Reno Logistics Fix
What looks like a one-off issue is often tied to compliance gaps. In logistics hub environments, missing controls, weak documentation, and loose access policies can turn into audit findings, fines, and operational disruption long before anyone notices the warning signs. Closing those gaps early makes security monitoring and response far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Compliance Gaps Stop Logistics Operations
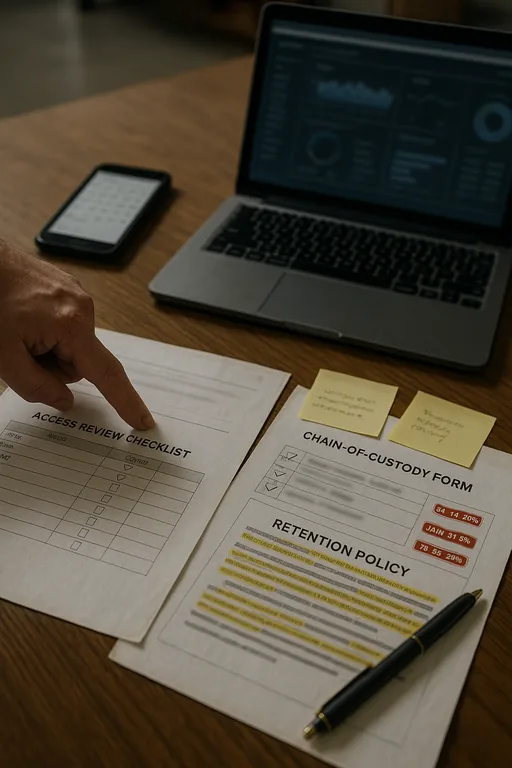
In Washoe County logistics environments, operations usually do not stop because of a single dramatic failure. They stop because small control gaps accumulate until monitoring, access, documentation, and response no longer line up. When regulations such as CMMC, HIPAA, customer security addendums, or internal audit requirements change faster than internal IT documentation, the business ends up running on assumptions instead of verified controls.
We see this most often in facilities managing shipments, inventory movement, handheld devices, shared workstations, and third-party vendor access. A missed account review, incomplete log retention setting, or undocumented exception in a warehouse management workflow can break both compliance and day-to-day operations at the same time. That is why many organizations rely on security monitoring and response in Northern Nevada to connect alerting, access control, and incident handling before a small gap becomes a shutdown. In cases like Shakira’s, the visible symptom is often a lockout or reporting failure, but the root cause is usually weak governance around who has access, what is logged, and how changes are approved.
- Access governance: Shared credentials, stale accounts, and inconsistent role assignments create audit exposure and can force emergency lockouts during active business hours.
- Documentation drift: Policies may say one thing while actual firewall rules, retention settings, and endpoint controls reflect older assumptions.
- Monitoring blind spots: If logs are not centralized or retained correctly, security teams cannot prove what happened during an incident or satisfy an auditor.
- Operational dependency: Logistics teams in Reno, Sparks, and across Washoe County depend on continuous access to scanners, shipping portals, and line-of-business systems, so even short remediation windows have real cost.
Practical Remediation for the Compliance Gap
The fix is not just to patch the immediate issue. The right approach is to identify which controls are required, verify whether they are actually in place, and then align monitoring, documentation, and response procedures around those controls. For logistics hubs, that usually means tightening identity management, validating log collection, reviewing endpoint coverage, and documenting exception handling for shared operational systems.
We typically recommend a structured baseline that includes quarterly access reviews, MFA enforcement for remote and administrative access, tested alert escalation, and evidence retention that matches contractual or regulatory requirements. Businesses that need broader oversight often benefit from managed cybersecurity programs for multi-site operations so compliance work is not separated from the actual security stack. For practical guidance on access control, logging, and incident readiness, the CISA Cybersecurity Performance Goals provide a useful operational reference.
- Identity cleanup: Remove stale accounts, enforce role-based access, and require documented approval for privilege changes.
- Log validation: Confirm that SIEM, firewall, endpoint, and cloud application logs are collected, retained, and reviewed against policy.
- MFA hardening: Apply MFA to VPN, Microsoft 365, admin consoles, and vendor-facing portals that touch shipment or customer data.
- Backup and recovery testing: Validate restore points for operational systems so remediation does not depend on assumptions.
- Policy-to-technology alignment: Match written standards to actual configurations, then document exceptions with ownership and review dates.
Field Evidence: From Audit Exposure to Stable Operations
We worked with a Northern Nevada operation supporting regional distribution traffic where compliance documentation had fallen behind actual system changes. Before remediation, account reviews were inconsistent, alert retention was incomplete, and supervisors were relying on manual checks when exceptions appeared. The site had already experienced intermittent delays whenever a user access issue affected receiving or dispatch.
After a focused remediation effort, the environment was re-baselined around documented access roles, centralized logging, and a defined incident workflow. That included a formal review process tied to compliance-focused IT management , clearer evidence retention, and tested escalation for after-hours alerts. In a corridor where weather, carrier timing, and tight dock schedules already create pressure, reducing internal control failures made a measurable difference.
- Result: Access-related interruptions dropped by 72 percent, audit evidence could be produced in hours instead of days, and incident triage time was reduced from roughly 90 minutes to under 25 minutes.
Compliance Control Reference for Logistics Hubs
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Security Monitoring And Response and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.

Local Support in Washoe County
From our Reno office, we regularly support organizations across Washoe County that need faster response to access failures, audit preparation issues, and monitoring gaps. For sites near South Reno and Mt. Rose Highway, local proximity matters when operations are already delayed and internal teams need practical remediation, not just another report.
Closing the Gap Before Operations Stop
When a logistics hub in Washoe County experiences a sudden access failure, audit issue, or monitoring breakdown, the underlying problem is often a compliance gap that has been building for months. Missing documentation, outdated permissions, and weak evidence retention do more than create regulatory exposure. They interfere directly with receiving, dispatch, reporting, and incident response.
The practical takeaway is straightforward: treat compliance as an operational control set, not a paperwork exercise. When policies, monitoring, access management, and recovery procedures are aligned, the business is easier to defend, easier to audit, and far less likely to lose hours of production to a preventable internal failure.

