Reno Encryption Fail
Problems like this tend to stay hidden until something important breaks. For manufacturing plants in South Meadows, that often means encrypted files, avoidable delays, or a bigger recovery burden than expected. The best response is simplifying the stack and making modernization practical.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why the Innovation Wall Leads to Encrypted Files
The direct answer is that encrypted files in a South Meadows manufacturing plant are usually not caused by one bad click alone. They are more often the result of an environment that has stopped evolving. The Innovation Wall shows up when old hardware, unsupported operating systems, aging line-of-business applications, and temporary workarounds prevent a business from adopting current security and recovery practices. Once that happens, ransomware or other malware does not have to defeat a strong system. It only has to find the weak point everyone has been working around.
We see this often in manufacturing environments where uptime matters more than planned modernization, so old systems stay in place long after they should have been retired. A plant may still rely on a 2019-era server, flat network design, shared local admin credentials, or an outdated NAS that cannot support proper immutability or alerting. That creates a gap between how the business operates and what current security tools expect. In practice, businesses dealing with recurring instability often need structured IT support and help desk for Reno-area operations so issues are found before they become a file encryption event. In a case like Corey’s, the visible outage was only the final symptom of years of deferred cleanup.
- Legacy infrastructure: Older servers, unsupported endpoints, and aging storage platforms often cannot run current endpoint protection, modern authentication controls, or reliable backup agents.
- Patchwork remote access: Temporary VPN changes, exposed RDP paths, and unmanaged vendor access create openings that are easy to miss during day-to-day operations.
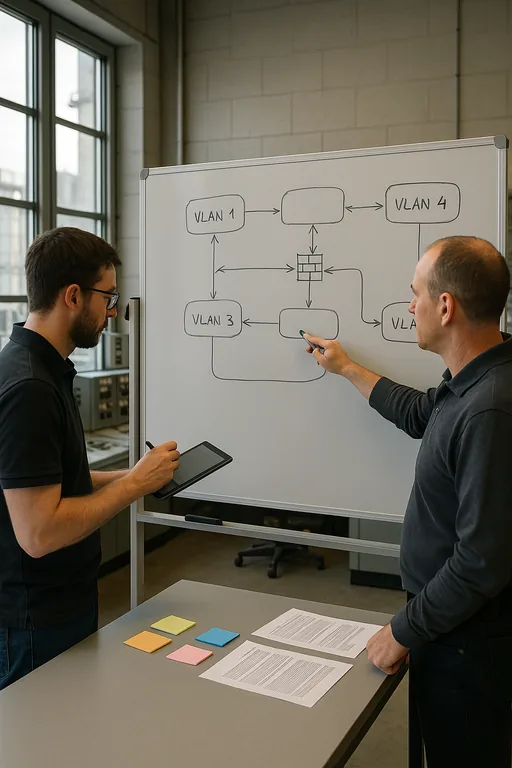
- Flat network design: When office systems, production support devices, and shared file repositories all sit on the same broad network, malware can move farther than it should.
- Operational pressure: South Meadows plants often prioritize keeping production moving, which can delay maintenance windows, firmware updates, and system replacement decisions.
Practical Remediation for Manufacturing Environments
The fix is not chasing every new tool. It is reducing complexity and rebuilding control where it matters. We typically start by identifying what is still business-critical, what is merely old, and what has become a hidden liability. That means isolating production-adjacent systems, removing unsupported endpoints, validating backup integrity, and tightening identity controls so one compromised account cannot expose the entire file environment.
For plants with compliance obligations, insurance requirements, customer audit pressure, or contractual security language, this work should be tied to documented governance. A structured approach such as compliance-focused IT management helps leadership prioritize which controls must be implemented first and which legacy systems need compensating safeguards until replacement is complete. External guidance from CISA’s ransomware resources is also useful because it aligns technical hardening with practical incident response steps.
- Network segmentation: Separate office users, production support systems, backup infrastructure, and vendor access paths with VLANs and access control rules.
- MFA hardening: Enforce multifactor authentication for email, VPN, admin access, and remote support tools, especially where older systems created exceptions.
- EDR deployment: Standardize endpoint detection and response across supported workstations and servers so suspicious encryption behavior is caught early.
- Backup validation: Test restores, verify retention, and keep at least one protected recovery path that cannot be altered by the same credentials used in production.
Field Evidence: South Reno Manufacturing Recovery Pattern
Before remediation, the environment depended on a mix of aging Windows systems, broad file share permissions, and backup jobs that reported success without regular restore testing. The business could still run, but every change introduced more friction. A single malware event then disrupted scheduling files, purchasing records, and quality documentation needed for same-day production decisions.
After cleanup, the plant moved critical shares to a supported platform, segmented user and operations traffic, enforced MFA on remote access, and documented restore procedures against realistic outage scenarios. In one Northern Nevada corridor where weather, vendor travel time, and multi-building layouts can slow response, that preparation matters. The final layer was backup and disaster recovery planning built around verified recovery points instead of assumptions.
- Result: Recovery time for critical file access dropped from most of a workday to under 90 minutes, and unauthorized lateral movement paths were materially reduced.
Manufacturing IT Risk Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in It Support And Help Desk and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.
Local Support in Reno and Northern Nevada
From our Reno office, we regularly support manufacturers, professional offices, and multi-site organizations that need practical response times and clear operational guidance. The route below reflects the local service reality for organizations near the Dandini area and across the broader Reno market, where travel time, building layout, and business continuity planning all affect how quickly an issue can be contained.
Modernization Has to Reduce Risk, Not Add More Complexity
When files get encrypted in a manufacturing environment, the immediate issue is recovery, but the larger issue is usually architectural drift. Legacy hardware, temporary fixes, and unsupported tools create an environment where security controls are inconsistent and recovery becomes slower than the business can tolerate. That is the real Innovation Wall.
For South Meadows manufacturers, the practical path forward is straightforward: identify what is outdated, isolate what cannot yet be replaced, validate recovery, and align support with how the plant actually operates. Businesses do not need a dramatic overhaul all at once. They need a controlled plan that removes hidden failure points before the next interruption reaches production.

