Reno/Sparks Hub Audit
What looks like a one-off issue is often tied to legacy tools. In logistics hub environments, legacy systems, patchwork fixes, and hard-to-adopt tools can turn into efficiency, visibility, and growth long before anyone notices the warning signs. Closing those gaps early makes network server and cloud management far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why the Innovation Wall Stops Logistics Operations
When operations stop in a Washoe County logistics environment, the outage is rarely just a bad morning or a single failed device. More often, it is the result of an innovation wall: older hardware, outdated operating systems, and business software that cannot reliably support current cloud workflows, API connections, reporting tools, or AI-assisted planning. The business may still be functioning, but it is functioning on borrowed time.
We typically see this in facilities that added scanners, shipping stations, remote access, and cloud dashboards over several years without redesigning the underlying platform. That creates a stack where one legacy server becomes the choke point for inventory visibility, dispatch timing, and user authentication. In practice, network server and cloud management in Northern Nevada is what separates a stable logistics operation from one that stalls every time an old dependency fails. That is the same pattern behind incidents like Layla’s: the visible outage starts at the workstation, but the real failure sits deeper in the environment.
- Legacy compute limits: Older servers and storage platforms often cannot handle modern cloud sync, security agents, or analytics workloads without performance drops and lockups.
- Patchwork integrations: Temporary fixes between shipping software, file shares, printers, and remote users create brittle dependencies that break during updates or reboots.
- Visibility gaps: Teams may not know which system is authoritative for orders, inventory, or billing until an outage exposes the confusion.
- Adoption friction: If tools are too hard to use, staff work around them with spreadsheets, local saves, and manual steps that increase operational risk.
- Growth drag: Businesses remain stuck on 2019-era infrastructure while competitors scale with better reporting, automation, and cloud-ready workflows.
Practical Remediation for Legacy Logistics Environments
The fix is not simply replacing one failed server. The right approach is to reduce dependency on unsupported systems, document the workflow from intake to billing, and modernize the environment in stages that operations staff can actually absorb. For most logistics hubs, that means identifying which applications must stay on-premises, which can move to managed cloud platforms, and which should be retired entirely.
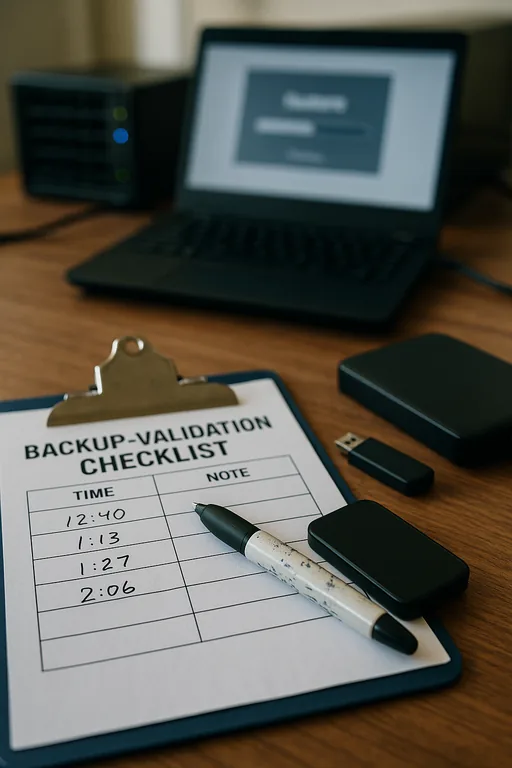
We usually start by stabilizing identity, storage, and endpoint health, then move into backup validation, application compatibility testing, and network segmentation for warehouse devices. Consistent proactive endpoint management for Reno operations helps prevent the same workstation, scanner, and access issues from reappearing after the core platform is repaired. For security and modernization planning, the CISA secure-by-design guidance is a useful reference because it reinforces reducing complexity and eliminating avoidable failure points.
- Server rationalization: Inventory every production server, remove abandoned roles, and migrate critical workloads off unsupported operating systems.
- Backup validation: Test restores at the file, VM, and application level so recovery is proven rather than assumed.
- MFA and identity hardening: Protect remote access, admin accounts, and cloud applications that support dispatch, billing, and reporting.
- VLAN segmentation: Separate warehouse devices, office systems, guest access, and server traffic to reduce lateral disruption during faults or security events.
- Alerting improvements: Monitor storage latency, failed backups, authentication errors, and line-of-business service health before users report the outage.
Field Evidence: From Repeated Stoppages to Stable Throughput
In one Northern Nevada distribution setting, the pattern was familiar: morning slowdowns, intermittent scanner disconnects, and a file-based workflow that froze whenever the primary server hit resource limits. The site was moving between Reno and Sparks routes daily, and even short interruptions caused missed handoff windows for outbound freight. After mapping the workflow, removing an obsolete application dependency, and restructuring the server and storage roles, the environment became far more predictable.
Just as important, the business gained clearer operational oversight through IT systems for multi-location operations instead of relying on tribal knowledge and emergency fixes. That shift reduced escalations, shortened recovery time, and gave managers a more accurate view of what was happening across dispatch, warehouse, and back-office functions.
- Result: Unplanned workflow interruptions dropped from multiple incidents per month to one minor event in a full quarter, while order processing delays were reduced by roughly 70%.
Legacy Logistics Risk and Control Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Network Server And Cloud Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.

Local Support in Washoe County
Reno Computer Services supports organizations across Reno, Sparks, and the wider Washoe County area where logistics, warehousing, and multi-site coordination depend on stable systems. For businesses operating near Raleigh Heights and surrounding corridors, local response matters, but so does designing the environment so every issue does not require an emergency drive across town.
Modernization Is an Operations Issue, Not Just an IT Project
For logistics hubs in Washoe County, operations stopping is usually a sign that the environment has outgrown the tools underneath it. Legacy hardware, unsupported software, and years of workaround-driven decisions create a fragile system where one failure can interrupt dispatch, visibility, billing, and customer communication all at once.
The practical takeaway is straightforward: simplify the stack, validate recovery, and modernize the systems that carry daily operations before the next outage forces the decision. That approach improves resilience, makes cloud adoption more realistic, and gives leadership better control over growth.

