Reno/Sparks Lockout
The outage or lockout is usually the last symptom to appear, not the first. Poor safeguards, inconsistent records handling, and a slow response create weak points that can disrupt identity email and user security and put legal exposure, reporting obligations, and client trust at risk. Reducing that risk starts with documenting safeguards, tightening response steps, and protecting sensitive data.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why A Lockout Becomes A Legal Liability Issue
For a medical practice in Sparks, a lockout is rarely just a password problem. It usually points to a broader control failure involving identity management, email security, access logging, records retention, and response discipline. When those controls are weak, the business impact moves beyond downtime and into legal liability. If protected information is exposed, mishandled, or becomes unavailable during care delivery, the practice may face reporting obligations, billing disruption, and difficult questions about whether reasonable safeguards were in place.
We see this pattern often in smaller healthcare environments across Sparks and Reno where systems have grown over time without a clear owner. One office may rely on shared mailboxes, inconsistent onboarding, and old user accounts that were never fully removed. Another may have cloud access enabled but no documented approval process for who can reach patient-related data from home or from mobile devices. That is where identity email and user security in Northern Nevada becomes central to risk reduction. The legal issue is not only that access failed. It is that the practice may not be able to show who had access, when controls changed, or whether the response was timely and documented. As the local discussion often goes, if client data is lost, saying you did not know is not a legal defense in a Reno court.
- Identity control gaps: Disabled accounts left active, weak password reset procedures, and missing multifactor enforcement can trigger lockouts, unauthorized access, and incomplete audit trails.
- Records handling inconsistency: Patient files, referral documents, and billing attachments stored across email, desktops, and cloud folders create uncertainty about where sensitive data resides.
- Slow incident response: Delayed escalation means staff improvise, use personal devices, or bypass normal workflows, which increases exposure and weakens defensibility later.
- Operational pressure: In a busy Sparks clinic, front-desk teams cannot wait long for restored access, so the temptation to use workarounds rises quickly.
Practical Remediation For Access, Auditability, And Continuity
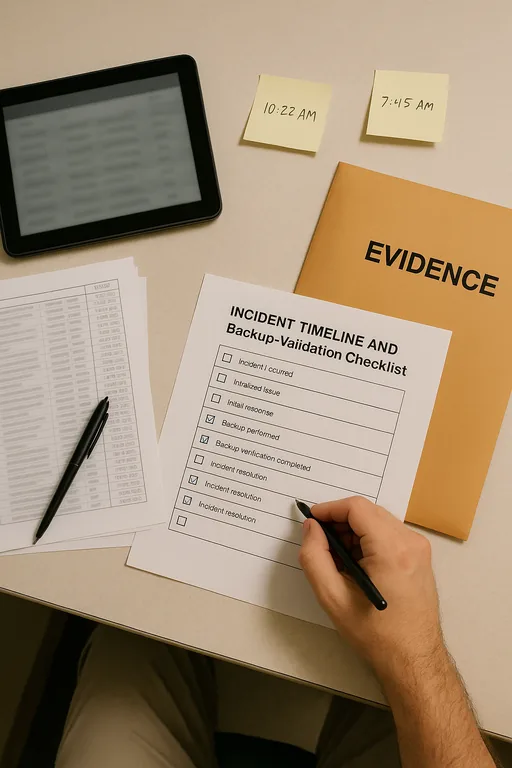
The fix starts with treating the lockout as a control review, not just a help desk ticket. First, confirm whether the event was caused by credential abuse, a sync failure, a mail security policy conflict, or an infrastructure issue between on-premise systems and cloud services. Then document the timeline, affected users, systems touched, and any patient or billing workflows interrupted. For medical offices with mixed local servers and cloud applications, stronger server and hybrid infrastructure management helps reduce the gray area where authentication, file access, and application dependencies break down.
From there, the practice should tighten account lifecycle management, require MFA for all privileged and remote access, validate backup access to critical records, and test emergency workflows for scheduling and intake. If Microsoft 365 is involved, mailbox auditing, conditional access, and sign-in review should be part of the standard response. The CISA guidance on multifactor authentication is a practical baseline because it addresses one of the most common root causes behind account compromise and lockout events.
- MFA hardening: Require multifactor authentication for email, EHR-adjacent systems, VPN, and admin accounts, with exceptions removed unless formally approved.
- Audit logging: Retain sign-in, mailbox, and file access logs long enough to support legal review and incident reconstruction.
- Backup validation: Test restoration of scheduling, billing, and document repositories so availability failures do not become records failures.
- Response playbooks: Define who isolates accounts, who contacts legal or compliance leadership, and how patient-facing operations continue during an outage.
Field Evidence: From Account Failure To Defensible Operations
In one Northern Nevada healthcare environment, the initial condition looked familiar: repeated account lockouts, shared inbox confusion, and no reliable way to confirm whether a failed login was user error or malicious activity. The office was operating between a local line-of-business server and Microsoft 365, with inconsistent permissions and no tested fallback for intake documents. During a busy weekday, staff lost access to scheduling and secure communications just as referrals were arriving from outside providers.
After the environment was cleaned up, the practice had documented access roles, enforced MFA, mailbox auditing, and clearer separation between local infrastructure and cloud workloads. We also see better stability when organizations align those cloud controls with Microsoft environment management for regulated offices instead of letting permissions drift over time. In this case, the office moved from reactive lockout recovery to a process that could show what happened, who was affected, and how operations were restored. That matters in Sparks and Reno where multi-site referrals, weather disruptions, and limited administrative slack can magnify even a short outage.
- Result: Unplanned access interruptions dropped by 70 percent over the following two quarters, and the office reduced same-day scheduling delays from several hours to under 30 minutes during tested recovery events.
Reference Points For Medical Practice Access And Liability Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Identity Email And User Security and has spent his career building practical recovery, security, and operational continuity processes for businesses across Sparks, Reno, and Northern Nevada and Northern Nevada.

Local Support in Sparks, Reno, and Northern Nevada
Medical offices in Sparks often depend on a mix of cloud identity tools, local network equipment, and older line-of-business systems that do not fail gracefully. From our Reno location, the Virginia Foothills area is typically about 21 minutes away under normal traffic, which matters when a practice needs on-site verification of access, devices, and records workflows rather than another round of remote guesswork.
Operational Takeaway For Sparks Medical Practices
A medical practice lockout becomes a legal liability issue when the organization cannot show that access was controlled, records were handled consistently, and the response was documented. The outage is only the visible event. The real exposure sits underneath it in weak identity controls, unclear ownership, and missing evidence.
For practices in Sparks, the practical path forward is straightforward: tighten identity and email controls, document records workflows, test recovery steps, and make sure cloud and local systems are being managed as one environment. That reduces downtime, improves defensibility, and gives leadership a clearer answer when auditors, insurers, or counsel ask what happened.

