Reno Law Firm Cyber
Seeing systems going down is often the visible symptom of hidden threats, not the root problem itself. In law firms across Reno, issues like stolen credentials, MFA gaps, and weak monitoring can quietly undermine managed backup solutions until work stops or risk spikes. The fix usually starts with hardening identity, watching for abnormal behavior, and closing blind spots across users and devices.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why “Systems Down” Is Often an Identity Problem First
When a Reno law firm reports that systems are down, the visible outage is often only the last stage of the problem. In many cases, the real issue starts earlier with stolen credentials, incomplete MFA coverage, reused passwords, or a user account that begins authenticating in ways nobody is watching. Modern attackers do not always force entry through the perimeter. They log in with valid credentials, move quietly, and interfere with file access, cloud applications, and backup workflows in ways that can look like ordinary technical failure.
That matters for legal operations because document access, time entry, email, and case management are tightly connected. If identity is compromised, even strong backup tooling can be undermined by unauthorized deletions, retention changes, or encrypted file sync activity before anyone recognizes the pattern. We often see firms improve resilience by pairing backup strategy with managed backup solutions in Reno that are monitored alongside user behavior, endpoint health, and administrative access. In the kind of incident Cristian faced, the outage was only the symptom; the hidden threat was already active inside normal business systems.
- Credential misuse: A valid user login can bypass firewall assumptions, access cloud data directly, and disrupt legal workflows before traditional outage checks show a clear root cause.
- MFA gaps: Partial MFA deployment leaves service accounts, legacy apps, or remote access paths exposed even when leadership believes MFA is already in place.
- Weak monitoring: Without alerting on impossible travel, unusual file activity, or privilege changes, firms may not detect the hidden threat until staff can no longer work.
- Backup blind spots: Backups may exist, but if retention, immutability, or restore validation are weak, recovery can be slower and riskier than expected.
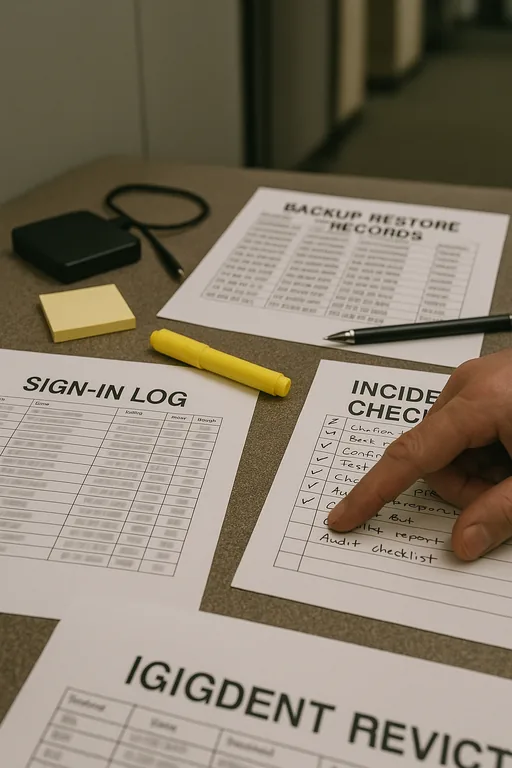
Practical Remediation for Law Firms That Need Work to Keep Moving
The fix is not just restoring data and moving on. The first step is to contain identity risk by forcing password resets where appropriate, reviewing sign-in logs, removing unauthorized sessions, tightening conditional access, and verifying MFA on every user and privileged account. From there, endpoint telemetry, email security, and backup integrity all need to be checked together. For firms with multiple offices, remote staff, or cloud-heavy document workflows, stable recovery also depends on disciplined network infrastructure management for Reno legal operations so authentication, file access, and failover paths behave predictably under stress.
We also recommend aligning remediation with practical guidance from CISA’s MFA recommendations , especially where legal data, remote access, and administrative privileges overlap. In many environments, the most effective improvements are straightforward: remove legacy authentication, deploy EDR across all endpoints, validate backup restores on a schedule, separate admin accounts from daily-use accounts, and tune alerting so unusual behavior is reviewed before it becomes downtime.
- Identity hardening: Enforce MFA everywhere, disable legacy protocols, and separate privileged access from standard user activity.
- Endpoint visibility: Deploy EDR and alerting that can flag suspicious sign-ins, encryption behavior, and lateral movement quickly.
- Backup validation: Test restores regularly, protect backup repositories, and confirm retention cannot be altered by compromised user credentials.
- Access control review: Audit shared mailboxes, document repositories, and line-of-business permissions to reduce unnecessary exposure.
- Network stability: Segment critical systems and document traffic paths so recovery does not depend on a flat, loosely controlled environment.
Field Evidence: Hidden Login Activity Behind a “Backup Failure” Report
We worked through a similar pattern for a professional office corridor environment in the Reno-Sparks market where staff initially believed the backup platform had failed because files were unavailable and restore points looked inconsistent. The actual issue was unauthorized account activity combined with sync disruption and poor alerting. Before remediation, users experienced repeated lockouts, missing document versions, and uncertainty around what data was trustworthy. After identity controls were tightened, restore testing was completed, and the environment was reviewed with stronger server and hybrid infrastructure oversight , the firm regained stable access and a clearer recovery path.
- Result: Restore confidence improved, suspicious sign-in activity was contained, and unplanned file-access disruption dropped from repeated daily incidents to zero during the following quarter.
Reference Points for Law Firm Outage Investigation
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Backup Solutions and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in Reno and Northern Nevada
Law firms in Reno often need fast, practical response when authentication problems, backup concerns, or file access issues interrupt billable work. From downtown offices to business parks and multi-site legal operations, local support matters because recovery depends on both technical depth and familiarity with how firms actually work across Northern Nevada.
What Law Firms Should Take Away
If systems go down in a Reno law firm, it is worth assuming the visible outage may be covering a deeper identity or monitoring problem. Stolen credentials, weak MFA coverage, and poor visibility can quietly interfere with backups, file access, and normal legal workflows long before anyone labels it a security event.
The operational answer is to treat backup, identity, endpoint monitoring, and infrastructure as one continuity system. When those controls are reviewed together, firms are in a much better position to reduce downtime, protect client data, and keep billable work moving even when something abnormal starts in the background.

