Regulated Businesses
Regulated businesses operate under licensing, privacy, payment, or industry control requirements that directly affect IT decisions. Understanding the rules, the evidence behind compliance, and where local authority support fits can reduce disruption, audit stress, and avoidable exposure.
At a licensed behavioral health office, Alfred P. was still able to log in through an old remote access account three weeks after termination; patient intake stopped during the investigation, reportable exposure work began immediately, and the first week of containment and legal review cost $62,000.
The following scenario reflects a redacted real-world incident pattern encountered in business IT environments. Identifying details have been changed for privacy, while the operational failure and financial impact remain representative.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage secure infrastructure, reduce operational risk, recover from outages, maintain continuity, and stabilize compliance-aware technology environments. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to regulated businesses because access control, recovery readiness, documentation discipline, incident response, and secure system management are what separate a defensible environment from one that fails under audit or during a breach. His work supporting Reno and Sparks business technology environments is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience.
Regulatory obligations vary by industry, contract, data type, and geography, so the right control set depends on what your business actually handles and who oversees it. This is general technical information; specific network environments and compliance obligations change strategy.
A common mistake is treating compliance as a policy exercise instead of an operating model. Many smaller regulated businesses have written procedures, but the real exposure sits in daily habits such as shared accounts, informal vendor access, inconsistent offboarding, and missing audit evidence. What usually separates a stable environment from a fragile one is whether ongoing IT operations oversight turns those policies into repeatable, documented controls.
- Data scope: The business needs a clear inventory of regulated data, where it lives, who can access it, and which vendors can touch it.
- Control ownership: Each safeguard needs an owner, a review cadence, and an exception process rather than relying on memory.
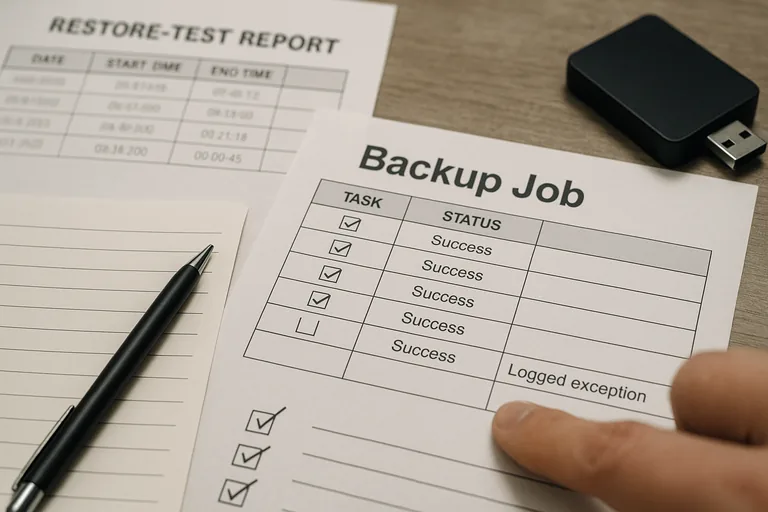
- Evidence: If patching, access reviews, or backups are claimed, there should be records showing dates, systems, results, and follow-up actions.
- Recovery readiness: Regulated operations need more than backup software; they need tested restoration steps that support real business continuity.
What counts as a regulated business in practice?
In practice, it is not limited to banks or hospitals. Medical offices handling protected health information are guided by the HHS HIPAA Security Rule, merchants processing cards are affected by the PCI DSS Official Standards, and Nevada organizations storing personal information should understand Nevada Revised Statutes NRS 603A. Those frameworks matter because they translate legal or contractual obligations into operational expectations around confidentiality, integrity, availability, access control, incident handling, and proof that safeguards are actually being maintained.
Why does regulation change IT decisions?
Regulation changes IT decisions because the business is no longer judged only by whether systems run; it is judged by whether access is controlled, sensitive data is limited to approved use, incidents can be investigated, and records exist to prove diligence. A common failure point is assuming a tool purchase satisfies the obligation. In mature environments, the issue is rarely the tool alone; it is the process around it, including who approves access, how changes are tracked, how long logs are retained, and how quickly operations can continue after a system problem.
Which failures create the most regulatory and operational exposure?
- Incomplete offboarding: Former staff, contractors, or vendors keep active accounts, creating hidden access long after the business relationship ends.
- Shared identities: Generic logins make activity hard to trace, weaken accountability, and complicate breach investigation.
- Uncontrolled data flow: Regulated information is copied into personal email, spreadsheets, local desktops, or unsanctioned cloud tools.
- Patch exceptions that never close: Critical systems are left behind because nobody owns the maintenance window or validates completion.
- Documentation gaps: During an incident, leadership cannot quickly answer what data was affected, which systems were involved, or who had access.
How should regulated IT operations work day to day?
Day-to-day control in a regulated environment usually means identity lifecycle management, asset tracking, patch deployment, endpoint protection, log retention, vendor access control, documented change management, and recovery planning operating as one system rather than separate tools. During a routine security review, repeated login failures from a retired front-desk PC led investigators to a legacy scheduling connector still running under a shared account with no owner; the alert was only the symptom, while the real issue was an undocumented system dependency and weak offboarding. Mature environments map each regulated application to an owner, remove access through tickets, review exceptions on a set cadence, and keep logs long enough to reconstruct who did what and when.

How can a business verify controls are really functioning?
A mature environment should produce patch compliance reports, access review logs, restore test records, asset inventory documentation, security alert escalation notes, and change records that show what was approved and when. Without those artifacts, leadership is being asked to rely on verbal assurance. In practice, this often breaks down when backups are present but restores have not been tested, multifactor authentication exists for executives but not all privileged accounts, or alerts are generated without a documented workflow showing who reviewed them and how exceptions were handled.
What warning signs suggest weak or superficial compliance?
- Audit readiness depends on one person: If one employee must explain everything from memory, the environment is fragile.
- Policies exist without operating evidence: Written standards are available, but no logs, reports, or review records support them.
- Vendor access is loosely controlled: Third parties connect remotely without formal approval, narrow permissions, or session traceability.
- Systems are patched by assumption: Leadership hears updates are automatic, but no compliance report confirms actual coverage.
- Incidents are handled informally: Response happens through scattered email and chat instead of tickets, timelines, and containment records.
What should happen next if your environment is unclear?
The next step is usually a scoped review of obligations, data types, system owners, vendor touchpoints, and the evidence your business can produce today. A competent provider should be able to explain where regulated data enters the business, how access is approved and removed, how exceptions are documented, what recovery sequence would be followed during downtime, and which controls still depend on habit instead of process. That kind of review often reveals whether the environment is genuinely controlled or simply appears controlled until someone asks for proof.

