Reno/Sparks Law Firm Audit
The outage or lockout is usually the last symptom to appear, not the first. Poor safeguards, inconsistent records handling, and a slow response create weak points that can disrupt backup and recovery programs and put legal exposure, reporting obligations, and client trust at risk. Reducing that risk starts with documenting safeguards, tightening response steps, and protecting sensitive data.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why a System Outage Becomes a Legal Liability Problem
When a law firm in Sparks or Reno has systems down, the immediate problem is lost access. The larger problem is legal liability. If client records cannot be located, restored, or verified, the firm is no longer dealing with a simple IT interruption. It is dealing with chain-of-custody questions, missed deadlines, incomplete production, and potential reporting obligations. In Nevada, saying the firm did not know a safeguard was missing does not carry much weight once client data is affected.
We typically find that the outage is only the visible failure. Underneath it are weak retention practices, inconsistent folder permissions, untested restores, and no documented incident sequence for who does what first. That is why firms relying on backup and recovery programs in Northern Nevada need more than a backup job that says it completed. They need recoverability, auditability, and a clear record of what was protected, when it was protected, and how quickly it can be restored. In the Lakeridge incident, Bruce was not dealing with one broken system; she was dealing with a process failure that had been hidden until access stopped.
- Records governance: Legal files stored across email, local shares, and cloud folders create inconsistent retention and restoration points.
- Recovery validation: Backups that are never tested often fail at the exact moment a firm needs a clean restore for pleadings, discovery, or billing records.
- Response timing: A slow first hour increases downtime, expands staff idle time, and raises the chance of missed court, client, or insurer notification requirements.
- Access control drift: Permission changes made over time can lock out staff, expose confidential files, or break application dependencies without warning.
What a Law Firm Should Fix Before the Next Lockout
The practical fix is not a single tool. It is an operating model. Firms need documented data locations, defined retention rules, tested restore points, and a response plan that assigns ownership to legal operations, firm leadership, and technical support. For most offices, that means mapping where client data actually lives, separating critical systems from general office traffic, and confirming that backups can restore both individual files and full working environments.
We also recommend tighter operational oversight through business IT operations management so incident handling is not improvised during a disruption. That includes alerting on failed jobs, quarterly restore testing, MFA hardening for admin access, and written escalation steps. For firms reviewing their obligations around cyber incidents and data handling, the CISA ransomware and recovery guidance is a useful baseline because it focuses on preparation, containment, and restoration rather than theory.
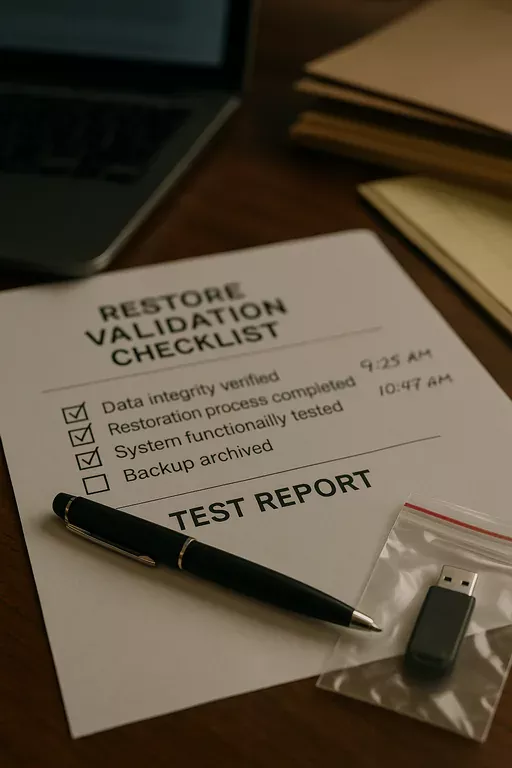
- Backup validation: Test file-level and full-environment restores on a schedule and document the results for internal review.
- MFA hardening: Require multifactor authentication for email, remote access, backup consoles, and privileged accounts.
- Access review: Audit permissions by role so legal assistants, partners, and outside users only reach the data they need.
- Incident runbook: Define who isolates systems, who communicates with attorneys, who checks deadlines, and who preserves logs and evidence.
Field Evidence: Restoring Access Without Repeating the Same Failure
In one Northern Nevada legal office corridor, the initial state was familiar: backup jobs showed green, but nobody had recently tested a full restore of document management data, mapped drives, and user permissions together. After a lockout event, staff were working from partial exports, intake slowed, and billing entries had to be reconstructed manually. The office also had to verify whether any client communications were delayed long enough to create reporting concerns.
After remediation, the firm moved to scheduled restore testing, documented file ownership, and clearer endpoint and server alerting. It also added support for growing Reno businesses that emphasized continuity rather than break-fix response. The result was a cleaner recovery path during later disruptions caused by line instability and office connectivity issues common in mixed older and newer building infrastructure around Reno-Sparks.
- Result: Recovery testing reduced file restoration time from several hours of uncertainty to a verified 42-minute process for priority legal data, while cutting staff idle time during follow-up incidents by more than 60%.
Law Firm Systems Risk Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Backup And Recovery Programs and has spent his career building practical recovery, security, and operational continuity processes for businesses across Sparks, Reno, and Northern Nevada and Northern Nevada.

Local Support in Sparks, Reno, and Northern Nevada
From our Reno office, we regularly support firms across Sparks, Reno, and nearby legal and professional corridors where fast response matters but documented recovery matters more. For offices near Lakeridge and south Reno, the travel time is short enough for on-site coordination when needed, but the real value comes from having systems, records handling, and recovery steps organized before a disruption affects client work.
Reduce Exposure Before the Next Outage Tests the Firm
For law firms in Sparks, the real issue is not whether a server, account, or file share can fail. It is whether the firm can prove it had reasonable safeguards, restore critical records quickly, and respond in a way that protects deadlines, confidentiality, and client trust. That is where legal liability and operational resilience meet.
If backups are untested, records handling is inconsistent, or response steps live only in someone’s memory, the next outage will be more than downtime. It will be an audit of the firm’s controls. The practical path forward is straightforward: document the environment, validate recovery, tighten access, and make incident response repeatable.

