Reno Network Crash Risk
This kind of issue rarely appears all at once. For financial offices in Northern Nevada, it usually builds through phishing clicks, password reuse, and weak account hygiene and then surfaces as a network crash, slower recovery, or higher exposure. A more reliable setup starts with tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Human Error Still Causes Network Failure in Financial Offices
The main question is straightforward: can weak user habits really lead to a network crash in a financial office? Yes. In practice, the crash is often not a dramatic hardware failure. It is a chain reaction that starts with a user clicking a fake reset link, reusing a password that was already exposed elsewhere, or approving a login prompt without verifying it. In Northern Nevada financial environments, that can quickly affect email, shared drives, remote access, endpoint trust, and even core workflow systems tied to billing or document review.
We typically find that the human element becomes the trigger, while the network and endpoint stack become the amplifiers. Once one account is compromised, attackers often use that foothold to move through synced credentials, cloud sessions, mapped drives, and unmanaged local admin rights. That is why proactive device and endpoint management in Northern Nevada matters so much. It reduces the chance that one bad click turns into a wider outage. In a regulated office, the business consequence is not limited to downtime. It can also mean delayed client communication, interrupted reporting, and added scrutiny around access controls. As Iris’s situation shows, the visible outage is usually the last stage of a problem that started with basic account hygiene.
- Credential reuse: Staff often use similar passwords across cloud tools, remote access portals, and internal systems, which allows one compromised login to affect multiple business functions.
- Phishing-driven session theft: Fake password reset emails and spoofed Microsoft 365 prompts can capture credentials or session tokens without triggering immediate suspicion.
- Weak endpoint control: Devices without consistent policy enforcement, patching, and alerting give attackers more time to persist after initial access.
- Shared operational dependencies: Financial offices rely on tightly connected email, file storage, printers, scanners, and line-of-business applications, so one account issue can create broad workflow disruption.
Practical Remediation for Identity, Endpoint, and Access Stability
The fix is not a single product. It is a set of controls that reduce the odds of user error becoming an operational incident. We start by hardening identity: phishing-resistant MFA where possible, conditional access rules, removal of stale accounts, password manager adoption, and review of mailbox forwarding and sign-in anomalies. Then we tighten endpoint policy so devices cannot quietly become the next stage of the incident. For financial offices, this work should be documented and repeatable, especially when audit readiness matters.
That is where governance and audit preparation for regulated operations becomes useful. It turns security expectations into enforceable policy, user training, access review cadence, and evidence that controls are actually being followed. For a practical baseline on phishing-resistant practices and account protection, the guidance from CISA is worth aligning to, especially for offices handling sensitive financial records.
- MFA hardening: Require multi-factor authentication on email, VPN, cloud apps, and administrator access, while reducing prompt fatigue through conditional access tuning.
- EDR deployment: Use endpoint detection and response to identify suspicious login behavior, token misuse, and lateral movement from compromised devices.
- Mailbox and identity review: Audit forwarding rules, impossible travel events, legacy authentication, and dormant accounts on a scheduled basis.
- Least-privilege access: Remove unnecessary admin rights and separate standard user activity from elevated administrative tasks.
- User habit reinforcement: Train staff to verify reset requests, report suspicious prompts, and stop using recycled passwords across business systems.
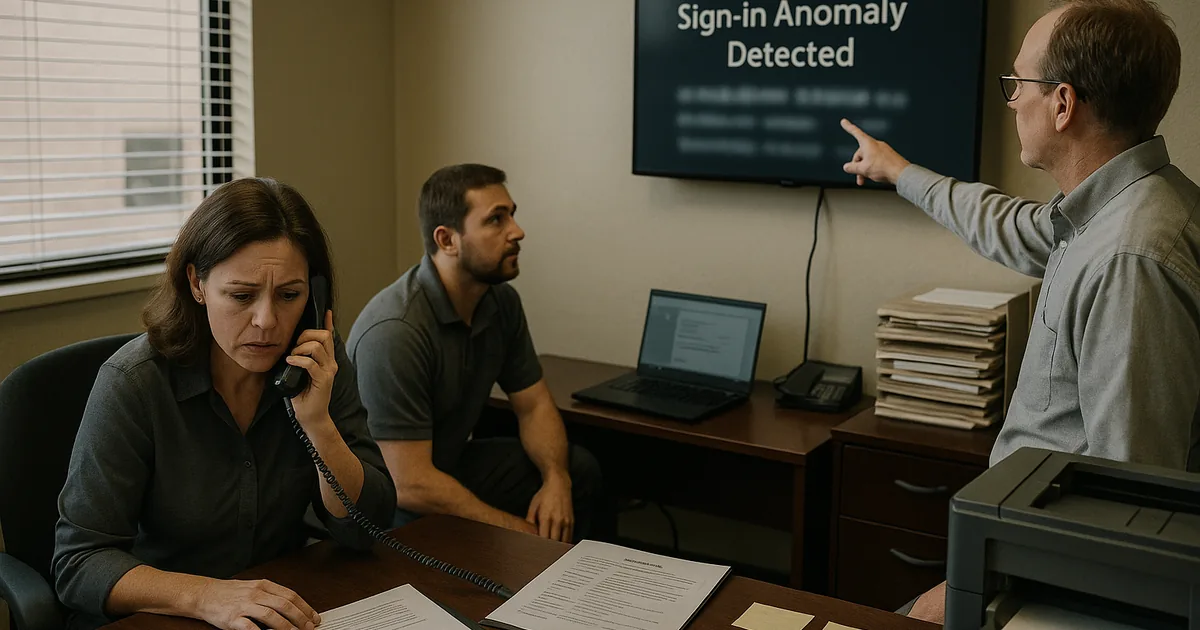
Field Evidence: Credential Cleanup Restored Stability for a Reno Financial Workflow
We worked through a case with a small financial office operating between central Reno and client meetings across Sparks. Before remediation, the office had recurring lockouts, inconsistent file access, and repeated email security alerts that staff treated as isolated annoyances. The underlying issue was broader: reused passwords, weak MFA enrollment, and no structured review of sign-in anomalies or endpoint exceptions.
After identity cleanup, endpoint policy enforcement, and a documented response process, the office moved from reactive troubleshooting to controlled operations. Staff could access the systems they needed without repeated lockouts, suspicious forwarding rules were eliminated, and incident review time dropped because alerts were tied to clear ownership. For firms that also need documented oversight, compliance-focused IT management helps connect technical controls to policy and reporting expectations.
- Result: Account-related disruptions dropped by 70 percent over the next quarter, and recovery from suspicious login events went from most of a business day to under 45 minutes.
Reference Table: Human Element Risks in Financial Office Networks
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Proactive Device And Endpoint Management and has spent his career building practical recovery, security, and operational continuity processes for businesses across Northern Nevada and Northern Nevada.

Local Support in Northern Nevada
Financial offices in Reno, Sparks, Carson City, and nearby business corridors often need fast response when account compromise starts affecting access, billing, or endpoint trust. From our Reno office, we support organizations that need practical remediation, documented controls, and local follow-through when a user-driven security issue begins to impact daily operations.
Operational Takeaway for Financial Offices
When a financial office in Northern Nevada suffers a network crash tied to the human element, the root problem is usually not the network alone. It is the combination of weak account practices, inconsistent endpoint control, and too much trust placed in routine-looking email activity. That is why the right response starts with identity hardening, endpoint visibility, and documented operating discipline.
Handled early, these issues are manageable. Left alone, they tend to surface as downtime, delayed billing, access instability, and avoidable compliance pressure. The practical goal is not perfection. It is building a setup where one employee mistake does not become a business-wide interruption.

