Network, Server & Cloud Management in Fallon, Nevada
Network, server, and cloud management keeps Fallon businesses operating by maintaining connectivity, application availability, secure access, and recoverable data. Done properly, it reduces avoidable outages, shortens recovery time, and gives leadership visible control over infrastructure risk.
At 8:17 a.m., Anne R. learned that a neglected virtualization host in a Fallon office had dropped two line-of-business servers, the cloud sync queue had stalled overnight, and payroll, dispatch, and invoicing were frozen long enough to create $71,200 in recovery costs, overtime, and lost work.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure, secure identities, maintain stable networks, recover servers, and keep cloud platforms operational under real business conditions. Scott Morris has 16+ years of managed IT and cybersecurity experience. That experience is directly relevant to Network, Server & Cloud Management in Fallon, Nevada because reliable environments depend on disciplined monitoring, documentation, patching, access control, recovery planning, and incident handling rather than assumptions or one-time setup. Scott Morris’s work is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience for business technology environments, including support relevant to Reno and Sparks organizations where downtime and security exposure carry real operational cost.
The discussion below focuses on operational patterns, common failure points, and evaluation criteria that business leaders can use when reviewing infrastructure management. This is general technical information; specific network environments and compliance obligations change strategy.
In practice, network, server, and cloud management is the day-to-day discipline of keeping firewalls, switches, wireless, internet circuits, virtual hosts, storage, Microsoft 365 or other cloud platforms, and business applications working as one operating environment. For companies comparing this work to broader managed IT services in Fallon, the difference is operational depth: the goal is not only user support, but also stable performance, controlled change, secure configuration, and recoverable infrastructure.
- Network layer: Internet connectivity, firewall policy, switching, wireless coverage, VPN access, and segmentation that determine how people and systems communicate.
- Server layer: Physical hosts, virtual machines, storage, directory services, application servers, and patching that keep core business systems available.
- Cloud layer: Identity platforms, email, file collaboration, backup targets, SaaS administration, and security settings that extend operations beyond the office.
A common failure point is treating these layers as separate purchases instead of one interdependent system. In mature environments, server maintenance is coordinated with backup retention, firewall rules are reviewed when cloud workflows change, and account permissions are tied to job role changes. That coordination supports uptime, but it also supports audit readiness and documented decision-making for organizations working through compliance and risk management expectations.
What does network, server, and cloud management actually cover in a Fallon business?
It covers ownership of the full infrastructure lifecycle: inventory, configuration, monitoring, patching, capacity, access control, backup protection, and recovery planning across on-premises and cloud systems. What usually separates a stable environment from a fragile one is clear ownership of change. If nobody can say which switch feeds the phone system, which server hosts the accounting database, which cloud tenant controls email security, or who approves firewall changes, the environment may function day to day while still carrying hidden outage risk.
Why does this matter beyond basic uptime?
Because infrastructure problems rarely stay technical for long. A failed switch uplink can stop barcode scanners, a storage latency issue can make accounting look like a software problem, and a cloud identity outage can lock out email, remote access, and file sharing at the same time. Fallon businesses often run lean operations, so one unavailable system may delay shipping, payroll, scheduling, customer communication, or field coordination faster than leadership expects.
Which operational risks does competent management reduce?
Competent management reduces several risks at once: unplanned downtime from aging hardware, security exposure from stale admin accounts, data loss from unprotected storage, and recovery delays caused by undocumented dependencies. In environments that have not been reviewed recently, it is common to find old VPN users still enabled, flat internal networks that allow broad lateral access, and cloud admin accounts protected inconsistently. Nevada businesses handling personal information also need reasonable security measures under Nevada Revised Statutes NRS 603A; in business terms, poor infrastructure management can become not only an outage problem but also a legal and reporting problem when logs, account controls, and response records are missing.
How does competent management work in practice day to day?
In mature environments, the day starts with dashboard review for failed services, unusual login activity, high disk usage, link errors, backup status, and cloud service alerts, followed by ticket triage, scheduled changes, and documented follow-up. During one routine infrastructure review, repeated packet loss on a core uplink looked like a cabling issue, but correlated logs showed a failing transceiver and an overloaded virtual host sharing the same closet power circuit; the signal mattered because the first symptom was network instability, while the deeper issue was multi-layer infrastructure stress. Guidance from the Cybersecurity and Infrastructure Security Agency (CISA) emphasizes protected backups because resilience depends on restoration integrity, and competent teams pair that with restoration sequencing so identity services, file shares, and line-of-business systems come back in a controlled order.

What evidence shows the environment is being managed competently?
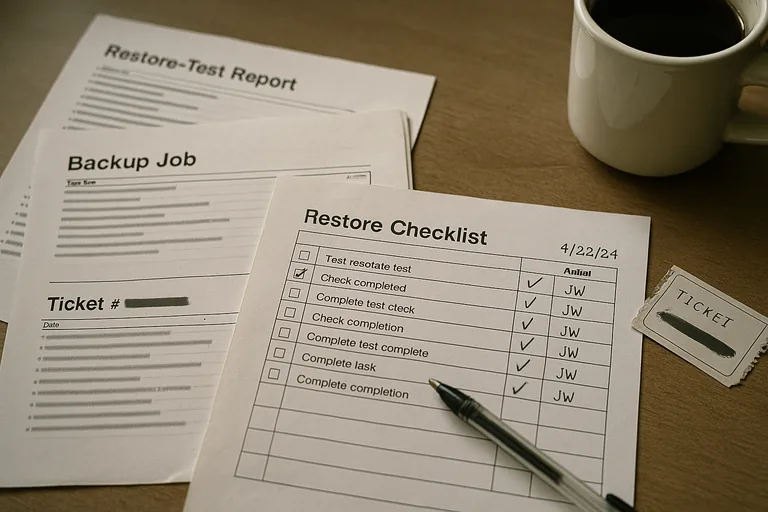
A competent provider should be able to show a current asset inventory, patch compliance reports, alert escalation logs, backup restore test records, firewall rule review notes, and documented ownership for privileged accounts. In practice, the issue is rarely the tool alone; it is the process around it. A business evaluating ongoing IT operations in Fallon should ask how exceptions are handled, how often restore tests are performed, who confirms failed alerts were acknowledged, and what report proves systems were actually updated rather than merely scheduled for updates.
When does weak implementation become dangerous?
This tends to break down when remote access is added without segmentation, old administrative rights accumulate over time, or cloud sign-ins are protected by multifactor authentication for some users but not all privileged roles. Guidance in NIST SP 800-207 Zero Trust Architecture exists because once a single device or identity is compromised, broad internal trust makes lateral movement much easier; in business terms, weak separation turns a local issue into a company-wide outage. A common failure point is believing the firewall alone provides safety while servers, printers, cameras, workstations, and cloud admins still operate in loosely controlled trust relationships.
What should a Fallon business review next?
The next step is not a tool purchase; it is a baseline review of inventory, internet dependencies, server roles, cloud administrator access, backup retention, recovery order, and documentation quality. If leadership cannot get a clear map of critical systems, recent restore evidence, and a written explanation of who responds to after-hours alerts, the environment is operating on assumption. For organizations aligning infrastructure decisions with documented risk and compliance priorities, that review should also identify where legal obligations, cyber insurance expectations, and operational dependencies overlap.

