Reno Encrypt Threat
Problems like this tend to stay hidden until something important breaks. For manufacturing plants in South Meadows, that often means encrypted files, avoidable delays, or a bigger recovery burden than expected. The best response is hardening identity, watching for abnormal behavior, and closing blind spots across users and devices.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Encrypted Files Often Start with a Login, Not a Break-In
When a manufacturing plant in South Meadows finds encrypted files, the visible problem is usually the last stage of the incident. The earlier stages are quieter: a reused password, a successful phishing login, a stale admin account, or remote access that was never tightened after a vendor project. That is why the invisible threat matters. Modern attackers often do not need to defeat the firewall. They sign in with valid credentials, blend into normal traffic, and move toward file shares, ERP data, and production support systems that the perimeter never flags as suspicious.
We see this most often in environments where operations depend on a mix of office users, plant-floor devices, vendor access, and older systems that cannot easily support modern controls. In that setting, one compromised identity can reach much farther than leadership expects. For organizations trying to reduce that exposure, compliance advisory programs in Northern Nevada help map where access, retention, and recovery controls are not aligned with actual business risk. That gap is often what turns a single stolen login into encrypted engineering files, delayed shipments, and reporting problems.
The operational consequence is not limited to downtime. If quality documents, shipping records, or maintenance files are locked, supervisors start working from memory, staff create side spreadsheets, and traceability weakens. That is where incidents become expensive. In Wendy’s case, the file encryption was only the symptom. The root issue was that the account activity looked legitimate long enough to avoid immediate detection.
- Credential misuse: Stolen usernames and passwords can let an attacker access file shares, remote tools, and cloud-connected systems without triggering a classic perimeter alarm.
- Flat access paths: When office networks, file servers, and production support resources are too broadly connected, one compromised account can affect multiple departments quickly.
- Limited behavioral visibility: If no one is watching for unusual sign-in patterns, mass file changes, or after-hours access, encryption activity is often discovered only after users report broken files.
Practical Remediation for Manufacturing Environments
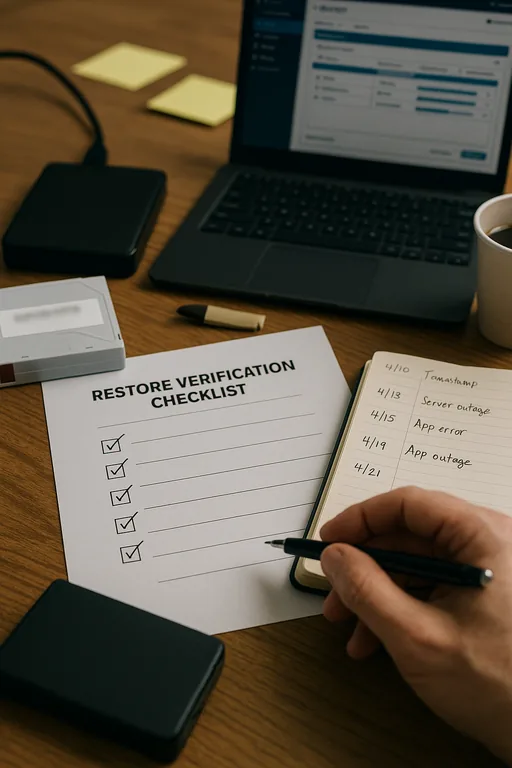
The right response is not just restoring data and moving on. Plants in South Meadows need to contain the account path that allowed the encryption event, verify what was touched, and reduce the chance of repeat access. That usually starts with forced credential resets, MFA review, endpoint isolation, and a timeline of sign-in activity across Microsoft 365, VPN, remote support tools, and local servers. From there, backup integrity has to be validated before any broad restore begins. Businesses that want faster recovery under pressure usually benefit from backup and recovery programs built for operational continuity rather than backup jobs that only appear healthy on paper.
We also recommend separating plant-floor dependencies from general office access where possible, tightening privileged accounts, and alerting on unusual file modification volume. If the environment includes regulated records, retention and access controls should be reviewed against documented requirements, not assumptions. Guidance from CISA’s ransomware guidance remains practical here because it focuses on identity protection, segmentation, tested recovery, and incident response discipline rather than one product fix.
- MFA hardening: Require phishing-resistant or app-based MFA for remote access, email, admin accounts, and vendor connections.
- Backup validation: Test restore points for file shares, ERP support data, and critical documentation so recovery time is known before an incident.
- Segmentation and alerting: Limit lateral movement between user networks and critical systems, and alert on abnormal sign-in behavior and mass encryption patterns.
Field Evidence: Quiet Credential Abuse Before File Encryption
In one Northern Nevada manufacturing corridor engagement, the initial complaint was simple: users could see folders, but key files would not open and several naming conventions had changed overnight. Before remediation, the environment had broad share permissions, inconsistent MFA enforcement, and no reliable alerting for unusual after-hours access. The affected team was also relying on a backup schedule that had not been tested against real recovery objectives.
After containment, restore validation, and access cleanup, the organization moved critical shares behind tighter permissions, reduced standing admin rights, and improved visibility across servers and cloud sign-ins. They also added network, server, and cloud management for multi-site operations so abnormal behavior could be investigated before users noticed broken files. That matters in Washoe County where plants often coordinate with suppliers, front offices, and remote decision-makers across separate locations.
- Result: Recovery time for critical shared data dropped from more than a business day to under 3 hours, and suspicious sign-in events began generating actionable alerts instead of being discovered by end users.
Reference Points for Reducing File Encryption Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Compliance Advisory Programs and has spent his career building practical recovery, security, and operational continuity processes for businesses across South Meadows, Reno, Sparks, and Northern Nevada and Northern Nevada.

Local Support in South Meadows, Reno, Sparks, and Northern Nevada
Reno Computer Services supports manufacturers and other operationally sensitive businesses across the Reno-Sparks area, including South Meadows and Spanish Springs. For plants dealing with encrypted files, identity misuse, or recovery concerns, local response matters because coordination often involves office staff, production leadership, outside vendors, and backup systems at the same time.
What Manufacturing Leaders Should Take Away
Encrypted files in a South Meadows manufacturing environment usually point to a broader control failure, not just a bad workstation or a one-time outage. The common pattern is hidden credential abuse, weak visibility, and recovery assumptions that were never tested under real operating pressure. Once that is understood, the response becomes more disciplined: contain identity risk, verify backups, reduce lateral movement, and improve monitoring where abnormal behavior starts.
For plant operators, the practical goal is straightforward. Keep documentation, scheduling, and production support systems available even when a user account is compromised. That requires technical controls, but it also requires operational clarity about who has access, what must be restored first, and how quickly the business can tolerate disruption.

