Reno Lockout Remediation
Seeing a lockout is often the visible symptom of hidden threats, not the root problem itself. In medical practices across Reno, issues like stolen credentials, MFA gaps, and weak monitoring can quietly undermine managed IT support plans until work stops or risk spikes. The fix usually starts with hardening identity, watching for abnormal behavior, and closing blind spots across users and devices.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why a Medical Practice Lockout Usually Signals a Deeper Identity Problem
A lockout in a Reno medical office is rarely just a lockout. In most cases, it is the first visible symptom of an identity control failure that has already been developing in the background. We often find a mix of reused passwords, weak or inconsistent MFA enforcement, unmanaged mobile access, and sign-in activity that no one is actively reviewing. That aligns with the current threat pattern in healthcare and professional offices: attackers do not need to break through the firewall if they can log in with valid credentials.
For medical practices, the operational impact is immediate. Scheduling slows down, patient intake gets delayed, e-prescribing workflows can stall, and billing teams lose access to systems they need to close the day cleanly. In a local environment like Reno and Sparks, where many clinics run lean staffing models and depend on cloud platforms, one compromised account can ripple across the entire office. That is why structured managed IT support in Reno has to include identity oversight, not just device maintenance. In situations like the one Harrison faced, the lockout is only the visible event; the real issue is the hidden access path that allowed abnormal sign-ins to happen without fast containment.
- Technical factor: Stolen or reused credentials can bypass perimeter defenses when MFA is weak, conditional access is missing, or sign-in anomalies are not being monitored in real time.
- Operational factor: Medical front desks, billing teams, and providers depend on continuous account access, so even a short identity outage disrupts patient flow and revenue capture.
- Local factor: Multi-site coordination between Reno, Sparks, and Carson-area staff often increases account exposure through remote access, mobile devices, and shared administrative workflows.
Practical Remediation for Hidden Access Threats in Healthcare Offices
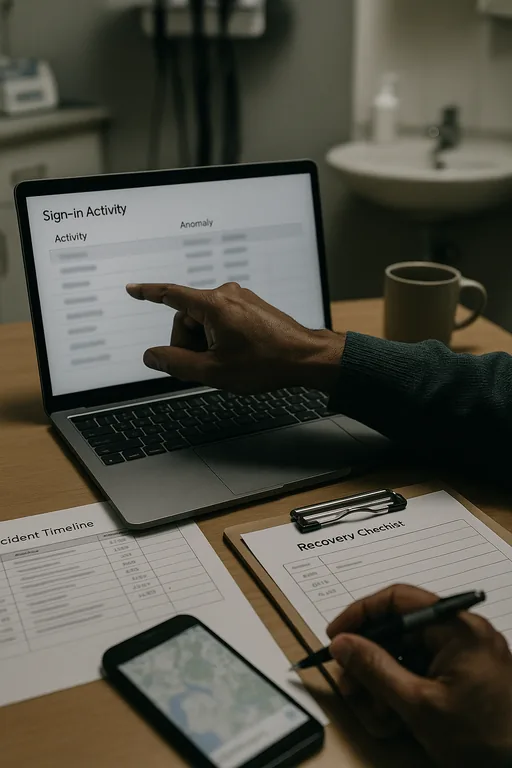
The fix starts with treating identity as a monitored security layer, not a one-time setup item. We typically begin by reviewing sign-in logs, disabling stale sessions, forcing password resets where appropriate, and validating that MFA is enforced for every user, including administrators, billing staff, and third-party support accounts. From there, the environment needs conditional access controls, endpoint visibility, and alerting that can distinguish normal Reno-area activity from suspicious login behavior. This is where broader cybersecurity services in Washoe County become operationally important rather than theoretical.
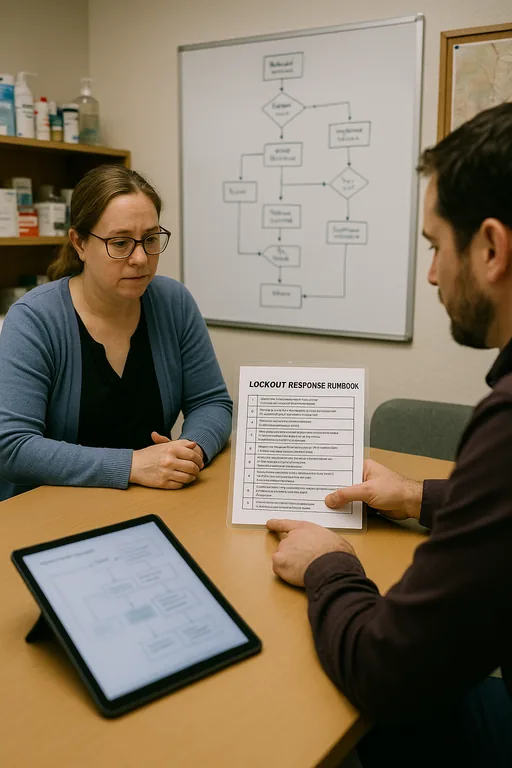
Medical practices also need to verify that recovery steps are documented and tested. If a user is locked out, the office should know who can restore access, how quickly logs can be reviewed, and whether any protected health information may have been exposed. The most useful external guidance on this remains the CISA identity and password security recommendations , especially when paired with MFA hardening and endpoint detection. The goal is not just to get users back in; it is to close the path that caused the incident in the first place.
- Control step: Enforce phishing-resistant MFA where possible, apply conditional access by role and location, and alert on impossible travel, repeated failed sign-ins, and new device registrations.
- Control step: Validate endpoint health before allowing access to cloud applications, especially for laptops used across clinics or from home.
- Control step: Document lockout response, account recovery authority, and escalation paths so front-desk operations do not stall during a live incident.
Field Evidence: Restoring Access Without Repeating the Same Failure
We have seen this pattern in practices operating between central Reno and Sparks business corridors: a user account gets locked, staff assume it is a routine password problem, and only later does log review show suspicious access attempts that had been active before the outage. In one recent healthcare-style environment, the office had cloud email, scheduling, and billing tied too closely to a small number of user accounts with inconsistent MFA enrollment. Before remediation, every lockout created confusion, manual workarounds, and uncertainty about whether the event was accidental or malicious.
After identity controls were tightened, sign-in alerts were tuned, and access review became part of routine oversight, the office moved from reactive resets to controlled response. That also supported compliance-focused IT management by giving leadership clearer evidence of who accessed what, when, and from where. In Northern Nevada healthcare operations, that level of visibility matters because short outages often happen during the busiest patient windows, not after hours.
- Result: Account recovery time dropped from more than two hours of disruption to under 20 minutes, with abnormal sign-in events flagged before they caused another full-office access interruption.
Reference Table: Identity Controls That Reduce Lockout Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed It Support Plans and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.
Local Support in Reno, Sparks, and Northern Nevada
Medical practices in Reno and Sparks often need fast support that accounts for both identity security and the practical realities of local travel, multi-office coordination, and patient-facing downtime. From our Reno office, we regularly support businesses across the Truckee Meadows, including locations near Wild Horse Canyon Drive where a short delay can still disrupt a full clinic schedule. The route below reflects the local service path tied to this type of incident response.
What Medical Practices Should Take Away From a Lockout Event
If a medical practice in Reno gets locked out, the right response is to assume there may be a deeper identity or monitoring gap behind the event. The visible outage matters, but the larger issue is whether stolen credentials, weak MFA enforcement, or unmanaged endpoints were already creating risk before anyone noticed. That is why remediation has to go beyond password resets and focus on access controls, alerting, and documented recovery steps.
For healthcare offices, the practical goal is simple: keep patient-facing operations moving while reducing the chance that the same hidden threat returns next week. When identity is treated as a core operational control, lockouts become faster to contain, easier to investigate, and less likely to turn into a billing, compliance, or continuity problem.

