Reno Data Breach
What looks like a one-off issue is often tied to compliance gaps. In construction firm environments, missing controls, weak documentation, and loose access policies can turn into audit findings, fines, and operational disruption long before anyone notices the warning signs. Closing those gaps early makes regulatory compliance support far more resilient.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why Compliance Gaps Turn Into Breach Events

A data breach at a construction firm in Washoe County is rarely just a security failure. More often, it is a compliance management failure that has been building quietly for months. We typically find a mix of shared credentials, inconsistent onboarding and offboarding, undocumented file retention, and cloud access that expanded faster than internal policy controls. When regulations such as CMMC, HIPAA, or contract-driven security requirements change faster than the business can document them, the gap shows up first in operations and only later in the audit trail.
That is why firms dealing with contract data, employee records, project financials, or subcontractor documentation often need structured regulatory compliance support in Northern Nevada rather than a one-time technical cleanup. In practice, the breach is the visible symptom. The root cause is usually that required controls were never mapped to actual business processes. In a construction environment, that can affect estimating, field reporting, payroll coordination, and billing cycles all at once. When Larry lost access to trusted records during the incident, the real problem was not just the compromised account. It was the absence of documented control ownership.
- Access governance: User permissions often remain broader than necessary, especially when project managers, accounting staff, and outside partners all touch the same systems.
- Documentation drift: Policies may exist on paper, but they do not match current Microsoft 365 settings, file shares, retention rules, or vendor access.
- Audit readiness: Many firms cannot quickly prove who accessed what, when access was approved, or whether required controls were tested.
- Operational exposure: A breach can delay pay applications, subcontractor communication, and owner reporting long before any regulator asks questions.
Practical Remediation for Construction Compliance Failures
The fix is not just to reset passwords and move on. The right response is to close the control gap that allowed the breach to happen. That starts with a scoped review of identity controls, data handling, retention practices, vendor access, and evidence collection. For firms with multiple project teams, remote field access, and cloud-based document workflows, we usually recommend a formal baseline review supported by risk assessments and security readiness planning so the business can identify where policy, technology, and actual user behavior no longer align.
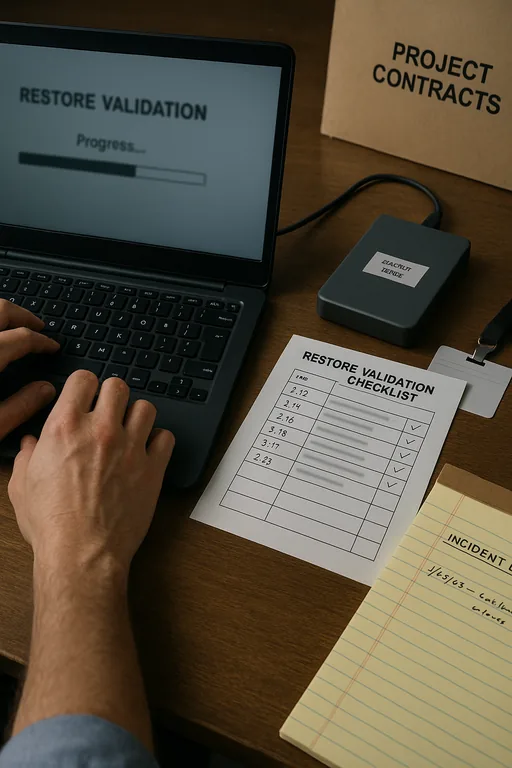
From there, remediation should be tied to recognized guidance. The CISA Secure Our World guidance is useful for reinforcing MFA, password hygiene, and phishing resistance, but firms with contract or regulated data also need stronger internal evidence. That means access reviews on a schedule, documented approval paths, tested backups, retention rules that match legal and contractual obligations, and incident response steps that can be followed under pressure. Where policy maturity is weak, businesses often benefit from compliance-focused IT management that turns scattered procedures into something auditable and repeatable.
- MFA hardening: Require phishing-resistant multi-factor authentication for email, file platforms, and remote admin access.
- Role-based access: Limit project, HR, and accounting data to approved groups with documented ownership.
- Retention controls: Align document storage and deletion practices with contract terms, legal requirements, and internal policy.
- Backup validation: Test recovery of critical files and cloud data, not just backup job completion alerts.
- Audit evidence: Preserve logs, approval records, and policy acknowledgments so the firm can demonstrate control enforcement.
Field Evidence: Multi-Department Access Cleanup After a Breach Review
We worked through a similar pattern with a Northern Nevada business operating between Reno and Sparks where project administration, finance, and outside vendors all relied on the same cloud file structure. Before remediation, access had grown informally over time, retention settings were inconsistent, and no one could quickly confirm whether former users still had visibility into sensitive folders. The immediate concern was breach containment, but the larger issue was that the business could not show a clean control narrative if an insurer, regulator, or contract partner asked for proof.
After a structured review, the business reduced shared access groups, documented approval ownership, enforced MFA across critical systems, and tied backup validation to actual recovery testing. The result was not just better security. It was cleaner operations during month-end billing and fewer delays when teams needed to verify records from active and closed jobs, even during weather-related schedule shifts common around Washoe County job sites and office corridors.
- Result: Privileged access was reduced by 43%, recovery verification time dropped from several hours to under 40 minutes, and the firm completed its next compliance review cycle with documented controls instead of manual reconstruction.
Compliance Control Reference for Construction Firms
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Regulatory Compliance Support and has spent his career building practical recovery, security, and operational continuity processes for businesses across Washoe County and Northern Nevada.
Local Support in Washoe County
Reno Computer Services supports businesses across Reno, Sparks, and the broader Washoe County area, including organizations operating near Neil Road where office administration, healthcare-adjacent tenants, and construction-related back-office functions often depend on stable access to shared records and documented controls. From our Ryland Street office, the route to this service area is typically about 14 minutes, which matters when a compliance issue is also interrupting billing, file access, or incident response coordination.
Closing the Gap Before the Next Incident
For construction firms in Washoe County, a breach is often the point where weak documentation, broad access, and outdated control practices finally become visible. The operational damage usually arrives first through delayed billing, interrupted coordination, and time lost reconstructing who had access to what. The compliance issue is not separate from the business issue. It is the reason the disruption lasted as long as it did.
The practical takeaway is straightforward: review controls before they are tested by an incident, not after. When policies, permissions, retention rules, and recovery steps are aligned, firms are in a much stronger position to contain a breach, satisfy contract requirements, and keep day-to-day operations moving.

