Reno Data Breach
This kind of issue rarely appears all at once. For construction firms in Northern Nevada, it usually builds through unclear ownership, overlapping tools, and fragmented support and then surfaces as a data breach, slower recovery, or higher exposure. A more reliable setup starts with clarifying ownership and enforcing cleaner escalation paths.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
How Vendor Chaos Turns Into a Breach
The main failure is not usually one bad device or one missed alert. It is the absence of clear ownership. In construction firms across Reno, Sparks, Carson City, and the Tahoe corridor, we often see internet, phones, line-of-business apps, printers, cloud storage, and field connectivity all managed by different vendors with different support boundaries. When no one owns the full environment, routine issues stay unresolved longer and security gaps remain open.
That is where the vendor chaos problem becomes a breach problem. A construction company may have shared admin accounts, stale vendor access, undocumented firewall changes, and no single escalation path when something looks wrong. In Shannon’s kind of situation, the delay is what causes damage. The first hour gets spent figuring out who controls what instead of isolating the affected account, reviewing logs, and protecting active jobs. Businesses dealing with that pattern usually need structured IT support and help desk in Northern Nevada so incidents move through one accountable process instead of four disconnected ones.
- Fragmented ownership: Internet, voice, cloud apps, and endpoint support are split across multiple providers, leaving no one responsible for access review, incident coordination, or final resolution.
- Overlapping tools: Different vendors deploy separate remote access tools, antivirus products, or backup agents, which creates blind spots and inconsistent alerting.
- Weak escalation paths: Office managers end up acting as dispatchers between carriers, software vendors, and consultants during an outage or suspected breach.
- Construction workflow exposure: Estimating files, bid documents, subcontractor records, and accounting data often move between office and field systems without consistent access controls.
What Practical Remediation Looks Like
The fix starts with consolidating accountability before adding more tools. We typically map every vendor, every admin credential, every remote access method, and every system dependency. From there, we assign a primary owner for incident response, define who can authorize changes, and remove legacy access that no longer has a business reason to exist. That is especially important for construction firms where project schedules, payroll timing, and subcontractor coordination leave little room for confusion.
From a technical standpoint, the environment should be standardized with documented access control, centralized logging, MFA enforcement, and tested recovery procedures. Firms that want fewer handoff failures generally benefit from network, server, and cloud management that ties file systems, identity controls, and backup validation into one operating model. For breach response planning and access control baselines, CISA guidance is a useful operational reference.
- Access cleanup: Remove unused vendor accounts, rotate privileged credentials, and require MFA for all administrative and remote access paths.
- Centralized alerting: Send firewall, endpoint, Microsoft 365, and backup alerts into one monitored workflow so suspicious activity is not buried across separate portals.
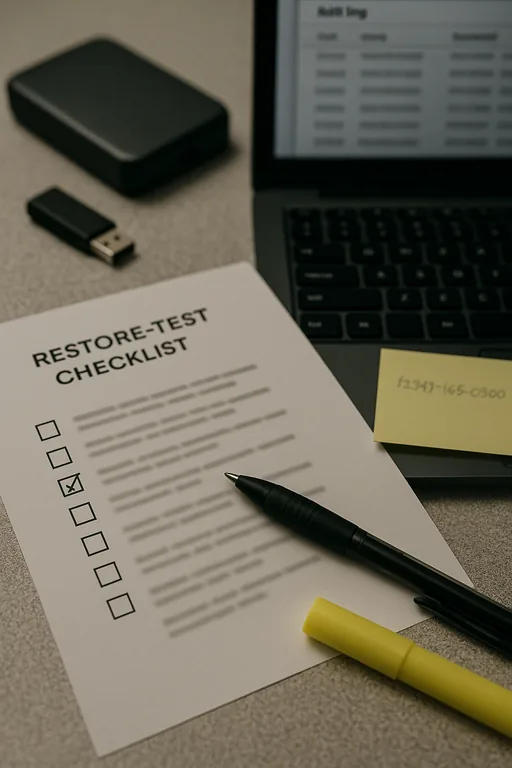
- Backup validation: Test file and server restores on a schedule instead of assuming backup jobs equal recoverability.
- Escalation control: Define one incident owner, one after-hours path, and one documented contact matrix for carriers, software vendors, and internal decision-makers.
Field Evidence: Multi-Vendor Construction Operations Stabilized
We have seen this pattern in Northern Nevada construction and trade environments where the main office is in Reno but crews, trailers, and supervisors work across Washoe County and into Carson-area job sites. Before cleanup, support tickets bounced between a telecom provider, a software reseller, and an outside network contractor. No one had a complete asset list, firewall rule history, or current admin roster. Small issues took hours to classify, and security reviews were mostly reactive.
After consolidating documentation, standardizing admin access, and tightening the core network design with network infrastructure management for multi-site operations , the response process became much faster. Instead of debating ownership during an incident, the company had a defined path for containment, vendor coordination, and recovery. That matters in a region where weather, travel time, and dispersed job locations can slow hands-on troubleshooting if the underlying process is weak.
- Result: Incident triage time dropped from roughly 3 hours to under 40 minutes, stale privileged accounts were eliminated, and backup restore testing confirmed recovery for critical estimating and accounting data.
Reference Table: Where Construction Firms Commonly Lose Control
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in It Support And Help Desk and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada
Construction firms in this region often operate across office, warehouse, and jobsite locations, which makes vendor coordination harder when something breaks. From our Reno office, the drive to the Aircenter area is typically about 15 minutes under normal conditions, which is close enough for practical local support but still far enough that remote triage, documentation, and clear ownership need to be in place before an incident starts.
Why This Issue Keeps Repeating
Construction firms do not usually end up with breach exposure because one system failed in isolation. The pattern is usually operational: too many vendors, unclear support boundaries, undocumented access, and no single owner for response. When that structure is weak, even a manageable security event becomes a longer outage, a slower investigation, and a more expensive recovery.
The practical takeaway is straightforward. Clarify ownership, reduce overlapping tools, document escalation paths, and verify that backups and access controls actually work. In Northern Nevada, where teams often move between office and field environments, that discipline matters more than adding another disconnected product.

