Reno Law Firm IT Risks
When a business is dealing with systems going down, the failure usually started earlier. Unclear ownership, overlapping tools, and fragmented support can weaken managed cybersecurity programs over time and leave law firms in The Truckee Meadows exposed when pressure hits. Addressing the problem means clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Vendor Chaos Turns Into Systems Down Events
When systems go down at a law firm in The Truckee Meadows, the immediate assumption is often that the internet failed or a server crashed. In practice, we usually find a coordination failure first. Internet, phones, Microsoft 365, line-of-business applications, endpoint security, and backup tools may all be working under separate contracts with separate support desks. That structure leaves nobody clearly accountable for incident ownership, especially when the issue crosses more than one platform.
This is where The Vendor Chaos becomes a real operational risk. An office manager is left chasing carriers, software support, copier vendors, and workstation providers while attorneys are waiting on case files and staff cannot move intake or billing forward. For firms trying to stabilize risk, structured managed cybersecurity programs in Northern Nevada help by assigning ownership, standardizing alerts, and making sure one team can coordinate the full response path. In situations like Corey’s, the outage itself was only part of the damage; the larger problem was that nobody had authority to drive triage from first alert through recovery.
- Fragmented escalation: Separate vendors often troubleshoot only their own piece, which slows root-cause isolation when the real issue spans identity, connectivity, endpoint controls, and application access.
- Overlapping tools: Multiple security or remote-management products can create blind spots, duplicate alerts, or conflicting policies that make recovery harder during a live incident.
- Operational bottlenecks: Law firms depend on document access, calendaring, email, and voice systems at the same time, so even a partial failure can interrupt intake, deadlines, and billing.
- Local support realities: Across Reno, Sparks, and nearby office corridors, response time is affected by building access, carrier handoffs, and whether anyone onsite can identify the actual point of failure.
How To Restore Control And Reduce Repeat Downtime
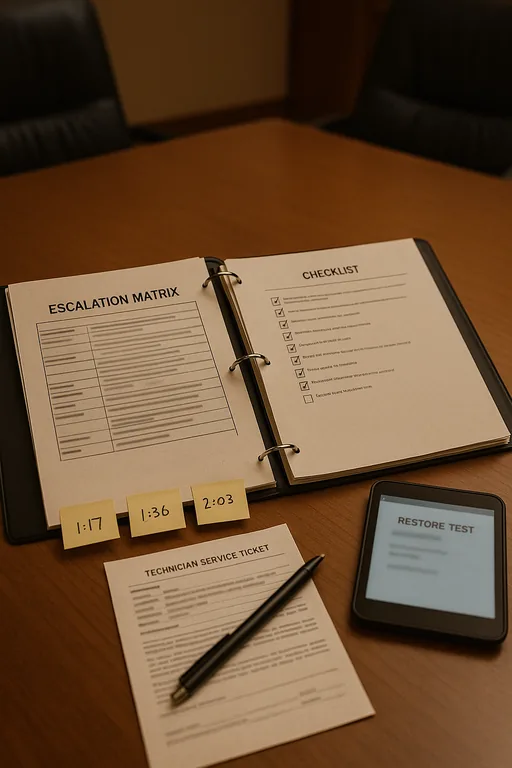
The fix is not adding more vendors. It is establishing a single operating model for ownership, escalation, and technical standards. We typically start by mapping every dependency: ISP, firewall, switches, wireless, VoIP, Microsoft 365, legal software, endpoint protection, backup, and remote access. From there, each system gets a named owner, a documented escalation path, and a clear definition of what triggers after-hours response. Firms that need this level of clarity often benefit from a formal technology advisory and assessment process to identify where support overlap and accountability gaps are creating avoidable risk.
Remediation also needs technical controls, not just better phone numbers. That means validating backups, reviewing MFA enforcement, checking endpoint detection coverage, confirming network segmentation where appropriate, and making sure alerting reaches the right people in the right order. For law firms handling sensitive client data, the CISA ransomware guidance is a practical reference because it ties incident readiness directly to access control, backup integrity, and recovery planning.
- Single incident owner: Assign one accountable team to coordinate all vendors during outages so the office is not forced to manage technical handoffs in real time.
- Escalation matrix: Document who handles internet, voice, identity, endpoint, and application failures, including after-hours contacts and decision thresholds.
- Backup validation: Test restore capability on legal documents, shared drives, and cloud data instead of assuming backup jobs equal recoverability.
- MFA and endpoint hardening: Enforce stronger identity controls and verify EDR coverage so a systems-down event does not become a security incident.
Field Evidence: Stabilizing A Multi-Vendor Law Office
We worked through a similar pattern with a professional office operating between central Reno and south Reno corridors where recurring outages were being blamed on whichever vendor answered the phone last. Before cleanup, the firm had no unified escalation list, inconsistent admin access, and no reliable way to tell whether the problem started with the ISP, firewall, Microsoft 365, or a line-of-business application. After consolidating documentation, assigning incident ownership, and aligning support expectations, the office moved from reactive vendor chasing to a defined response process.
One of the most important improvements was strategic governance. Instead of letting each renewal or tool decision happen in isolation, the firm adopted IT strategy engagements for multi-vendor operations so technology decisions supported continuity, security, and legal workflow requirements together. In Northern Nevada, where firms often rely on a mix of local carriers, cloud platforms, and specialized legal software, that planning step materially reduces confusion during live incidents.
- Result: Incident triage time dropped from more than 2 hours of vendor back-and-forth to under 30 minutes, and repeat service interruptions were reduced over the next quarter through clearer ownership and tested recovery steps.
Reference Points For Law Firms Managing Vendor Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Cybersecurity Programs and has spent his career building practical recovery, security, and operational continuity processes for businesses across The Truckee Meadows and Northern Nevada.

Local Support in The Truckee Meadows
We regularly support firms across Reno, Sparks, and nearby business corridors where legal offices depend on stable access to case files, email, phones, and cloud applications. From our Reno location, the Kietzke corridor is a straightforward service route, but the larger value is not drive time alone. It is having a clear operating model before an outage starts so vendor confusion does not slow recovery.
Clear Ownership Prevents Small Gaps From Becoming Full Outages
For law firms in The Truckee Meadows, systems-down incidents are often less about one broken device and more about unmanaged complexity. When internet, phones, software, security, and support contracts are all moving independently, downtime lasts longer because nobody owns the whole event. That creates unnecessary exposure for billing, client communication, and document access.
The practical takeaway is straightforward: define ownership, simplify escalation, validate recovery, and align vendors under one operating plan. Firms that do this are in a much better position to contain outages before they become larger security or compliance problems.

