the technical failure is only part of the issue. The larger problem is usually ownership. We often find that internet, phones, software, workstations, firewall management, and backup systems are split across multiple vendors with no single party accountable for incident command. That structure slows diagnosis, weakens documentation, and leaves the office manager doing coordination work that should already be mapped out in a recovery plan.
This is why disaster recovery planning and recovery in Northern Nevada has to include vendor governance, not just backup software and restore steps. In financial offices around Sparks and Reno, outages rarely stay isolated. A switch failure can interrupt cloud access, a firewall rule change can break remote sessions, and a voice outage can stop client communication at the same time. In Frances’s case, the visible crash was the last symptom. The real failure was that no one had a clean escalation tree, current network documentation, or authority to coordinate all vendors under one response process.
- Technical factor: Overlapping vendor responsibility creates delayed triage, duplicate tooling, inconsistent monitoring, and longer recovery windows when internet, phones, endpoints, and line-of-business systems fail together.
- Operational factor: Financial staff cannot process client requests, complete reconciliations, or maintain normal communication when shared systems and voice services go down at the same time.
- Local factor: In Sparks business parks and multi-tenant office environments, carrier handoff points, aging cabling, and undocumented network changes can make root-cause isolation slower unless one team owns the full incident path.
How to Clean Up Ownership, Escalation, and Technical Controls
The practical fix is to reduce ambiguity before the next outage. That starts with a current network diagram, a vendor responsibility matrix, named escalation contacts, and a tested incident workflow that defines who owns internet, firewall, switching, wireless, voice, endpoint response, and backup validation. Offices that rely on several outside providers usually benefit from one coordinating technical lead who can direct troubleshooting instead of waiting for each vendor to defend its own scope.
We also recommend pairing recovery planning with layered security and endpoint visibility. Financial firms handling sensitive records should align response procedures with cybersecurity services in Washoe County so a crash is not mistaken for a simple connectivity issue when the real cause is malicious activity, credential misuse, or unauthorized software behavior. Guidance from CISA is useful here because it ties incident response, backup readiness, and containment into one operational model instead of treating them as separate projects.
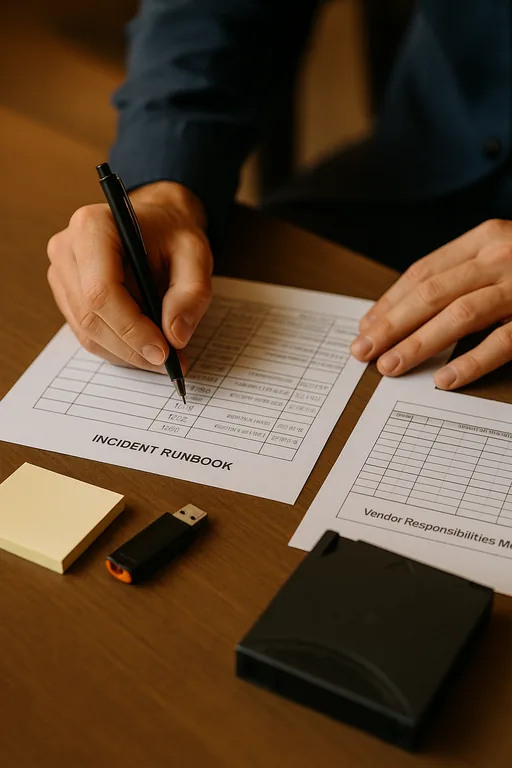
- Control step: Build a single escalation runbook with vendor contacts, asset ownership, carrier circuit details, firewall access procedures, and recovery priorities by business function.
- Control step: Validate backups against actual restore objectives, not just successful job reports, so file access and application recovery can be measured under time pressure.
- Control step: Standardize monitoring and alerting across firewall, switch, ISP handoff, and cloud application dependencies to reduce finger-pointing during outages.
- Control step: Apply MFA hardening, EDR, and change control so a network crash caused by endpoint compromise is identified quickly instead of being treated as a generic service interruption.
Field Evidence: Multi-Vendor Failure in a Sparks Financial Corridor
We reviewed a similar environment supporting a small financial office near the Sparks industrial and business corridor where internet, hosted voice, workstations, and a cloud accounting platform were all managed by different providers. Before cleanup, the office had no current network map, no tested failover procedure, and no agreement on who could authorize emergency changes. During incidents, staff opened separate tickets with each vendor and waited for callbacks while client-facing work stalled.
After consolidating documentation, assigning a primary incident owner, and adding endpoint and threat protection for business systems , the office moved from reactive vendor chasing to controlled response. The next service interruption was isolated to a failed edge device within minutes, temporary connectivity was restored through a documented workaround, and billing operations resumed the same morning despite a regional service disruption affecting nearby tenants.
- Result: Initial fault isolation dropped from roughly 90 minutes to under 15 minutes, and the office restored core access without a full-day shutdown.
Operational Controls for Vendor-Driven Outage Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Disaster Recovery Planning And Recovery and has spent his career building practical recovery, security, and operational continuity processes for businesses across Sparks, Reno, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in Sparks and Northern Nevada
Financial offices in Sparks often depend on a mix of internet, voice, cloud software, and endpoint vendors that were added over time rather than designed as one operating model. From our Reno office, the route to the Viking Way area is typically manageable, but travel time is only one part of response. The bigger advantage is having documentation, escalation ownership, and recovery priorities already defined before a crash forces everyone into reactive troubleshooting.
Clear Ownership Shortens Recovery Time
A network crash in a Sparks financial office is rarely just a hardware event. More often, it exposes weak ownership, fragmented vendor management, and recovery plans that were never built around real operating conditions. When no one controls the full escalation path, downtime lasts longer, staff productivity drops, and client-facing work backs up quickly.
The practical takeaway is straightforward: document the environment, define who owns each system, test recovery steps, and make sure security, endpoint visibility, and vendor coordination are part of the same operating plan. That is how offices reduce confusion, restore service faster, and keep a technical incident from turning into a business disruption.

