Proactive Device & Endpoint Management
Proactive device and endpoint management keeps business laptops, desktops, and mobile systems patched, monitored, encrypted, and accountable so security issues are caught earlier, staff lose less time to device trouble, and avoidable downtime is reduced before it spreads.
On a Tuesday morning, Abby K. at a 42-user logistics office learned a newly issued laptop had never been enrolled in endpoint management, missed six months of patches, and spread credential-stealing malware through a shared browser profile; shipping stopped for a day, emergency cleanup followed, and the disruption cost $50,000.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage devices, reduce cyber exposure, maintain stable infrastructure, and recover cleanly when systems fail. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background matters in proactive device and endpoint management because weak enrollment, patching gaps, poor policy enforcement, and missing recovery documentation are common causes of downtime in real business environments; experienced IT teams reduce risk through disciplined monitoring, secure configuration, response workflows, continuity planning, and operational resilience for Reno and Sparks business technology environments.
This article explains common operational patterns and evaluation points, not a one-size-fits-all prescription. This is general technical information; specific network environments and compliance obligations change strategy. Legacy software, remote work, cyber insurance conditions, and industry rules may require different controls or review cadence.
In real business environments, endpoints are where staff work, where credentials are stored, and where many incidents first become visible. When a machine is slow, unpatched, misconfigured, or missing security controls, the business effect is not abstract: users lose hours, SaaS sessions are exposed, line-of-business software behaves unpredictably, and support costs climb. This is one reason mature managed IT services treat endpoint oversight as an operational function with ownership, review cadence, and escalation paths rather than a background utility.
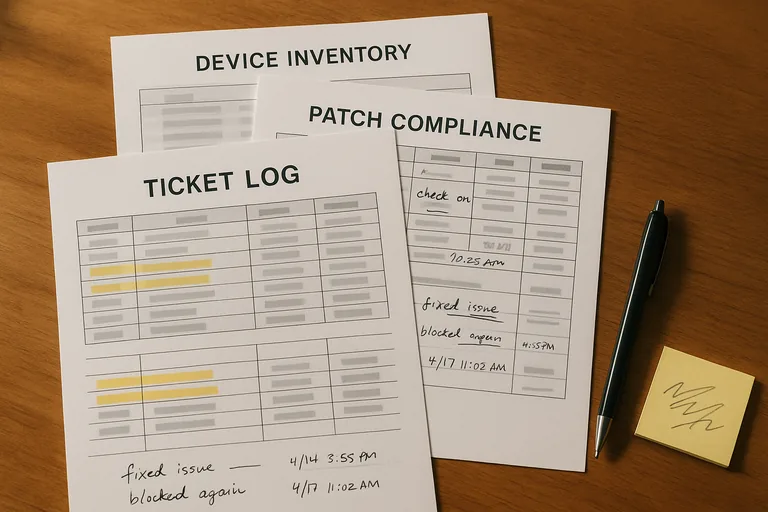
What usually separates a stable environment from a fragile one is evidence. Competent teams can show which devices are enrolled, which are overdue for critical patches, which users have local administrator rights, which machines have stopped checking in, and which exceptions were formally approved. In practice, the issue is rarely the tool alone; it is the process around it, especially when new devices are deployed quickly, remote staff work offsite, or older software creates pressure to bypass security policy.
What is proactive device and endpoint management?
Proactive device and endpoint management means the business does not wait for a user complaint or security incident to learn that a device is unhealthy. The devices are enrolled into management, assigned to users, configured against a baseline, monitored for patch and security status, and reviewed when exceptions appear. That approach usually improves uptime because problems such as failed updates, low disk space, broken security agents, expiring certificates, and unsupported software are identified before they interrupt work.
Why does it matter beyond antivirus and occasional updates?
Antivirus by itself sees only part of the problem. It does not replace patch discipline, configuration control, disk encryption oversight, application lifecycle management, or evidence that a lost laptop can be locked, wiped, or investigated. For businesses with remote staff, executives carrying sensitive mail, or regulated data flows that intersect with HIPAA security requirements, unmanaged endpoints create both operational disruption and a documentation gap when leadership needs to prove what was protected, what was exposed, and who was responsible.
Which risks does it reduce before they become incidents?
The risks it can reduce are usually the preventable ones that cause expensive cleanup: stolen credentials reused from an unmanaged browser, malware footholds through delayed patches, data exposure from missing encryption, and lateral movement enabled by standing local admin rights. Guidance in NIST SP 800-63B exists because identity controls fail when authentication and account lifecycle management are inconsistent; on endpoints, that translates into enforcing sign-in policy, tightening privileged access, and removing stale device trust before one compromised machine becomes a wider account incident.
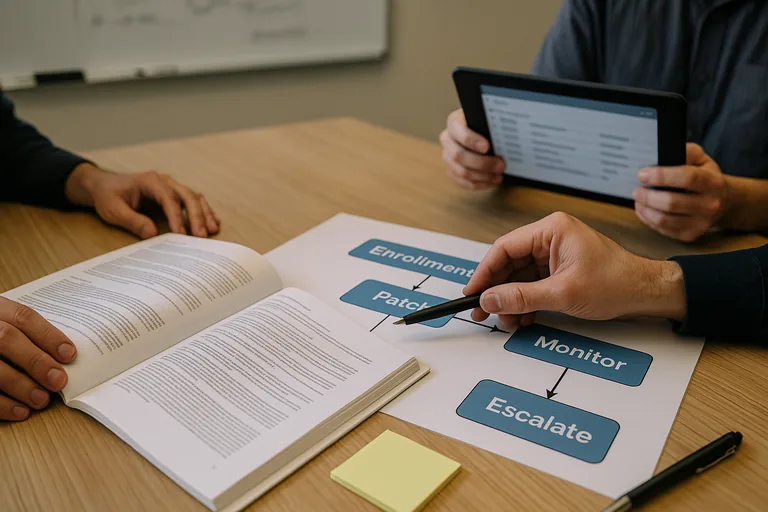
How does proactive endpoint management work in practice?
In practice, competent teams start with enrollment into a management platform, apply a standard build, push security tools, escrow encryption keys, define patch rings, restrict local admin, and watch health telemetry for exceptions. Alerts should not float in a dashboard without ownership; they need documented response steps tied to normal IT support and help desk processes so a failing agent, repeated reboot deferral, or offline executive laptop triggers action. During one routine review, a device showed current Windows updates but no recent endpoint sensor heartbeat; investigation found a manually prepared replacement laptop that never registered its security agent or encryption recovery key, which is exactly the kind of provisioning gap mature teams catch through verification rather than user complaints.
How can a business tell whether endpoint management is being done competently?
- Asset accuracy: There should be a current inventory showing device owner, location, operating system, lifecycle status, and whether the device is actually checking in.
- Patch evidence: Ask for patch compliance reports by severity and age, not a verbal assurance that updates are handled.
- Policy proof: A competent provider can show encryption status, endpoint protection coverage, local admin exceptions, and configuration baselines that are enforced rather than merely written down.
- Response records: Mature environments produce alert escalation logs, ticket history, and exception approvals so leadership can see who acted, when, and why an issue remained open.
When does weak implementation become dangerous?
Weak implementation becomes dangerous when endpoint management exists on paper but not in practice. A common failure point is replacement devices being handed out before enrollment is complete, temporary admin rights never being removed, update policies being paused for one legacy application and then forgotten, or alerts being sent to a mailbox nobody reviews. During incident response, it is common to discover that the security tool was installed, but a broken service, expired license, or stale policy left the device effectively unprotected for weeks; by then, the business is dealing with downtime, uncertain breach scope, and unreliable testimony about what controls were active.

