Reno Construction Risk
Problems like this tend to stay hidden until something important breaks. For construction firms in South Meadows, that often means a data breach, avoidable delays, or a bigger recovery burden than expected. The best response is hardening identity, watching for abnormal behavior, and closing blind spots across users and devices.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.

Why the Invisible Threat Is So Common in South Meadows Construction Operations
The main risk is not always a dramatic network intrusion. In many construction environments, the real breach starts with a reused password, a successful phishing prompt, or a compromised cloud login that blends into normal activity. That is the core of the invisible threat: modern attackers often do not break through the perimeter at all. They log in with stolen credentials, move through email, file shares, and cloud apps, and stay unnoticed long enough to affect billing, project schedules, or vendor communication.
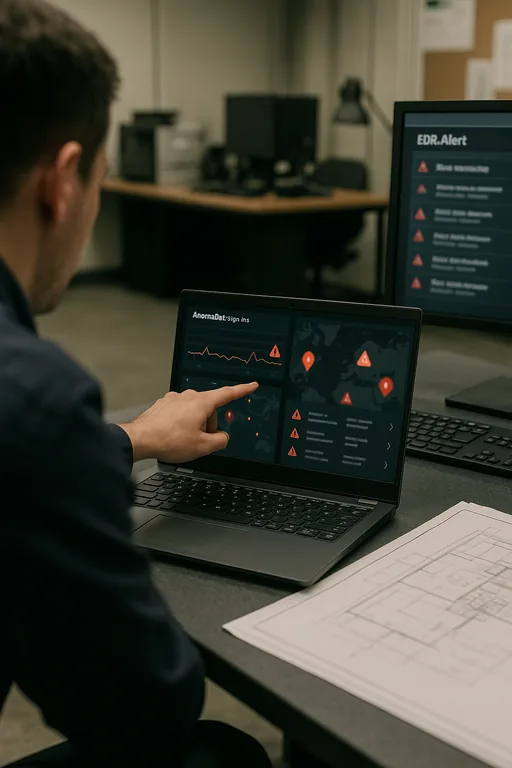
We see this regularly with firms operating between South Meadows, Reno, Sparks, and job sites spread across Northern Nevada. Estimators, project managers, accounting staff, and field supervisors all need fast remote access, which means identity becomes the control point. If sign-in monitoring is weak, conditional access is loose, or endpoint visibility is incomplete, a company can have a real breach without any obvious server outage. That is why businesses dealing with hidden account misuse often need security monitoring and response in Northern Nevada that focuses on user behavior, endpoint telemetry, and cloud account anomalies rather than just firewall alerts. In incidents like the one above, the problem is rarely one bad click alone; it is the combination of weak identity controls, limited alert tuning, and too many trusted sessions left unreviewed.
- Credential misuse: Stolen Microsoft 365 or VPN credentials can look like ordinary employee activity unless sign-in patterns, device trust, and impossible-travel events are actively reviewed.
- Construction workflow exposure: Shared bid files, vendor payment emails, and mobile access from trailers or job sites create more opportunities for account compromise to affect real operations.
- Hidden dwell time: A breach can remain undetected for days when the attacker only reads email, forwards messages, or accesses cloud storage without triggering traditional perimeter alarms.
- Business consequence: Delayed approvals, altered payment instructions, and interrupted scheduling can create downstream cost long before a formal incident response begins.
How to Reduce Breach Exposure Before It Turns Into Downtime
The fix is usually operational, not theoretical. Start by tightening identity controls around Microsoft 365, VPN access, and any cloud platform used for project documents or accounting. Enforce phishing-resistant MFA where practical, disable legacy authentication, review mailbox forwarding rules, and require device compliance before sensitive systems can be reached. Endpoint detection should be active on laptops used in the office, at home, and in the field so suspicious sign-ins can be correlated with device behavior instead of reviewed in isolation.
From there, governance matters. Construction firms benefit from written access standards, vendor payment verification procedures, and incident escalation steps that are actually used by office managers and project leads. That is where compliance-focused IT management becomes practical rather than administrative. We also recommend aligning controls with guidance from CISA , especially around strong authentication, password hygiene, and account protection. If the business handles regulated project data, insurance requirements, or contractual security obligations, a structured review through compliance advisory programs helps close the gap between technical controls and documented accountability.
- Identity hardening: Require MFA, block legacy protocols, restrict risky sign-ins by geography and device state, and review privileged accounts monthly.
- Behavior monitoring: Alert on impossible travel, unusual mailbox rules, mass file access, and sign-ins from unmanaged devices.
- Endpoint control: Deploy EDR across office and field laptops so suspicious login activity can be tied to process execution, malware, or browser token theft.
- Payment verification: Add out-of-band confirmation for vendor banking changes and invoice redirection requests.
- Backup validation: Confirm that file repositories, cloud data, and critical line-of-business records can actually be restored, not just backed up.
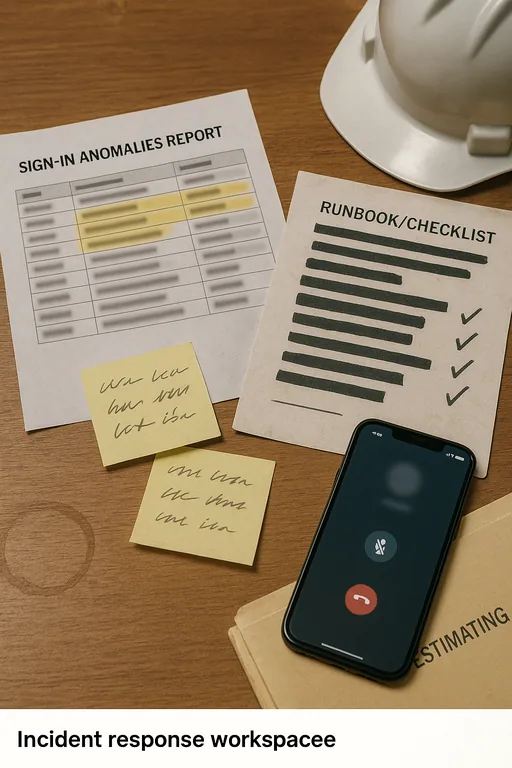
Field Evidence: Credential Abuse Hidden Inside Normal Project Traffic
In one Northern Nevada construction scenario, the initial complaint was not “we have a breach.” It was that accounting and project coordination were seeing inconsistent email threads, missing attachments, and confusion around payment approvals. The company had active firewalls and antivirus, but no one was reviewing cloud sign-in anomalies or mailbox rule changes. A compromised account had been accessed repeatedly outside normal work patterns while staff moved between a South Meadows office, supplier calls, and active job sites.
After containment, we reset sessions, enforced stronger MFA, removed unauthorized forwarding rules, validated endpoint health, and tightened access policies around finance and document systems. The before state was reactive and fragmented. The after state gave the business clearer visibility into who was signing in, from what device, and under what conditions. That shift matters in Reno-area operations where teams are often mobile and decisions move quickly. In this case, Terri’s callback was simple: once identity alerts were tuned correctly, the company stopped treating odd email behavior as a user issue and started treating it as a security signal.
- Result: Suspicious sign-in detection time dropped from multiple business days to under 20 minutes, and finance-related account changes required verified approval before release.
Reference Points for Reducing Invisible Breach Risk
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Security Monitoring And Response and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.
Local Support in Reno and South Meadows
We support businesses across Reno, including South Meadows, with practical response planning, identity hardening, and investigation of suspicious account activity. From our Ryland Street office, the route to the Sky Mountain area is typically short enough to support on-site coordination when a construction firm needs help validating access issues, containing a suspected breach, or restoring normal operations.
What Construction Firms Should Take Away
A hidden breach risk usually means identity controls are carrying more weight than the business realizes. For construction firms in South Meadows, the practical issue is not just whether a firewall is installed. It is whether cloud accounts, laptops, finance workflows, and remote access are being monitored closely enough to catch misuse before it affects schedules, payments, or project records.
The right response is disciplined and specific: tighten authentication, review abnormal behavior, validate endpoint visibility, and document who approves sensitive changes. When those controls are in place, a suspicious login becomes a contained event instead of a larger operational disruption.

