Reno/Sparks File Security
This kind of issue rarely appears all at once. For manufacturing plants in Northern Nevada, it usually builds through surprise spending, delayed upgrades, and aging infrastructure and then surfaces as encrypted files, slower recovery, or higher exposure. A more reliable setup starts with planning upgrades deliberately and aligning IT decisions to business risk.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Encrypted Files Often Start as a Budgeting Problem

When a manufacturing plant in Northern Nevada ends up with encrypted files, the immediate assumption is usually malware alone. In practice, we often find a broader financial roadmap gap behind the incident. Systems stay in place past their safe lifecycle, backup storage is expanded only after capacity warnings, and security controls are added reactively instead of as part of a planned operating budget. That is how IT becomes a surprise expense rather than a managed business function.
For plants in Reno, Sparks, Carson City, and surrounding industrial corridors, the risk is amplified by always-on operations, older line-of-business software, and mixed environments that include office systems, production workstations, shared file servers, and remote vendor access. If backup architecture is underfunded or tested inconsistently, encrypted files become more than a security event. They become a production scheduling problem, a shipping problem, and often a cash-flow problem. This is why businesses dealing with recovery exposure usually need managed backup solutions in Northern Nevada that are tied to business priorities instead of ad hoc purchases. In Kathleen’s case, the file encryption event was only the visible symptom of years of delayed infrastructure decisions.
- Aging infrastructure: Older servers, unsupported operating systems, and end-of-life storage arrays increase the chance that a ransomware event or file corruption issue spreads faster than the business can isolate it.
- Unplanned spending cycles: When upgrades are postponed until failure, backup retention, recovery speed, and endpoint protection are usually compromised at the same time.
- Operational dependency: Manufacturing teams rely on shared drawings, work orders, ERP exports, and shipping records, so even partial file encryption can halt production flow.
- Weak recovery validation: Many plants have backups on paper, but no routine restore testing to confirm that critical files can be recovered within the time the operation actually needs.
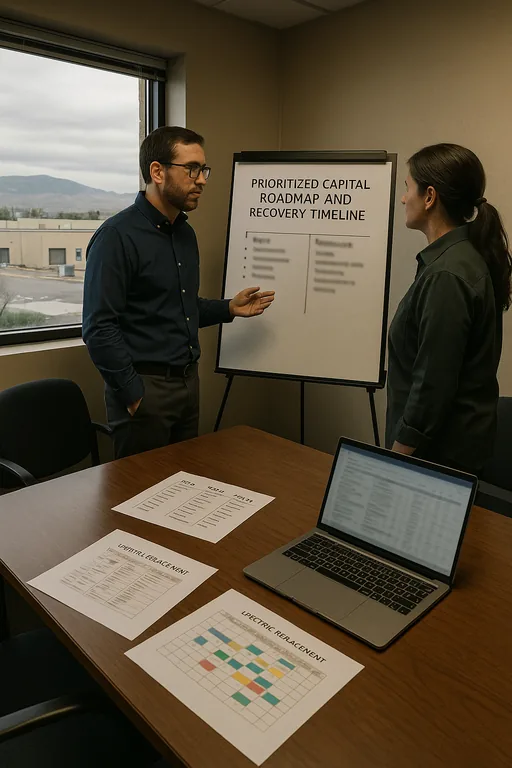
How to Close the Financial Roadmap Gap Before Recovery Fails
The fix is not just buying another appliance or adding more cloud storage. The right approach is to build a staged roadmap that ranks systems by operational impact, then funds security and recovery controls in the order the business would need them during an outage. For manufacturing environments, that usually means separating office and production assets, tightening privileged access, validating immutable backups, and documenting recovery priorities for file shares, ERP data, and shipping systems first.
We also recommend standardizing Microsoft 365, identity, and endpoint policy management so the environment is easier to secure and recover. Plants with hybrid file access and remote supervisors often reduce risk by improving cloud and Microsoft environment management across user accounts, SharePoint, OneDrive, and conditional access policies. For practical ransomware resilience guidance, the CISA ransomware guide remains a useful operational reference.
- Backup validation: Run scheduled restore tests against critical file sets and production-support data so recovery time is measured, not assumed.
- MFA hardening: Enforce phishing-resistant or app-based multifactor authentication for remote access, admin accounts, and cloud services.
- Network segmentation: Separate production systems, office users, and vendor access paths with VLANs and access controls to limit lateral movement.
- Lifecycle budgeting: Put servers, storage, firewalls, and licensing on a replacement schedule so upgrades happen before failure or encryption events expose the gap.
Field Evidence: Recovery Planning That Reduced Production Disruption
We worked with a Northern Nevada operation in an industrial corridor where file storage had grown for years without a formal replacement plan. Before remediation, backup jobs were completing inconsistently, restore testing was rare, and line supervisors were storing critical documents across a mix of local shares and cloud folders. During winter weather and carrier instability, even short interruptions from Spectrum or local power events made the environment harder to trust because no one had a clear order of recovery.
After documenting business-critical systems, restructuring backup tiers, and aligning server and storage refresh timing with a formal capital plan, the business moved from reactive recovery to a controlled process. They also improved infrastructure management for multi-site operations so network, storage, and endpoint decisions were reviewed together instead of in isolation.
- Result: Restore testing improved from occasional spot checks to quarterly validation, critical file recovery time dropped from most of a workday to under 90 minutes, and unplanned IT spending became a forecasted line item instead of an emergency purchase.
Manufacturing Recovery Planning Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Backup Solutions and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.
Local Support in Reno and Northern Nevada
Our office on Ryland Street is a short drive from the Vassar Street area, which matters when a manufacturing or operations team is dealing with encrypted files, failed restores, or a recovery decision that cannot wait until the next day. We regularly support Reno-area businesses that need practical response, clear prioritization, and a better long-term roadmap for backup, infrastructure, and security spending.
What Manufacturing Leaders Should Take Away
Encrypted files in a manufacturing plant are often the final result of a longer pattern: deferred upgrades, unclear ownership, backup assumptions, and no financial roadmap that connects technology spending to operational risk. The technical issue matters, but the planning gap is usually what turns a recoverable event into a costly interruption.
A stronger position comes from budgeting infrastructure deliberately, testing recovery on a schedule, and treating backup, identity, and network controls as part of plant continuity. When those decisions are made early, downtime is shorter, recovery is cleaner, and IT stops behaving like an emergency line item.

