Reno Law Firm Tech
This kind of issue rarely appears all at once. For law firms in Northern Nevada, it usually builds through phishing clicks, password reuse, and weak account hygiene and then surfaces as systems going down, slower recovery, or higher exposure. A more reliable setup starts with tightening identity controls and building safer day-to-day habits.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Human Error Still Brings Legal Systems Down
For most law firms, systems do not fail because of a dramatic infrastructure collapse. They fail because a routine user action opens the door to account compromise, mailbox takeover, or unauthorized access that then disrupts the rest of the environment. In Northern Nevada, we often see this start with a phishing email, password reuse between business and personal accounts, or weak sign-in habits around Microsoft 365, remote access tools, and case management platforms.
The human element matters because legal operations depend on identity. If email is compromised, intake slows down, court notices can be missed, document sharing becomes risky, and trust in the environment drops immediately. Once attackers gain a foothold through a user account, they often move laterally into file shares, cloud storage, and administrative tools. That is why firms dealing with recurring login issues, suspicious sign-in activity, or delayed detection usually need stronger security monitoring and response in Northern Nevada rather than relying on antivirus alone. In cases like Mya’s, the visible outage is only the final symptom of a much earlier control failure.
- Identity exposure: A single compromised mailbox can trigger account lockouts, MFA fatigue, unauthorized forwarding rules, and broader access instability across legal staff.
- Password reuse: Reused credentials increase the chance that a breach from another service will affect firm email, VPN access, or cloud applications.
- Delayed detection: Without active alerting and review, suspicious sign-ins may continue long enough to disrupt calendars, intake, billing, and document workflows.
- Operational dependency: Law firms in Reno, Sparks, and Carson City often rely on a small number of key users, so one compromised account can interrupt the whole office faster than many leaders expect.
Practical Controls That Reduce Downtime and Exposure
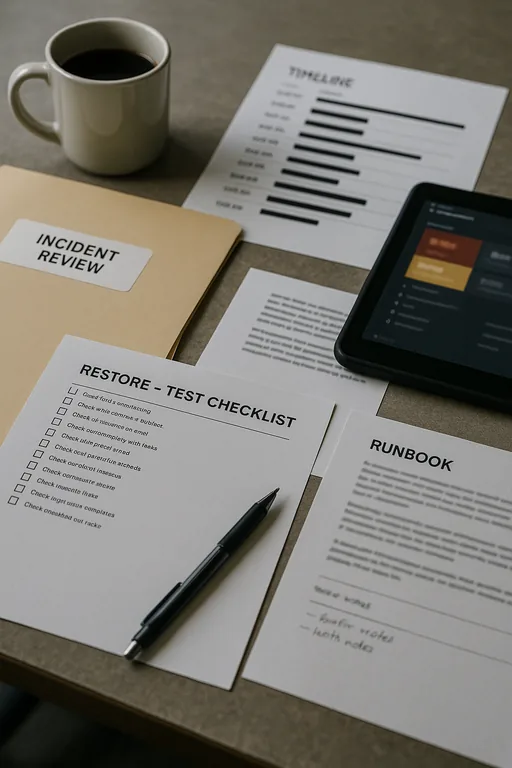
The fix is not a single product. It is a layered operating model that assumes users will occasionally click the wrong link and then limits what happens next. We typically start by reviewing identity controls, mailbox rules, MFA enforcement, endpoint visibility, and backup readiness. For legal offices, this also means confirming that document repositories, shared drives, and cloud platforms can be restored cleanly if an account compromise turns into a broader incident.
From there, the goal is to shorten detection time and contain the blast radius. That includes stronger conditional access, phishing-resistant MFA where practical, alert tuning, and tested backup and recovery programs for business continuity . The technical baseline should align with practical guidance from CISA , especially around password hygiene, MFA, and phishing resistance.
- MFA hardening: Require MFA across email, remote access, and cloud apps, and reduce approval fatigue with better sign-in policies and device trust controls.
- Mailbox protection: Audit forwarding rules, legacy authentication, and impossible-travel alerts to catch account misuse early.
- Endpoint visibility: Use EDR and centralized alerting so suspicious activity on one workstation does not stay isolated and unnoticed.
- Backup validation: Test file, server, and cloud recovery regularly so a compromised account does not become a prolonged outage.
- User conditioning: Run short, repeatable awareness training tied to the exact email lures staff are seeing, not generic annual modules.
Field Evidence: Account Compromise Contained Before File Access Spread
We recently worked through a pattern common in the Reno legal corridor: a small office with Microsoft 365, shared file storage, and a few remote users had repeated sign-in prompts and unexplained mailbox behavior after a phishing event. Before controls were tightened, staff lost time resetting passwords, checking sent mail, and confirming whether client communications had been altered. The firm also had gaps in server oversight and cloud administration that made it harder to verify what had been touched.
After identity cleanup, alert tuning, and better IT systems for multi-location operations , the environment became easier to monitor and recover. The office regained stable access, reduced false lockouts, and had a clearer escalation path when suspicious activity appeared. In a region where weather events, travel between offices, and small in-house teams can slow response, that operational clarity matters.
- Result: Unauthorized mailbox activity was contained the same day, password reset volume dropped by more than 60 percent over the next quarter, and recovery confidence improved because cloud and file access were documented and tested.
Reference Points for Reducing Human-Driven Security Failures
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Security Monitoring And Response and has spent his career building practical recovery, security, and operational continuity processes for businesses across Northern Nevada and Northern Nevada.

Local Support in Northern Nevada
We support firms throughout Reno and the surrounding Northern Nevada area, including offices that need fast response between downtown Reno, South Reno, and nearby business corridors. For legal practices near Lakeridge Shores, the travel window from our Ryland Street office is typically about 13 minutes, which helps when account access issues or workstation failures need on-site validation alongside remote containment.
What Law Firms Should Take Away
When a law firm in Northern Nevada reports that systems are down, the root cause is often not a server failure by itself. More often, it is weak account hygiene, a successful phishing click, or poor visibility into identity activity that allowed a small mistake to become an operational disruption. For legal offices, that affects intake, communication, billing, and client confidence very quickly.
The practical answer is to treat user behavior as part of the security stack. Stronger identity controls, monitored endpoints, tested recovery, and clear response procedures reduce both downtime and uncertainty. That approach is more effective than waiting for the next lockout or mailbox incident to reveal the same gap again.

