Reno/Sparks Hub Audit
When a business is dealing with operations stopping, the failure usually started earlier. Poor safeguards, inconsistent records handling, and a slow response can weaken security monitoring and response over time and leave logistics hubs in The Truckee Meadows exposed when pressure hits. Addressing the problem means documenting safeguards, tightening response steps, and protecting sensitive data.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Operations Stop Before Anyone Calls It a Legal Problem
When a Truckee Meadows logistics hub suddenly cannot move freight, print manifests, confirm chain-of-custody records, or access customer instructions, the immediate symptom is operational stoppage. The underlying problem is usually broader: weak security monitoring, inconsistent document handling, and no disciplined response path when something abnormal starts. That is where legal liability enters the picture. If client data is lost, altered, or exposed, saying no one knew what was happening is not a defense that carries much weight in a Reno court.
We typically find that the breakdown starts with fragmented oversight. One team stores records in email, another in a shared drive, and another in a cloud application with inconsistent permissions. Alerts may exist, but nobody is accountable for reviewing them in real time. Once a suspicious login, file deletion, sync conflict, or endpoint compromise occurs, the business loses both operational continuity and defensible documentation. That is why structured security monitoring and response in Northern Nevada matters for logistics environments that depend on timing, dispatch accuracy, and customer trust. In cases like the one above, the real issue was not only downtime; it was the inability to prove what happened, when it happened, and whether regulated or contract-sensitive information had been affected.
- Technical factor: Disconnected logging, inconsistent file permissions, and delayed alert review can turn a minor access anomaly into a full operational stoppage with audit exposure.
- Operational factor: Multi-shift dispatch, warehouse coordination, and remote yard access create more handoff points where records handling can drift out of policy.
- Legal factor: If customer records, delivery data, or internal notes are mishandled, the absence of documented safeguards can become part of the liability analysis.
What Practical Remediation Looks Like in a Working Logistics Environment
The fix is not a single tool. It is a controlled operating model. Start by identifying where dispatch records, customer files, scanned documents, and operational communications actually live. Then standardize permissions, retention, and logging across those systems. For many businesses, that means tightening Microsoft 365 controls, reducing informal file sharing, and creating a clear incident path so unusual activity is reviewed before it disrupts operations. Stronger cloud and Microsoft environment management is often the fastest way to reduce both downtime and audit risk.
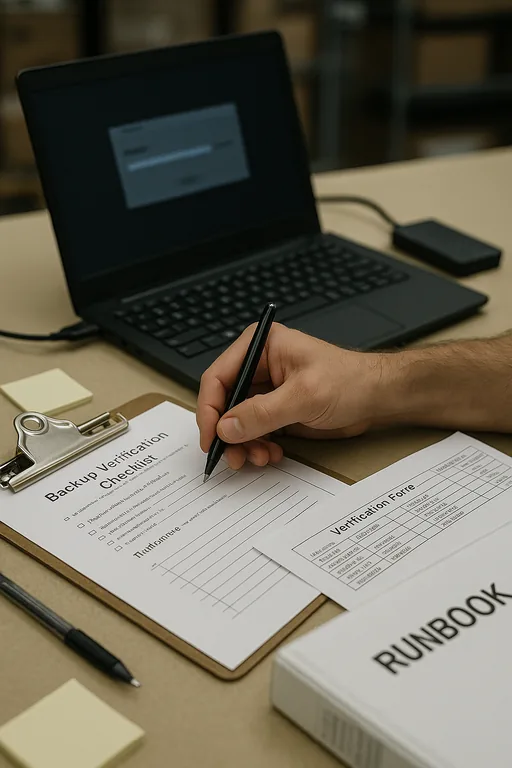
From there, the remediation needs to be tested, not assumed. We recommend validated backups for critical records, MFA hardening for all administrative and remote-access accounts, endpoint detection and response on dispatch and warehouse systems, and documented escalation steps for after-hours incidents. For organizations reviewing their legal exposure, the CISA Cybersecurity Performance Goals provide a practical baseline for access control, logging, recovery, and incident handling without turning the process into a paperwork exercise.
- Control step: Centralize logs from endpoints, Microsoft 365, firewalls, and file systems so access anomalies can be correlated quickly.
- Control step: Enforce MFA and conditional access for dispatch, finance, and admin users with elevated access to customer and shipment records.
- Control step: Validate backups through test restores of manifests, billing files, and operational documents rather than relying on backup job success messages alone.
- Control step: Document response ownership so supervisors know who isolates devices, who reviews logs, and who handles customer and legal notification decisions.
Field Evidence: Dispatch Recovery After Records Access Failure
In one Northern Nevada freight and yard-support environment, the business was operating with shared credentials, inconsistent SharePoint permissions, and no reliable way to tell whether missing files had been deleted, moved, or encrypted. During a high-volume week with weather-related schedule pressure moving between Reno and outlying sites, dispatch slowed to manual workarounds and supervisors had no clean audit trail for customer communication.
After access was restructured, alerting was centralized, and core systems were brought under documented oversight, the business moved from reactive troubleshooting to controlled recovery. That included better event visibility, tested file restoration, and clearer separation between operations, finance, and administrative access. Longer term, they also benefited from IT systems for multi-location operations that reduced the chance of one site-level issue spreading into a wider outage.
- Result: Critical dispatch and billing records were restored in under 90 minutes during later incidents, unauthorized access attempts were identified faster, and manual shipment delays dropped substantially over the following quarter.
Operational Controls That Reduce Downtime and Liability
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Security Monitoring And Response and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.

Local Support in The Truckee Meadows
From central Reno to outlying logistics and yard locations, response planning has to account for travel time, site access, and the reality that operational interruptions do not wait for ideal conditions. We support businesses across The Truckee Meadows with practical security oversight, recovery planning, and incident response structure that fits active operations.
The Real Audit Starts Before the Outage
For logistics hubs in The Truckee Meadows, operations stopping is rarely just an IT inconvenience. It is usually evidence that safeguards, records handling, and response ownership were not strong enough before the incident. Once dispatch records, billing data, or customer files become unavailable or questionable, the business is dealing with both downtime and legal exposure.
The practical takeaway is straightforward: document where critical information lives, control who can access it, monitor for abnormal activity, and rehearse recovery before a high-pressure day forces the issue. That approach reduces interruption, improves defensibility, and gives leadership a clearer picture of what happened when systems are under strain.

