Reno/Sparks IT Fail
The outage or lockout is usually the last symptom to appear, not the first. Unclear ownership, overlapping tools, and fragmented support create weak points that can disrupt proactive device and endpoint management and put response time, accountability, and outage recovery at risk. Reducing that risk starts with clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Vendor Chaos Brings Law Firm Systems Down
When a Sparks law firm has systems down, the root problem is often not a single failed device. It is usually fragmented ownership across internet, phones, line-of-business software, Microsoft 365, printers, workstations, and security tools. Each vendor manages one slice, but no one is responsible for the full operating picture. That gap is where outages grow. In legal environments, where document access, calendaring, intake, and billing all depend on connected systems, even a short interruption can ripple across the entire day.
We see this most often when an office manager is left coordinating multiple providers without a defined escalation map. One vendor changes DNS, another pushes a firewall rule, and a third updates an endpoint agent without checking compatibility. The result is delayed troubleshooting, duplicate tooling, and weak accountability. That is why firms dealing with recurring lockouts or inconsistent workstation behavior often need proactive device and endpoint management in Northern Nevada so patching, monitoring, access control, and response ownership are handled as one operating function instead of five separate conversations. In Zachary’s case, the visible outage was only the final symptom of weeks of unmanaged overlap.
- Technical factor: Overlapping vendor changes to identity, endpoint, and network settings can break authentication paths, disrupt shared resource access, and slow recovery because no single party has authority to isolate the fault quickly.
- Operational factor: Law firms depend on predictable access to document systems, email, phones, and billing platforms, so fragmented support directly affects intake, deadlines, and time capture.
- Local factor: Across Reno, Sparks, and Carson City, multi-vendor offices in older buildings or mixed-suite environments often inherit undocumented cabling, ISP handoff confusion, and legacy hardware that make ownership gaps worse.
How To Fix Ownership Gaps Before The Next Outage
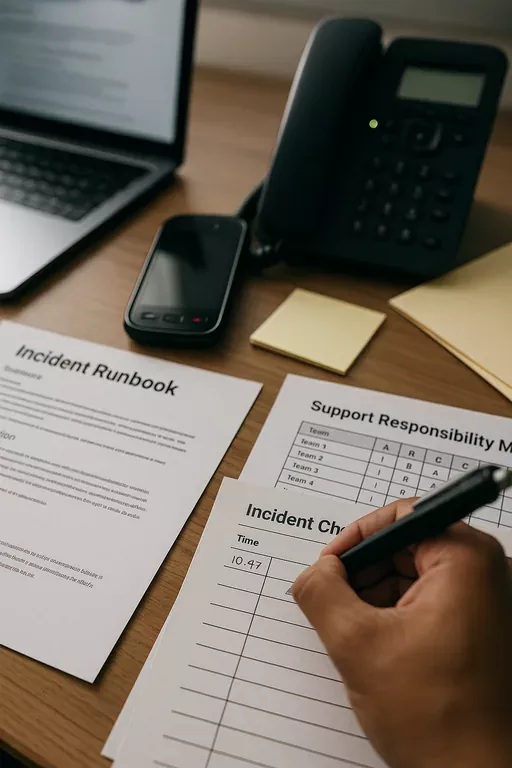
The practical fix is to assign clear operational ownership across endpoint, network, server, and vendor escalation layers. That starts with a current system inventory, a support responsibility matrix, and one documented incident path that defines who touches what first. For most firms, we recommend standardizing endpoint security, removing duplicate remote tools, confirming Microsoft tenant roles, and reviewing how phones, internet, and legal software depend on the local network. Firms that need stronger backbone stability usually benefit from improving network reliability with structured infrastructure management so switch configuration, firewall policy, wireless coverage, and ISP failover are not handled in isolation.
Remediation also needs verification, not assumptions. Backups should be tested, not just reported as successful. MFA policies should be reviewed against actual user workflows. Vendor contacts should be documented with escalation tiers and after-hours procedures. For legal offices handling sensitive client data, the operational baseline should align with practical guidance from CISA ransomware and resilience recommendations , especially around access control, recovery planning, and incident response readiness.
- Control step: Build a single escalation runbook that maps internet, firewall, endpoint, Microsoft 365, phone, and legal software dependencies, then assign one accountable owner for triage and vendor coordination.
- Control step: Standardize EDR, patching, and device policy so workstation issues are visible in one console instead of spread across multiple vendor dashboards.
- Control step: Validate backup recovery and core application access after every major network or identity change.
Field Evidence: Multi-Vendor Legal Office Recovery
In one Northern Nevada professional office corridor, the initial condition was familiar: intermittent file access, dropped VoIP registrations, inconsistent remote login behavior, and no agreed owner when something failed. The internet circuit was stable, but the firewall rules had been modified by one vendor, endpoint agents by another, and the server permissions had not been reviewed after a software migration. Staff were opening tickets in three different places and getting three different answers.
After consolidating escalation, documenting dependencies, and reviewing the underlying server and hybrid infrastructure management for multi-location operations , the office moved from reactive ticket chasing to a controlled support model. The before state was recurring downtime with unclear accountability. The after state was faster triage, fewer duplicate alerts, and a cleaner path for restoring access when a workstation or shared application failed. In practical terms, that meant fewer intake interruptions during busy court and filing weeks across Reno-Sparks.
- Result: Incident response time dropped from several hours of vendor back-and-forth to under 45 minutes for common access and connectivity issues, with noticeably fewer repeat outages over the following quarter.
Operational Reference: Where Vendor Gaps Usually Appear
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Proactive Device And Endpoint Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.

Local Support in Reno, Sparks, Carson City, and Northern Nevada
From our Reno office, we regularly support firms across Sparks and the surrounding Northern Nevada market where legal offices depend on stable phones, secure endpoints, shared files, and clear vendor coordination. The California Avenue corridor is only a short drive from our location, which matters when an issue needs both remote triage and local hands-on follow-through. For firms trying to reduce downtime tied to overlapping providers, local response and documented ownership make a measurable difference.
Clear Ownership Prevents Repeat Downtime
When a law firm in Sparks or Reno experiences a lockout, phone failure, or shared file outage, the technical fault is only part of the problem. The larger issue is often vendor chaos: too many tools, too many support contacts, and no single owner responsible for the full chain of systems that keep the office running. That is why outages take longer to diagnose and why the same problems tend to return.
The practical takeaway is straightforward. Clarify ownership, reduce overlap, document escalation, and validate the systems that matter most to legal operations. When endpoint management, network control, and infrastructure accountability are aligned, firms recover faster and spend less time chasing vendors during business hours.

