Reno Network Crash
Seeing a network crash is often the visible symptom of compliance gaps, not the root problem itself. In financial offices across Reno, issues like missing controls, weak documentation, and loose access policies can quietly undermine endpoint and threat protection until work stops or risk spikes. The fix usually starts with reviewing controls, access, and recovery steps before they are tested under pressure.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Compliance Gaps Often Sit Behind a Network Crash
In Reno financial offices, a network crash is often the event that exposes a longer-running control failure. The visible outage may involve endpoints dropping off the domain, security tools failing to update, or users losing access to line-of-business systems. The underlying issue is usually weaker than expected governance around access, documentation, and change control. When regulations and internal requirements move faster than the office can document them, endpoint protection becomes inconsistent and threat response slows down.
We see this most often in firms that have grown quickly, added hybrid work, or layered on new compliance obligations without revisiting how systems are actually administered. A financial office may believe it has protection in place, but if device baselines are not enforced, privileged accounts are not reviewed, and exceptions are handled informally, the environment becomes fragile. That is why firms dealing with recurring instability often need tighter endpoint and threat protection for Reno financial operations rather than another one-time repair. In cases like Bentley’s, the outage is the symptom; the real problem is that the control set no longer matches the business risk.
- Documentation drift: Security controls may exist on paper but not reflect current users, devices, remote access methods, or vendor connections.
- Access sprawl: Former staff, shared credentials, and unreviewed admin rights increase both operational instability and audit exposure.
- Policy mismatch: Requirements tied to CMMC, HIPAA, or financial data handling can change faster than internal IT procedures are updated.
- Endpoint inconsistency: Devices missing current policies, agent health checks, or patch validation can trigger broader failures during normal business hours.
How to Stabilize the Environment Before the Next Audit or Outage
The practical fix is not just replacing hardware or rebooting services. It starts with a control review that maps real systems, real users, and real business processes against the compliance obligations the office is expected to meet. We typically begin by validating endpoint coverage, confirming administrative access paths, reviewing exception handling, and testing whether recovery steps are documented well enough for someone other than the usual technician to execute them. For financial offices, identity controls matter just as much as endpoint tooling, which is why stronger identity and email security in Reno offices is often part of the remediation path.
From there, the environment should be hardened in layers: enforce MFA for privileged access, standardize endpoint policy deployment, validate backup recovery, and create an approval process for remote access and vendor exceptions. It also helps to align controls with a recognized framework so the office is not guessing what “good enough” looks like. The CISA Cybersecurity Performance Goals are a useful operational reference because they translate security expectations into practical controls that smaller and mid-sized businesses can actually implement.
- Access review: Remove stale accounts, reduce local admin rights, and document who can approve elevated access.
- MFA hardening: Require phishing-resistant or app-based MFA for remote access, email, and administrative systems.
- Endpoint baseline: Standardize EDR deployment, patch cadence, encryption status, and policy health reporting across all workstations.
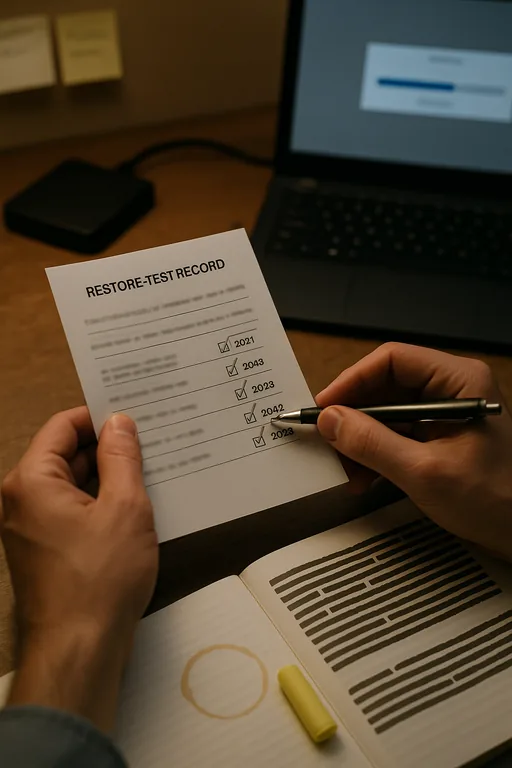
- Backup validation: Test file and system recovery on a schedule instead of assuming backups will work during an incident.
- Change control: Record security exceptions, vendor access, and policy changes so audits and incident reviews have a usable trail.
Field Evidence: Compliance Cleanup Restored Operational Stability
We worked through a similar pattern with a professional office operating between central Reno and North Valleys locations. Before remediation, staff experienced intermittent endpoint policy failures, inconsistent login behavior, and delayed access to shared financial records after routine updates. The office had security tools installed, but no one had recently verified whether policies, user roles, and recovery documentation still matched the way the business actually operated.
After a structured review, the office reduced privileged accounts, standardized endpoint enforcement, documented exception handling, and added clearer alerting through security monitoring and response oversight . That changed the environment from reactive troubleshooting to measurable control management. In a Northern Nevada setting where offices may depend on a mix of local ISP connectivity, remote staff, and small internal admin teams, that shift matters because outages are harder to absorb when every person in the office wears multiple hats.
- Result: Unplanned endpoint-related disruptions dropped over the next quarter, recovery documentation was usable by non-primary staff, and audit preparation time was reduced by roughly 40 percent.
Compliance Gap Audit Reference Points for Financial Offices
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Endpoint And Threat Protection and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in Reno and Northern Nevada
Financial offices in Reno, including North Valleys and Lemmon Valley, often need support that accounts for both compliance pressure and practical response logistics. From our Ryland Street office, we regularly help businesses review endpoint controls, access policies, and recovery readiness before a local outage turns into a larger reporting or audit problem.
What Financial Offices Should Take Away From a Compliance-Driven Crash
A network crash in a Reno financial office is rarely just a network problem. More often, it is the point where weak documentation, outdated access decisions, and uneven endpoint controls finally interrupt business operations. If the office cannot show who has access, how systems are protected, and how recovery works, both downtime and compliance exposure increase at the same time.
The practical response is to audit the control set before the next outage forces the issue. That means reviewing endpoint coverage, identity controls, exception handling, backup validation, and monitoring workflows as one connected operational system. When those pieces are aligned, firms are in a much better position to keep work moving, support audits, and reduce avoidable disruption.

