Reno/Sparks Hub Risk
What looks like a one-off issue is often tied to growth outpacing IT capacity. In logistics hub environments, endpoint sprawl, underplanned infrastructure, and inconsistent standards can turn into performance, reliability, and future growth long before anyone notices the warning signs. Closing those gaps early makes business IT operations management far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Scalability Ceilings Stop Logistics Operations

The main issue is not usually a single failed device. In Washoe County logistics environments, operations stop when growth quietly exceeds the design limits of the network, server capacity, identity controls, and endpoint management process. A site may add ten new users, several handheld devices, more cloud applications, and another shipping station without revisiting switch capacity, wireless density, DHCP scope, file access patterns, or onboarding standards. That is the scalability ceiling: the point where normal growth starts producing instability.
We see this most often in industrial corridors around Sparks and Reno where businesses expand quickly inside buildings that were not originally planned for dense wireless coverage or modern device counts. The result is intermittent slowness, dropped sessions, print failures, and stalled line-of-business applications that eventually become a full stop. Businesses trying to stay ahead of that pattern typically need structured business IT operations management so capacity, standards, and change control are reviewed before the next hiring wave. In cases like Priscilla’s, the outage is only the visible symptom; the root cause is usually unmanaged growth across users, devices, and dependencies.
- Endpoint Sprawl: As scanners, laptops, printers, tablets, and shared workstations accumulate, unmanaged device growth increases broadcast traffic, authentication failures, patch inconsistency, and support complexity.
- Infrastructure Saturation: Older switches, flat networks, and undersized wireless access point layouts create bottlenecks once staffing and shipment volume increase.
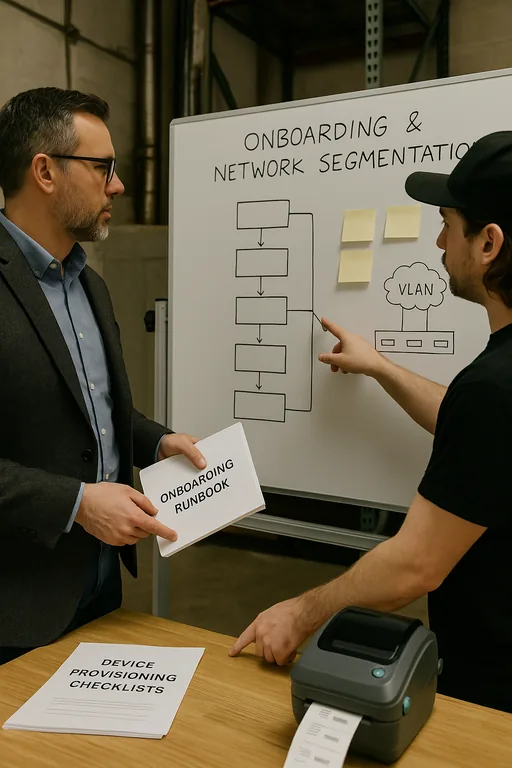
- Inconsistent Onboarding: When new users and devices are added without a standard build process, permissions drift, naming conventions break down, and troubleshooting takes longer during an outage.
- Application Dependency Creep: Shipping, inventory, ERP, VoIP, and cloud file systems often depend on the same core services, so one weak point can interrupt multiple workflows at once.
How to Remove the Ceiling Before Growth Causes Another Stop
The fix is operational as much as technical. First, map the actual environment: user counts, endpoint counts, switch utilization, wireless coverage, server workloads, cloud dependencies, and recovery priorities. Then standardize how every new employee, workstation, scanner, and application is introduced. Symptoms like operations stopping usually point to deeper issues than the immediate outage. For logistics hubs, standardizing how new users, devices, and systems are brought online is what keeps the problem from coming back.
From there, remediation usually includes segmented VLAN design, switch and access point capacity review, DHCP and DNS cleanup, documented onboarding templates, and alerting tied to real thresholds instead of waiting for complaints. Businesses with multiple shipping stations or warehouse offices often benefit from tighter network, server, and cloud management in Northern Nevada so performance and dependency issues are visible before they interrupt dispatch or receiving. For planning guidance, the CISA Cybersecurity Performance Goals provide a practical baseline for access control, asset visibility, resilience, and recovery.
- Capacity Review: Measure current utilization across switches, wireless, servers, storage, and internet circuits before adding the next group of users.
- Standardized Provisioning: Use documented builds for endpoints, printers, scanners, and user accounts so every addition follows the same security and performance baseline.
- Segmentation: Separate warehouse devices, office systems, guest access, and critical applications with VLANs and policy controls to reduce congestion and fault spread.
- Monitoring and Alerting: Track interface errors, access point saturation, authentication failures, and storage thresholds so small issues are addressed before they become downtime.
Field Evidence: Growth Pressure in a Sparks Distribution Corridor
In one Northern Nevada warehouse corridor, a growing operation had added staff, mobile devices, and cloud-based shipping tools over two quarters without redesigning the underlying network. Before remediation, supervisors were dealing with recurring disconnects, slow label generation, and periodic file lockups during peak receiving windows. The environment looked stable on paper, but switch uplinks were saturated, wireless overlap was poor near racking, and device enrollment was inconsistent.
After a structured cleanup that included switch replacement planning, wireless tuning, standardized endpoint deployment, and clearer dependency mapping, the site moved from reactive firefighting to predictable operations. A later review of network infrastructure management for multi-location operations also helped align warehouse and office traffic so future expansion would not hit the same ceiling again. That kind of before-and-after pattern is common in Washoe County facilities where growth happens faster than infrastructure planning.
- Result: Repeated shipping-station interruptions were reduced to isolated support tickets, onboarding time for new devices dropped by roughly 40%, and peak-hour network complaints fell significantly within the first month.
Scalability Risk Reference for Logistics IT Environments
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Business It Operations Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.
Local Support in Washoe County
Reno Computer Services supports businesses across Reno, Sparks, and the surrounding industrial corridors where logistics, warehousing, and distribution operations depend on stable networks and predictable onboarding. From our Reno office, the Kleppe Lane area is typically about 12 minutes away, which matters when a warehouse office, shipping station, or receiving desk loses access and operations begin stacking up.
Growth Has to Be Planned Into the Environment
When a logistics hub in Washoe County suddenly stops, the real issue is often not the outage itself. It is the accumulated effect of adding people, devices, applications, and workflow dependencies without expanding the underlying IT design. That is why scalability ceilings are so disruptive: they stay hidden until normal business growth turns into operational friction.
The practical takeaway is straightforward. Review capacity before the next hiring cycle, standardize onboarding for every user and device, and treat warehouse connectivity as a production system rather than a background utility. That approach reduces downtime, shortens recovery, and keeps future expansion from colliding with the network.

