Reno Construction Cyber Test
Seeing a data breach is often the visible symptom of untested backups, not the root problem itself. In construction firms across Reno, issues like failed restore tests, missing dependencies, and an unclear recovery order can quietly undermine managed cybersecurity services until work stops or risk spikes. The fix usually starts with validating backups regularly and proving recovery before a real outage.
This case study reflects real breakdown patterns documented across 300+ regional IT incidents. Names and identifying details have been modified for confidentiality, while technical and financial data remain accurate to the original events.
Why a Data Breach Often Exposes a Resilience Failure First
For construction firms in Reno, a breach rarely stays limited to a security event. It quickly becomes an operations problem when project files, accounting data, scheduling systems, and vendor communications all depend on the same servers, cloud sync tools, and identity controls. What we usually find is that the visible incident draws attention to a deeper issue: the business has backups, but it has not proven that those backups can restore the full workflow in the order the business actually needs.
That distinction matters. A backup is only a copy. Business continuity is the ability to keep working while systems are degraded, isolated, or being rebuilt. In practice, that means testing whether file shares restore with permissions intact, whether estimating software reconnects to its database, whether Microsoft 365 access can be recovered cleanly, and whether remote trailers or jobsite laptops can still reach current documents. Firms relying on cybersecurity services in Washoe County are usually better positioned when monitoring, identity protection, and recovery validation are managed together instead of treated as separate projects. In Marina’s case, the real failure was not just exposure to a breach event. It was the lack of a verified recovery sequence for the systems the office used every hour.
- Untested restore order: Backups may exist, but if accounting, project management, shared storage, and user authentication are not restored in the right sequence, staff still cannot work.
- Missing dependencies: Construction applications often rely on mapped drives, SQL databases, cloud identity, and local permissions that are not validated during routine backup jobs.
- False confidence from successful backup logs: A green backup status does not confirm that data is usable, complete, or recoverable under real outage conditions.
- Operational concentration risk: One compromised server or account can affect bids, RFIs, payroll support, and document control across office and field teams.
What a Resilience Test Audit Should Fix
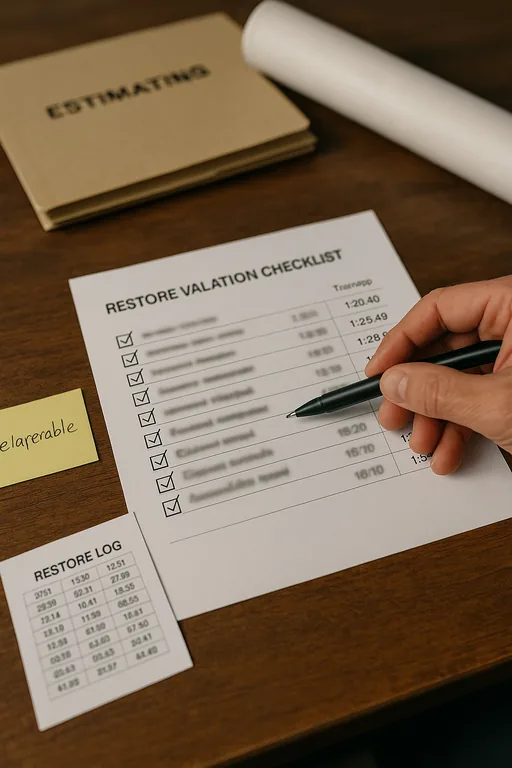
The practical fix is to move from backup ownership to recovery proof. We start by identifying the systems that actually keep the construction office moving: file storage, line-of-business applications, Microsoft 365, identity services, network shares, and any cloud-connected estimating or accounting platforms. Then we test restores against business priorities, not just technical convenience. That means confirming what must come back first, how long it takes, and what staff can do while recovery is underway.
For firms with contract obligations, payroll sensitivity, or regulated project data, this work should align with documented governance and risk review. That is where compliance-focused IT management becomes useful, because recovery testing, retention, access control, and incident response all need to support the same operating standard. A good benchmark for this approach is the guidance from CISA’s ransomware resilience and recovery recommendations , which emphasize tested backups, segmented recovery planning, and verified restoration.
- Restore validation: Run scheduled test restores for critical systems and confirm files open, permissions apply correctly, and applications reconnect without manual guesswork.
- Recovery sequencing: Document the order for identity, storage, databases, line-of-business apps, and endpoint access so staff can resume work faster.
- Backup isolation: Keep protected copies separate from production credentials and standard user access to reduce the chance of backup corruption during an attack.
- MFA and privileged access hardening: Limit administrative exposure and require stronger controls on backup consoles, cloud tenants, and remote management tools.
- Continuity planning: Define what the office, accounting team, and field supervisors can still do during partial outages, including alternate communications and temporary file access.
Field Evidence: The Resilience Test in a Reno Construction Workflow
We have seen this pattern in firms operating between central Reno, South Meadows, and job sites spread across Sparks and Carson City. Before testing, the environment often looks stable on paper: backup jobs complete, antivirus is active, and cloud email is available. But when a restore is attempted, the team discovers that the accounting database restores to a different path, shared folder permissions are incomplete, or a project folder structure synced from the cloud is several versions behind. That gap is where downtime expands.
After a structured resilience test, the before-and-after difference is usually straightforward. The business knows which systems are tier one, who approves recovery decisions, how long a clean restore actually takes, and what fallback process keeps project coordination moving during an outage. In one Northern Nevada scenario, a firm with crews working around weather delays and concrete scheduling windows reduced recovery uncertainty by validating both server restores and cloud access paths, then adding backup and disaster recovery controls for multi-location operations that matched how the office and field teams really worked.
- Result: Recovery testing cut estimated downtime from more than one business day to under four hours for core file access, accounting, and project document retrieval.
Construction Resilience Audit Reference Points
Scott Morris is an experienced IT and cybersecurity professional with 16 years of hands-on experience in managed technology services. He specializes in Managed Cybersecurity Services and has spent his career building practical recovery, security, and operational continuity processes for businesses across Reno, Sparks, Carson City, Lake Tahoe, and Northern Nevada and Northern Nevada.

Local Support in Reno and Northern Nevada
Construction firms in South Reno, Double Diamond, Sparks, and nearby project corridors often need support that accounts for both office systems and field coordination. From our Ryland Street office, the route to the Double Diamond area is typically about 18 minutes, which matters when an outage affects estimating, document access, or recovery verification during an active workday.
The Real Audit Question Is Whether Recovery Actually Works
A construction firm dealing with a breach in Reno does not just need a security response. It needs proof that critical systems can be restored in a usable order, with permissions, dependencies, and business priorities intact. That is the difference between having backup software and having resilience.
The practical takeaway is simple: test restores, document recovery order, validate access, and align security controls with continuity planning. When those pieces are in place, a breach is still disruptive, but it is far less likely to stop billing, scheduling, project coordination, or field communication for longer than necessary.

