Network, Server & Cloud Management in Minden, Nevada
Network, server, and cloud management keeps Minden businesses running by controlling uptime, security, access, updates, and recovery across local infrastructure and hosted platforms, so day-to-day operations are less likely to stall because of neglected systems or unclear ownership.
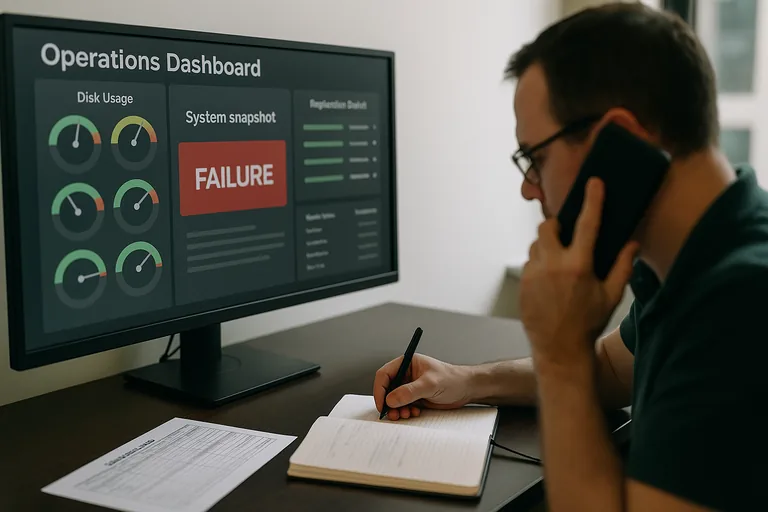
On a Tuesday payroll run in Minden, Aria W. lost access to her hosted ERP after a neglected virtual host datastore filled, snapshots stalled, and cloud file sync began writing stale records over current ones; emergency recovery, overtime, and delayed billing cost $72,500.
{HOOK_DISCLOSURE}
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage networks, servers, cloud platforms, access controls, recovery planning, and day-to-day infrastructure stability. Scott Morris has 16+ years of managed IT and cybersecurity experience. That operational background is directly relevant to Network, Server & Cloud Management in Minden, Nevada because weak ownership of patching, monitoring, identity, storage, and restoration is what turns routine technical issues into downtime, security exposure, and expensive recovery work. Scott Morris’s work is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience for business environments, including support approaches used for Reno and Sparks area organizations that need stable and well-maintained systems.
This article explains common operational patterns, controls, and evaluation points for business infrastructure management. This is general technical information; specific network environments and compliance obligations change strategy.
For a Minden business, network, server, and cloud management means one coordinated operating model for firewalls, switches, wireless, internet connectivity, virtualization, line-of-business servers, Microsoft 365 or other cloud platforms, user access, and recovery planning. The goal is not merely to keep equipment powered on. It is to make sure every critical system has ownership, monitoring, patching, backup coverage, and documented response steps when something starts to drift. Businesses comparing their current support approach with managed IT support in Minden should expect accountability across the full stack, not separate vendors blaming each other during an outage.
- Inventory: A current record of network gear, servers, virtual machines, cloud tenants, software, and admin accounts.
- Standardization: Consistent configurations for firewalls, backups, patching, DNS, remote access, and privileged accounts.
- Monitoring: Alerts for availability, disk health, failed logins, certificate expiration, replication problems, and abnormal resource use.
- Recovery readiness: Tested restore procedures, documented dependencies, and a known order for bringing systems back online.
A common failure point is the hybrid environment that grew without design: an aging file server in the office, cloud apps with separate admin portals, a firewall nobody has reviewed in years, and remote vendor access that survives staff turnover. That is where compliance and risk management stops being paperwork and becomes an uptime issue, because undocumented changes and weak control over identities usually mean longer outages, more security exposure, and harder recovery.
What does network, server, and cloud management actually include for a Minden business?
It includes the systems that move data, process work, store records, and control access: firewalls, switches, wireless, internet circuits, VPN or remote access, domain services, physical or virtual servers, backup systems, cloud identity, SaaS administration, and the policies that connect them. Cloud adoption does not remove network or server responsibility; it shifts some of it. What usually separates a stable environment from a fragile one is centralized ownership of identity, logging, patching, and configuration across all three layers. Guidance in NIST SP 800-207 Zero Trust Architecture matters here because business systems are no longer protected simply by being inside the office network; each request, device, and user session needs ongoing verification.
Why does this become a business risk instead of just an IT issue?
Because most operational failures show up first as stalled work, missed deadlines, and billing disruption, not as an abstract technical event. When DNS is unstable, line-of-business applications may appear down even though the server is running. When cloud permissions drift, the wrong people keep access and the right people lose it during a time-sensitive task. When storage fills or replication fails quietly, the business may discover the problem only after records are inconsistent across locations. For Nevada companies handling personal information, Nevada Revised Statutes NRS 603A also makes reasonable security measures a legal expectation, which means weak administration can create liability in addition to disruption.
How does competent management work in practice across network, server, and cloud systems?
What evidence shows the environment is being managed competently?
A common failure point is a stack of tools with no operating discipline behind them. Examples include endpoint protection installed but exclusions never reviewed, firewall rules accumulating without change control, admin accounts shared by multiple people, cloud backups purchased without confirming what data is actually covered, and server updates postponed until a reboot window never arrives. This tends to break down when a provider can describe products but cannot produce reports, runbooks, or recent test results. Another warning sign is when business leaders hear that everything is monitored, yet nobody can explain alert thresholds, after-hours ownership, or what the last resolved incident looked like. Those gaps usually stay hidden until an outage lasts longer than expected or an access problem turns into a security event.
- Asset inventory records: A dated list of firewalls, switches, servers, virtual machines, cloud tenants, software versions, and ownership.
- Patch compliance reports: Regular reporting that shows which systems are current, which are overdue, and why any exceptions were approved.
- Alert escalation logs: Records showing when a warning fired, who responded, how the issue was investigated, and when it was resolved.
- Restore test results: Proof that key systems and cloud data were restored to a usable state, not just that backup jobs reported success.
- Access review reports: Periodic confirmation that former staff, vendors, and shared administrative access were removed or restricted appropriately.
What warning signs suggest weak implementation or hidden fragility?
What should a business in Minden evaluate before changing providers or accepting the status quo?
Ask for evidence from the last ninety days: patch compliance reporting, restore test results, privileged account review, major incident notes, network documentation, and the escalation path for a failed server, internet outage, or cloud admin lockout. A competent provider should be able to explain which systems are critical, what recovery sequence is documented, what exceptions exist, and where the environment is still carrying risk. If that discussion is hard to get from the current provider or internal team, comparing the environment against the expectations of ongoing managed IT services in Minden can clarify whether the issue is tooling, staffing, or a lack of operational ownership. This is also the point where many businesses realize that undocumented access and weak review cadence belong in a broader risk management conversation, not just a support ticket queue.

