Reno Law Firm Downtime
Problems like this tend to stay hidden until something important breaks. For law firms in South Meadows, that often means systems going down, avoidable delays, or a bigger recovery burden than expected. The best response is validating backups regularly and proving recovery before a real outage.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why Backup Copies Fail the Real Resilience Test

For a South Meadows law firm, the main question is straightforward: why do systems still go down if backups exist? The answer is that a backup is only a stored copy of data. Business continuity is the ability to keep working, restore in the right order, and bring users back online without guessing. We see this gap often when firms assume that successful backup jobs mean they are protected, even though no one has tested whether document management, case files, mapped drives, Microsoft 365 access, security tools, and line-of-business applications can actually be restored together.
That is where the resilience test matters. If a restore has never been validated, the firm may discover too late that the image is incomplete, the credentials are outdated, the backup excludes a critical application folder, or the restored server cannot communicate properly with endpoint controls. In legal environments, that quickly turns into intake delays, missed filing preparation, billing disruption, and staff working from memory instead of records. Firms trying to reduce that exposure usually need stronger endpoint and threat protection in Reno because recovery is not just about getting data back; it is about restoring a trusted and usable operating state.
- Untested restore sequence: A backup may contain data, but if the firm does not know which systems must come back first, users can remain locked out even after the server is technically restored.
- Missing dependencies: Document systems, authentication, shared drives, and security agents often rely on each other, and one missing component can stall the entire recovery.
- Endpoint trust failure: Restored machines may trigger security conflicts, outdated policies, or broken agent communication if the environment was never tested end to end.
- Operational blind spots: Vincent’s situation is common because firms often test whether backups ran, not whether attorneys and support staff can resume work under real outage conditions.
How Law Firms Close the Recovery Gap Before the Next Outage
The practical fix is to move from passive backup retention to active recovery validation. That means scheduling restore tests, documenting recovery order, confirming application dependencies, and measuring how long it actually takes to return attorneys and staff to productive work. For firms in South Meadows and across the Reno area, this usually starts with a review of backup scope, retention, authentication dependencies, and whether the recovery plan reflects how the office really operates day to day.
We typically recommend pairing security controls with structured backup and disaster recovery for Reno businesses so the firm can validate both data restoration and secure system re-entry. A useful benchmark is guidance from CISA’s ransomware resilience and recovery guidance , which emphasizes tested backups, protected recovery paths, and documented restoration procedures rather than assumptions.
- Restore testing cadence: Run scheduled file-level and full-system restore tests, then document actual recovery times and failure points.
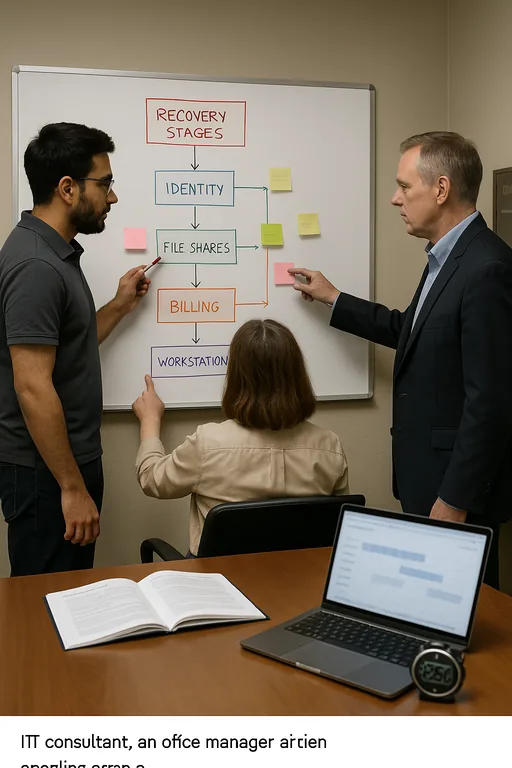
- Recovery order mapping: Identify what must return first, such as identity services, file shares, legal applications, print services, and billing systems.
- Endpoint control validation: Confirm EDR, antivirus, and policy enforcement tools reconnect correctly after restoration so recovered systems are not left exposed or quarantined unnecessarily.
- Immutable backup design: Use protected retention and isolated copies to reduce the chance that malware or admin error affects every backup set.
Field Evidence: South Reno Recovery Validation After a Server Failure
In one Northern Nevada engagement, a professional office corridor near South Reno had backups in place but no documented proof that a full restore would support normal operations. Before remediation, the environment depended on a single server image, inconsistent application backup coverage, and no verified recovery sequence. A power event and storage fault exposed the weakness immediately: data existed, but users could not authenticate cleanly, shared folders came back out of order, and security agents required manual repair.
After rebuilding the process, the firm adopted staged restore testing, dependency mapping, and a separate review of backup integrity for both server workloads and workstation data. We also added managed backup solutions for multi-user offices to improve retention visibility and restore consistency. The next validation cycle produced a controlled recovery with documented timing, fewer manual steps, and a much clearer handoff between IT and office leadership.
- Result: Verified recovery time dropped from an uncertain same-day outage window to a tested 2-hour core-system restoration target, with billing access and shared matter files restored in the correct order.
Resilience Test Reference Points for Law Firm Systems
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Endpoint And Threat Protection and has spent his career building practical recovery, security, and operational continuity processes for businesses across South Meadows, Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.
Local Support in South Meadows, Reno, Sparks, Carson City, and Northern Nevada
Our office in downtown Reno supports firms across South Meadows and the broader Northern Nevada corridor. For businesses dealing with backup validation, recovery planning, or endpoint protection concerns, local response matters, but tested process matters more. The route shown below reflects the practical service relationship between our Reno office and the Mogul area destination referenced in this article.
The Operational Takeaway for South Meadows Law Firms
If a law firm has backups but has never proven a full recovery, it still has a resilience gap. The real risk is not just data loss. It is the inability to restore the right systems, in the right order, with security controls intact and staff able to work. That is why restore testing, dependency mapping, and endpoint validation belong in the same conversation.
For firms in South Meadows, the practical standard is simple: do not assume a successful backup job equals business continuity. Measure recovery, document it, and test it often enough that an outage becomes a controlled event instead of an improvised one.

