Reno Logistics Hub Failure
Seeing operations stopping is often the visible symptom of legacy tools, not the root problem itself. In logistics hubs across Reno, issues like legacy systems, patchwork fixes, and hard-to-adopt tools can quietly undermine endpoint and threat protection until work stops or risk spikes. The fix usually starts with simplifying the stack and making modernization practical.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why the Innovation Wall Stops Logistics Operations
When operations stop in a Reno logistics environment, the immediate failure is usually only the last visible break. The deeper issue is often what we call the Innovation Wall: old hardware, unsupported operating systems, and years of one-off fixes that prevent the business from adopting current cloud platforms, modern endpoint controls, and reliable automation. In warehouse and distribution settings, that shows up as scanner disconnects, label-print failures, stale inventory data, delayed dispatch updates, and workarounds that depend on one or two employees knowing how to keep things moving.
For logistics hubs in North Valleys, Panther Valley, Sparks, and along the I-80 corridor, these failures are amplified by real operating conditions. Buildings with mixed-age wiring, segmented Wi-Fi expansions, and devices that were never designed for current SaaS or AI-assisted workflows create a fragile environment. In practice, effective endpoint and threat protection in Reno is not just about blocking malware. It is about making sure endpoints can stay patched, authenticated, monitored, and usable without breaking the workflow the warehouse depends on. That was the real issue behind Axel’s outage: the stack had become too old and too fragmented to support both production and security at the same time.
- Legacy endpoint capacity: Older workstations, thin clients, and mobile devices often lack the performance headroom for current security agents, browser-based logistics platforms, and cloud synchronization, leading to freezes, dropped sessions, and delayed transactions.
- Patchwork integrations: Barcode systems, shipping portals, shared drives, and line-of-business tools are frequently connected through ad hoc scripts or outdated middleware that fail during updates or network changes.
- Security-control avoidance: Teams sometimes disable protections, postpone patches, or exempt devices from policy because the hardware cannot tolerate modern controls without slowing operations.
- Operational dependency risk: When only a few devices or one aging server hold critical workflows together, a single endpoint issue can interrupt receiving, routing, billing, and customer communication at once.
How to Break the Innovation Wall Without Disrupting the Floor
The right fix is usually staged modernization, not a rushed rip-and-replace. We start by identifying which endpoints are business-critical, which systems are unsupported, and where security controls are being weakened to preserve speed. From there, the goal is to simplify the stack so devices can run current protection, connect cleanly to cloud tools, and fail in a controlled way instead of taking the whole workflow down. That often includes hardware lifecycle planning, policy cleanup, identity hardening, and removing old dependencies that no longer fit the operation.
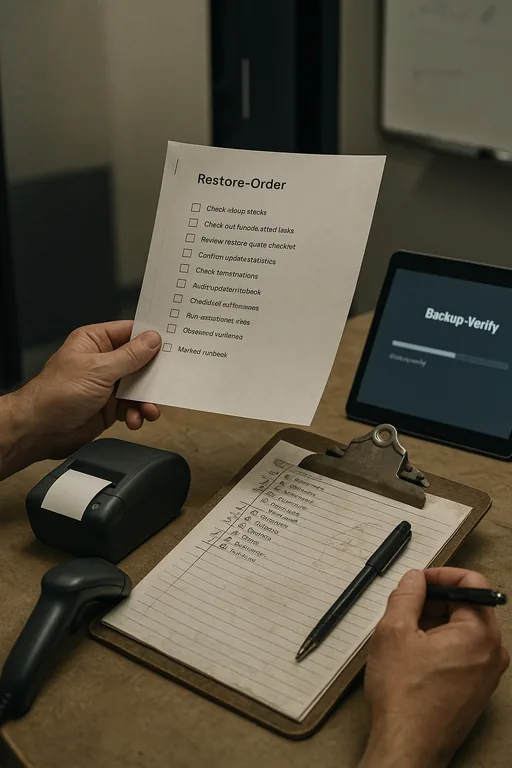
For logistics businesses, resilience also depends on recovery discipline. If a dispatch workstation, file share, or warehouse application fails, the business needs tested rollback points and documented recovery order. That is where backup and recovery programs for multi-shift operations become operationally important, not just a compliance checkbox. Guidance from CISA’s ransomware and resilience resources aligns well with this approach: reduce unsupported systems, validate backups, and make restoration practical under real-world pressure.
- Endpoint standardization: Replace unsupported devices first, align operating systems, and deploy a consistent EDR policy set so protection does not vary by department or device age.
- Identity and access hardening: Enforce MFA, remove stale accounts, and limit local admin rights to reduce the chance that one compromised endpoint becomes a wider warehouse outage.
- Backup validation: Test restores for dispatch data, file shares, and line-of-business systems on a schedule so recovery is measured in hours, not guesswork.
- Network cleanup: Segment warehouse devices, office endpoints, and server resources to contain faults and reduce the blast radius of a bad update or infected system.
Field Evidence: From Manual Workarounds to Stable Throughput
We commonly see this pattern in Northern Nevada industrial corridors where a warehouse has expanded faster than its IT standards. Before remediation, the environment usually depends on aging PCs at shipping stations, inconsistent wireless coverage, and one legacy server carrying too many roles. After standardizing endpoints, validating backups, and improving network, server, and cloud management for warehouse operations , the operation becomes more predictable. Dispatch screens refresh correctly, scanner sessions remain stable, and supervisors stop relying on paper logs to bridge system gaps.
In one comparable Reno-area distribution environment, the before state included recurring morning login delays, failed print jobs during peak outbound windows, and no confidence that a damaged endpoint could be rebuilt quickly. The after state was not flashy; it was operationally cleaner. Devices were replaced in phases, wireless and server dependencies were documented, and recovery order was tested. The result was fewer interruptions during shift changes and a measurable drop in unplanned IT-related stoppages during busy freight periods.
- Result: Unplanned endpoint-related interruptions were reduced by roughly 60 percent over the next quarter, and critical workstation recovery time dropped from most of a day to under 90 minutes.
Reference Points for Logistics Hub Modernization
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Endpoint And Threat Protection and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.

Local Support in Reno and Northern Nevada
Our office on Ryland Street is positioned to support businesses across Reno, including warehouse and logistics operations in Panther Valley and the North Valleys. For sites managing shipping deadlines, receiving windows, and multi-shift staffing, proximity matters, but so does having a plan that reduces the need for emergency visits in the first place. The route below reflects the local service reality for this corridor.
What Logistics Leaders Should Take Away
If a Reno logistics hub keeps running into sudden stoppages, the issue is rarely just one bad device or one isolated outage. More often, the business has reached the point where legacy endpoints, outdated integrations, and uneven security controls can no longer support current operational demands. That is the Innovation Wall in practical terms: the environment cannot move forward without becoming simpler and more supportable.
The operational answer is to reduce complexity, standardize critical systems, and make recovery testable. When endpoint protection, backups, and infrastructure management are aligned, the business is less likely to lose a shift to preventable failures and more likely to keep shipping, receiving, and billing on schedule.

