Reno/Sparks Data Breach
The outage or lockout is usually the last symptom to appear, not the first. Surprise spending, delayed upgrades, and aging infrastructure create weak points that can disrupt disaster recovery planning and recovery and put budget control, resilience, and uptime at risk. Reducing that risk starts with planning upgrades deliberately and aligning IT decisions to business risk.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Financial Roadmap Gaps Turn Into Breach Exposure
For construction firms in Sparks, a data breach often starts long before anyone notices suspicious logins or encrypted files. The more common pattern is financial drift: firewall replacement gets pushed another quarter, backup storage stays undersized, line-of-business servers remain on aging operating systems, and remote access expands without a matching security review. When IT is treated as a surprise expense instead of a planned operating function, risk accumulates quietly in estimating systems, accounting platforms, document shares, and field access tools.
That is where the financial roadmap matters. A construction company may believe it is controlling costs by delaying upgrades, but in practice it is extending the life of unsupported systems and leaving recovery gaps in place. We see this most often in firms balancing office staff in Sparks or Reno with superintendents, project managers, and subcontractor coordination across multiple job sites. A breach then becomes more than a security event; it interrupts billing, payroll, change-order processing, and access to plans. Businesses trying to reduce that exposure usually need structured disaster recovery planning and recovery in Northern Nevada so the budget reflects actual business risk instead of reacting after an outage.
- Aging infrastructure: Older servers, unsupported software, and deferred network refresh cycles create exploitable weak points that attackers and commodity malware routinely target.
- Unplanned spending patterns: When each IT decision is made under pressure, security controls are purchased inconsistently and recovery capability is rarely tested end to end.
- Shared financial data exposure: Construction firms often keep bids, contracts, AP records, and project cost files in broad-access shares, which increases the blast radius of one compromised account.
- Operational dependency: As Madelyn’s situation illustrates, a single access failure can stall billing approvals, vendor communication, and schedule updates across office and field teams.
How To Reduce Breach Risk Without Turning IT Into Constant Emergency Spend
The fix is not simply buying another security product. The practical approach is to build a prioritized roadmap that ties infrastructure age, business process dependency, and recovery objectives together. For a construction firm, that usually means identifying which systems support estimating, accounting, document storage, payroll, and remote field access, then assigning realistic replacement windows and recovery targets to each one. This is where disciplined infrastructure management programs for growing Reno businesses help prevent the cycle of delayed upgrades followed by emergency remediation.
We typically recommend a layered control set: MFA hardening for remote access and Microsoft 365, endpoint detection and response on all office and field laptops, backup validation with restore testing, network segmentation between core business systems and general user traffic, and alerting tied to privileged account changes. Construction firms should also align their planning to practical guidance from CISA’s ransomware and resilience guidance , especially where shared storage and remote access are involved. The goal is predictable capital planning, fewer emergency purchases, and faster recovery when an incident does occur.
- Roadmap-based refresh planning: Replace unsupported firewalls, switches, servers, and backup appliances on a scheduled cycle tied to business impact, not just failure events.
- MFA and access control: Require multifactor authentication for email, VPN, cloud file access, and administrator accounts, while reducing broad shared-folder permissions.
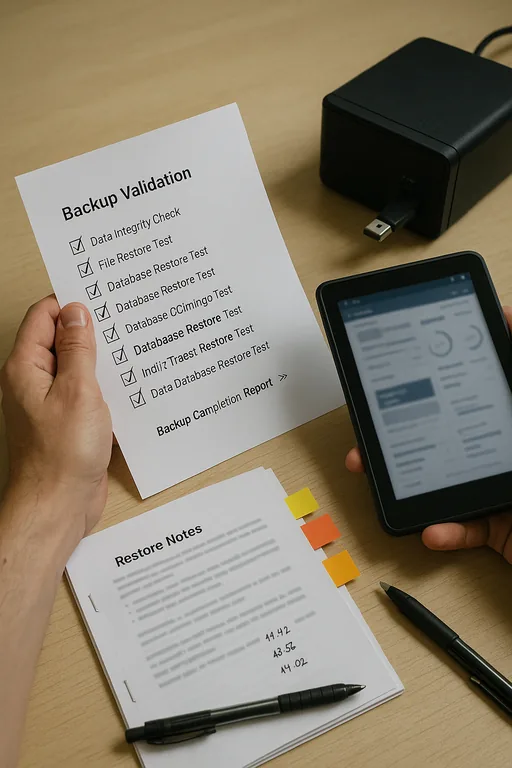
- Backup validation: Test restores for accounting data, project files, and line-of-business applications so recovery assumptions are proven before an incident.
- Endpoint and network controls: Deploy EDR, isolate sensitive systems with VLAN segmentation, and improve alerting around unusual login behavior and privilege escalation.
Field Evidence: From Deferred Upgrades To Predictable Recovery
We worked through a similar pattern with a regional contractor operating between Sparks, Reno, and outlying job sites where winter weather and distance made on-site delays more expensive. Before remediation, the company had an aging firewall, inconsistent laptop controls, and backups that existed on paper but had not been fully tested against live accounting and project data. After a phased refresh, access hardening, and documented recovery testing, the firm moved from reactive spending to a planned operating model with clearer ownership and fewer interruptions.
That improvement was not about adding complexity. It came from treating IT as a business system with budget discipline. Leadership also benefited from clearer forecasting through IT consulting in Northern Nevada , which helped tie upgrade timing to risk, compliance expectations, and operational dependency rather than waiting for another emergency.
- Result: Recovery testing time dropped from an unverified multi-day assumption to a documented 4-hour restore window for core financial and project file systems, while unplanned IT spend was reduced over the following budget cycle.
Construction IT Risk Control Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Disaster Recovery Planning And Recovery and has spent his career building practical recovery, security, and operational continuity processes for businesses across Sparks, Reno, and Northern Nevada and Northern Nevada.

Local Support in Sparks, Reno, and Northern Nevada
Construction firms in Sparks and nearby Reno often need support that can connect budgeting decisions to real recovery risk, especially when office staff, accounting systems, and field operations all depend on the same core infrastructure. Our office on Ryland Street supports businesses across the region, and the route to the Moana corridor is typically about 10 minutes under normal conditions, which matters when access failures affect billing, scheduling, or project coordination.
Budget Discipline Is Part Of Breach Prevention
A construction firm does not usually end up in breach recovery because of one isolated mistake. More often, the problem develops through delayed replacements, unclear ownership, and IT decisions made only when something breaks. That is why the financial roadmap matters. It gives leadership a way to prioritize upgrades, control spending, and reduce the chance that one compromised device or account will interrupt accounting, project coordination, or recovery operations.
For Sparks businesses, the practical takeaway is straightforward: if disaster recovery, security controls, and infrastructure planning are not being reviewed together, the company is likely carrying more operational risk than it realizes. A predictable plan is usually less expensive than emergency response, delayed billing, and unplanned downtime.

