Reno Network Crash Audit
This kind of issue rarely appears all at once. For financial offices in Northern Nevada, it usually builds through poor safeguards, inconsistent records handling, and a slow response and then surfaces as a network crash, slower recovery, or higher exposure. A more reliable setup starts with documenting safeguards, tightening response steps, and protecting sensitive data.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why a Network Crash Becomes a Legal Liability in Financial Offices
For financial offices in Reno, Sparks, Carson City, and the surrounding Northern Nevada market, a network crash is not only an uptime problem. It can become a legal liability issue when client records, tax documents, account data, or internal communications are unavailable, altered, or exposed during the event. The operational question is straightforward: if a firm cannot show what safeguards were in place, how records were handled, and how the incident was contained, it becomes much harder to defend the outcome after the fact.
We typically find that these failures build quietly. Endpoint protections drift out of policy, shared folders accumulate broad permissions, firewall changes are poorly documented, and backup assumptions go untested. When the environment finally fails under load, after a switch issue, malformed update, storage fault, or malware event, the office is left reconstructing what happened instead of executing a known response plan. That is where endpoint and threat protection in Northern Nevada matters: it gives financial firms better visibility into suspicious activity, device health, and containment steps before a routine outage turns into a reportable incident. As the discussion often comes up in Reno legal and compliance conversations, saying you did not know client data was at risk is not a strong defense if the controls were never documented or enforced.
- Technical factor: Flat networks, inconsistent endpoint controls, and undocumented access paths make it easier for a single failure to interrupt file access, delay billing, and increase exposure around confidential financial records.
- Operational factor: Slow incident triage means staff keep working around the problem, which can overwrite logs, delay containment, and complicate later review.
- Records factor: If retention, access, and recovery procedures are inconsistent, the office may not be able to prove what data was affected or whether it was restored intact.
Practical Remediation for Recovery, Containment, and Audit Readiness
The fix is not a single product. It is a disciplined combination of network design, endpoint control, documented response steps, and tested recovery. In financial environments, we start by identifying where client records live, who can access them, what systems are business-critical, and which devices create the highest exposure if they fail. From there, the office needs segmented traffic, current admin credentials under control, hardened endpoints, and backups that are tested against actual recovery objectives rather than assumed to work.
That usually means tightening switch and firewall documentation, validating alerting, and improving network infrastructure management for Reno financial operations so a single device issue does not take down the entire office. It also means aligning response procedures with practical guidance from CISA , especially around containment, recovery sequencing, and evidence preservation. Where firms rely on local servers, hybrid file storage, or older applications, we also review dependencies so recovery does not stall because one overlooked service failed to restart.
- Control step: Segment critical systems and restrict lateral movement with VLANs, role-based access, and firewall policy review.
- Control step: Enforce MFA, EDR, and device policy baselines on all workstations that handle client financial records.
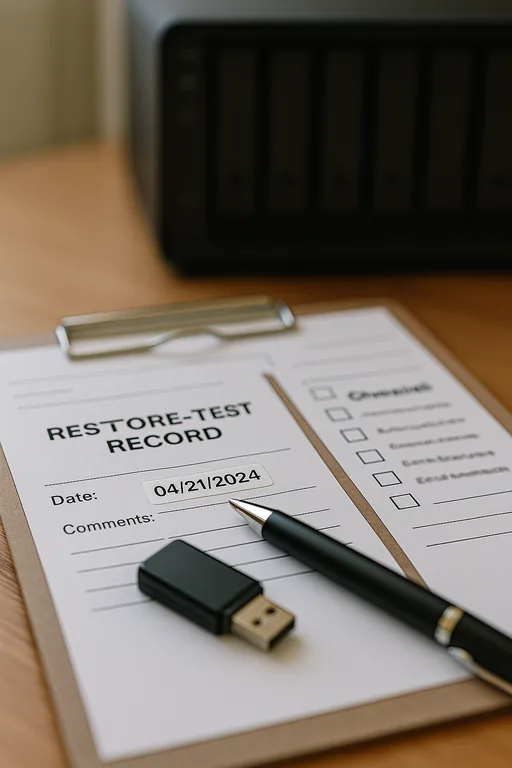
- Control step: Validate backups with scheduled restore testing, including line-of-business applications and shared file permissions.
- Control step: Maintain an incident runbook that defines who isolates systems, who communicates with staff, and how evidence is preserved.
Field Evidence: From Unplanned Outage to Defensible Recovery
In one Northern Nevada financial office corridor, the initial condition was familiar: aging switching equipment, broad shared-drive permissions, no recent restore test, and no clear separation between user traffic and critical business systems. When a network event disrupted access, staff could not tell whether the problem was hardware failure, malware, or a corrupted file service. That uncertainty extended downtime and created unnecessary concern around client record integrity.
After remediation, the environment was restructured with documented network paths, stronger endpoint controls, tested recovery procedures, and clearer server dependency mapping through server and hybrid infrastructure management . The next service interruption was isolated to a single network segment during a winter weather-related power fluctuation, and the office restored priority systems in a controlled sequence. That kind of outcome is what Luke needed the first time: a response that protects operations and supports later review instead of forcing the office to guess under pressure.
- Result: Recovery time for core file and application access dropped from most of a business day to under 75 minutes, with documented restoration steps and no unresolved questions about which client records were affected.
Financial Office Network Crash Risk Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Endpoint And Threat Protection and has spent his career building practical recovery, security, and operational continuity processes for businesses across Northern Nevada and Northern Nevada.
Local Support in Northern Nevada
Financial offices around Reno often need support that understands both the technical issue and the operational consequences of downtime. From our office on Ryland Street, Raleigh Heights is typically about 18 minutes away under normal conditions, which helps when a firm needs on-site coordination, network review, or recovery planning tied to real business workflows.
What Financial Offices Should Take Away
A network crash in a financial office is rarely just a technical interruption. It exposes how well the firm controls access, protects client records, documents response steps, and restores operations under pressure. In Northern Nevada, where smaller offices often balance compliance expectations with lean internal staffing, those gaps tend to stay hidden until a failure forces them into view.
The practical takeaway is to treat resilience and legal defensibility as part of the same process. If safeguards are documented, endpoints are controlled, backups are tested, and recovery roles are clear, the office is in a much stronger position to limit downtime and answer hard questions after an incident.

