Reno Data Breach Risk
Seeing a data breach is often the visible symptom of growth outpacing IT capacity, not the root problem itself. In construction firms across Reno, issues like endpoint sprawl, underplanned infrastructure, and inconsistent standards can quietly undermine governance policy and audit preparation until work stops or risk spikes. The fix usually starts with standardizing how new users, devices, and systems are brought online.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why a Data Breach Often Signals a Scalability Ceiling
For construction firms in Reno and Sparks, a breach rarely starts with a single bad click alone. More often, it starts when hiring, project growth, and device expansion move faster than IT standards. New estimators, project managers, superintendents, tablets, and laptops get added quickly, but account permissions, endpoint policies, and documentation do not stay aligned. That is the scalability ceiling risk: the business keeps growing, but the operating model underneath it does not.
We typically see this show up first in governance gaps rather than dramatic system failure. A firm may have acceptable tools in place, but no consistent process for provisioning users, separating project data, reviewing access, or validating audit readiness. In that environment, a breach becomes the visible symptom of weak control over change. Construction companies that need stronger governance policy and audit preparation in Reno are usually dealing with exactly this pattern. The issue is not just security; it is whether the business can add the next 10 people without breaking file access, reporting, or compliance discipline. That is what caught up with Angie’s team.
- Endpoint sprawl: Laptops, mobile devices, and shared workstations multiply across trailers, yards, and offices, but enrollment and security baselines are applied inconsistently.
- Permission drift: Users inherit access from prior projects or roles, creating unnecessary exposure to bid files, HR records, or financial data.
- Underplanned infrastructure: File systems, VPN access, and identity controls are often built for a smaller headcount and become unstable as teams expand.
- Audit friction: When standards are informal, it becomes difficult to prove who had access, when controls changed, and whether required safeguards were actually enforced.
How to Remediate the Capacity and Control Problem
The practical fix is to standardize onboarding, access control, and system oversight before the next hiring wave. That means every new user, laptop, mobile device, and cloud application should follow the same documented process: approved request, role-based access, endpoint enrollment, MFA enforcement, logging, and verification. For firms adding crews, estimators, and back-office staff across Reno, Sparks, and Carson City, this is where structured IT operations management for multi-site operations becomes necessary rather than optional.
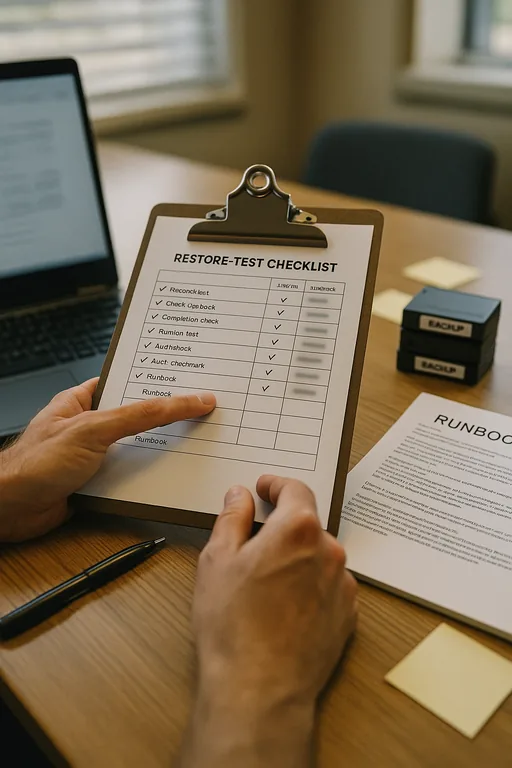
Remediation also needs technical depth. We recommend role-based groups instead of one-off permissions, EDR on all endpoints, conditional access for remote logins, backup validation for project data, and quarterly access reviews tied to active jobs and departments. If the firm handles regulated information, the control set should map to a recognized framework such as the CISA Cybersecurity Performance Goals so leadership can measure progress in operational terms instead of reacting only after an incident.
- Standardized provisioning: Build one onboarding workflow for users, devices, email, file access, MFA, and logging so growth does not create exceptions.
- Role-based access: Assign permissions by job function and project need, then remove inherited access when roles change.
- Endpoint control: Require EDR, patch compliance, encryption, and remote management on every company device before it touches production data.
- Backup validation: Test restores for file shares, project folders, and cloud data so recovery is proven, not assumed.
Field Evidence: Growth Stress Across a Northern Nevada Construction Operation
We worked through a similar pattern with a regional contractor operating between Reno and Sparks where office staff, field supervisors, and shared yard systems had been added over several hiring cycles. Before remediation, user setup varied by department, old permissions remained in place, and device inventory was incomplete. A single access issue forced leadership to stop normal work long enough to verify who could see estimating files, payroll-related folders, and vendor records.
After standardizing onboarding, documenting role-based access, and bringing endpoints under a single management baseline, the firm moved from reactive cleanup to controlled expansion. That included cleaner audit evidence, faster user setup, and fewer interruptions when new projects ramped up. For organizations that also need support for growing Reno businesses , this is where day-to-day oversight keeps the same problem from resurfacing six months later.
- Result: New user deployment time dropped from two business days to under four hours, access review exceptions fell by 68%, and no untracked endpoints remained on the production network.
Construction IT Scalability Risk Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Governance Policy And Audit Preparation and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.

Local Support in Reno, Sparks, Carson City, and Northern Nevada
Construction firms in the Reno-Sparks corridor often need support that accounts for fast hiring, multiple job sites, yard operations, and the practical distance between office staff and field teams. From our Ryland Street office, Granite Construction Regional Yard in Sparks is about 10 minutes away under normal conditions, which reflects the kind of local response and planning cadence many Northern Nevada businesses need when growth starts stressing systems and controls.
Standardize Before Growth Creates the Next Incident
A data breach in a growing construction firm is often the point where unmanaged expansion becomes impossible to ignore. When user setup, device control, access rights, and audit evidence are inconsistent, the business eventually runs into a ceiling where growth starts creating downtime, exposure, and operational drag.
The practical takeaway is straightforward: build the onboarding, governance, and operational controls before the next hiring push. For Reno-area construction companies, that usually means treating IT capacity as part of business planning, not as cleanup after another access problem or compliance scare.

