Reno Data Breach Fix
Seeing a data breach is often the visible symptom of compliance gaps, not the root problem itself. In construction firms across Reno, issues like missing controls, weak documentation, and loose access policies can quietly undermine business continuity and backup compliance until work stops or risk spikes. The fix usually starts with reviewing controls, access, and recovery steps before they are tested under pressure.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why the Compliance Gap Becomes the Real Breach Problem
For Reno construction firms, a data breach usually does not begin with a dramatic external event. More often, it starts with ordinary operational drift: shared credentials for estimators, project folders that stay open after role changes, backup jobs that report success without anyone validating recovery, and policy documents that no longer match current requirements. That is the compliance gap. The breach is simply the moment the gap becomes visible.
We see this most often when regulations and contract obligations move faster than internal documentation. CMMC expectations, healthcare-adjacent subcontractor requirements, insurance questionnaires, and customer security addenda all change the control environment. If access reviews, retention rules, and recovery testing are not updated with the same discipline, the business can fail both operationally and procedurally. Construction companies trying to stabilize this area often need structured business continuity and backup compliance in Reno so controls are tied to actual workflows instead of assumptions. In cases like Tammie’s, the immediate issue may be access failure, but the deeper problem is that nobody can prove who should have had access, what was backed up, or how quickly systems could be restored.
- Access governance: Project shares, accounting folders, and cloud apps often retain legacy permissions after staffing changes, acquisitions, or subcontractor turnover.
- Documentation drift: Written policies may reference old backup schedules, outdated vendors, or controls that are no longer enforced in the field.
- Recovery blind spots: Backup success alerts do not confirm that estimating files, job-cost data, and email records can actually be restored within required timeframes.
- Compliance pressure: Contractual and regulatory requirements can outpace internal IT processes, especially when construction firms add remote trailers, temporary sites, or new cloud platforms.
Practical Remediation for Construction Operations
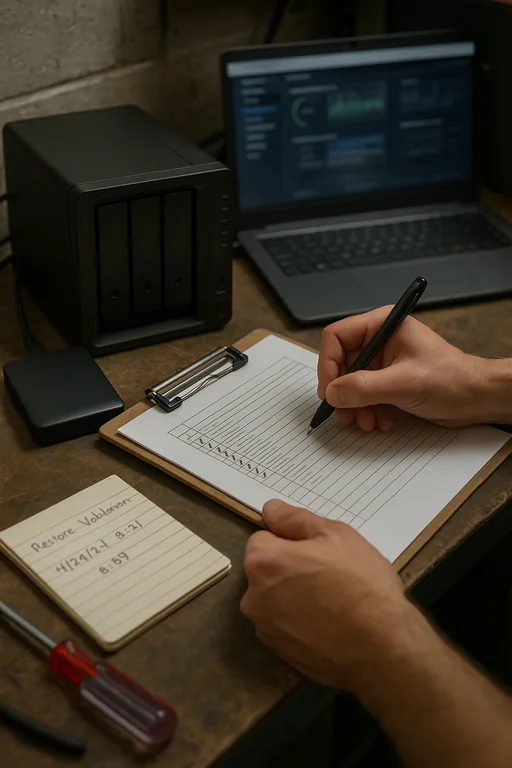
The fix is not a single security product. It is a control cleanup process that matches how the business actually operates. Start with role-based access reviews across file shares, Microsoft 365, line-of-business systems, and remote access tools. Then validate backup scope against the systems that matter most to operations: estimating, accounting, project management, email, and scanned job documentation. If retention, immutability, and restore testing are weak, the business is carrying more risk than the dashboard suggests.
We typically recommend formalizing restore testing and documented recovery priorities through backup and recovery programs for Reno operations , then aligning those controls with recognized guidance such as CISA ransomware and recovery guidance . For construction firms, that also means tightening MFA, removing stale accounts, documenting exception handling, and confirming that field and office teams can continue working if a primary system is unavailable. Infrastructure consistency matters as well, especially when cloud storage, on-prem servers, and mobile jobsite connectivity all intersect.
- Role-based access review: Remove inherited permissions, disable dormant accounts, and limit project data access to current business need.
- Backup validation: Test restores for accounting data, project files, and email rather than relying only on successful job logs.
- MFA hardening: Enforce phishing-resistant sign-in where possible and eliminate weak remote access paths.
- Control documentation: Update policies, retention schedules, and incident procedures so they match current systems and contract obligations.
- Platform oversight: Use network, server, and cloud management to keep permissions, monitoring, and system changes aligned across locations.
Field Evidence: Industrial Corridor Recovery Review
In one Northern Nevada engagement, a contractor operating between Reno and Sparks had no confirmed breach notification event, but repeated access issues and inconsistent backup records raised concern during an insurance and customer review. Before remediation, file permissions had grown organically over several years, backup retention varied by system, and nobody had run a full restore test on current project data. The business could not confidently answer how long accounting, scheduling, or document control would be down after an incident.
After a structured review, the company reduced shared-folder exposure, documented recovery tiers, validated restore times, and aligned office and field access with current roles. That mattered in a local environment where crews moved between yard, office, and jobsite, and where weather, carrier outages, and temporary connectivity can complicate recovery if controls are loose.
- Result: Restore validation time dropped from an untested state to a documented 3.5-hour recovery window for core project and accounting data, while stale privileged access was reduced by more than 60%.
Construction Compliance and Recovery Control Reference
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Business Continuity And Backup Compliance and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, and Northern Nevada and Northern Nevada.

Local Support in Reno and Sparks
Construction firms working between central Reno and the Sparks industrial corridor often need support that accounts for both office systems and operational movement between locations. From our Ryland Street office, the Lillard Drive area is typically about 13 minutes away under normal conditions, which makes it practical to support access failures, backup verification, and recovery planning tied to active business operations.
Close the Gap Before the Breach Defines the Process
For construction firms in Reno, the practical lesson is straightforward: a breach event often exposes control failures that have been accumulating quietly across access, documentation, backup validation, and recovery planning. If the business cannot show who has access, what is protected, and how quickly critical systems can be restored, the compliance gap is already affecting continuity.
The right response is disciplined remediation, not guesswork. Review permissions, test restores, align documentation to current obligations, and make sure office and field operations can continue through a disruption. That approach reduces downtime, supports audits and insurance reviews, and gives management a clearer operational picture before the next incident forces the issue.

