Manufacturing
Manufacturing growth depends on more than equipment and labor; it depends on stable systems, secure data flows, and recoverable operations that support planning, production, shipping, and workforce coordination without creating avoidable downtime or contract risk.
At 6:12 a.m., Alexandra K. watched a fabrication line stall because the ERP server that released work orders and printed shipping labels failed after repeated storage alerts went unanswered; three outbound loads missed cutoff, overtime spiked, and the disruption cost $61,000.
The following situation represents a realistic incident pattern derived from real business IT environments. Identifying details have been changed to preserve confidentiality.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage, secure, maintain, and recover the systems they depend on for daily operations. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Manufacturing because production environments rely on stable infrastructure, controlled access, recovery readiness, business continuity planning, and disciplined change management to reduce downtime, security exposure, and expensive operational surprises. His work is grounded in practical risk reduction, secure infrastructure management, operational resilience, and recovery planning for business technology environments, including Reno and Sparks organizations that need dependable systems rather than improvised fixes.
This article explains manufacturing IT and cybersecurity from an operational business perspective. This is general technical information; specific network environments and compliance obligations change strategy.
- Operational systems: ERP, MRP, scheduling, purchasing, shipping, and quality platforms coordinate work before a part is ever touched.
- Plant-floor dependencies: Label printing, scanner connectivity, engineering workstations, shared folders, time synchronization, and network switching often determine whether operators can keep moving.
- Business risk: A failure that looks minor in IT can create scrap, missed pickups, delayed invoices, overtime, and customer confidence issues within the same shift.
A common failure point is assuming office IT and plant-floor technology can be managed as separate worlds with no overlap. In real business environments, a password change, DNS issue, switch fault, expired certificate, or undocumented vendor tool can interrupt production just as effectively as a machine problem. What usually separates a stable environment from a fragile one is not the amount of hardware on site, but whether dependencies are documented, monitored, secured, and tested before they fail.
What does manufacturing actually include from an IT and cybersecurity standpoint?
From an operations perspective, manufacturing includes both business IT and the systems that support production decisions. That can mean ERP or MRP platforms, MES software, CAD or CAM file storage, purchasing workflows, QA documentation, shipping labels, handheld scanners, vendor remote access, and sometimes engineering workstations used to maintain PLC or HMI programs. A common mistake is to think only the machine controllers matter. In practice, production often depends just as heavily on identity systems, file access, print services, network switching, and time synchronization, because if those fail, lines can keep running briefly but orders, traceability, and shipment accuracy start breaking down.
Why does manufacturing downtime spread faster than many office outages?
What risks can competent manufacturing IT reduce?
Competent manufacturing IT reduces the risk of unauthorized remote access, production stoppage caused by single points of failure, file integrity problems in engineering data, and lateral movement between office and plant-floor systems after an account compromise. One weak point experienced teams often find is shared credentials for vendors or maintenance staff, which makes accountability poor and containment harder during an investigation. Guidance in NIST SP 800-63B matters here because authentication controls are not just a security preference; they exist to make user identity verifiable throughout the account lifecycle. In business terms, named accounts, multifactor authentication, reviewed privileges, and segmented access reduce the chance that one compromised login turns into line disruption, data loss, or an expensive recovery project.
How should manufacturing systems be managed in practice?
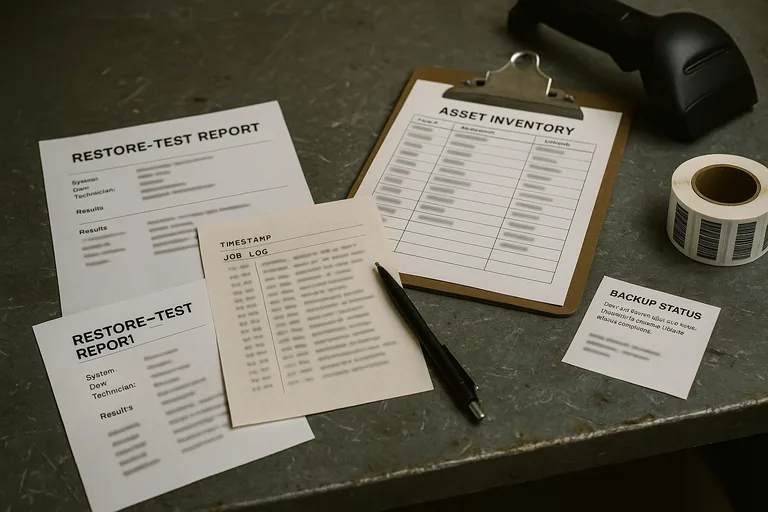
In mature environments, management starts with an accurate asset inventory that distinguishes office devices, engineering workstations, scanners, print servers, switches, wireless access points, and systems that directly affect production. Patch windows are scheduled around production realities, not around generic IT convenience, and exceptions are documented for equipment that cannot be updated normally. Monitoring should include storage health, switch status, wireless performance, environmental conditions in network closets, authentication activity, and backup job integrity for business systems that drive planning and fulfillment. During one routine review, repeated scanner dropouts triggered investigation into a packing area switch; the underlying issue was a failing cooling fan in a small wall cabinet, causing intermittent packet loss that only appeared during hotter afternoon shifts. This is where disciplined manufacturing IT management matters: the signal was minor, the root cause was not obvious, and the lasting fix required monitoring, documentation, and dependency awareness rather than a quick reboot.
How can a manufacturer tell whether the environment is actually being maintained properly?
A competent provider or internal team should be able to show evidence, not just reassurance. That evidence usually includes current asset inventory records, patch compliance reports, alert escalation logs, privileged access reviews, restore test results, documented exceptions for systems that cannot follow normal policy, and change records that explain what was modified and why. If backup status is always described as successful but there is no recent restore test, the environment may be less recoverable than it appears. If security alerts exist but nobody can show who reviewed them or how they were resolved, monitoring may be largely performative. Manufacturers serving regulated customers or adjacent sectors often find expectations begin to resemble healthcare technology environments, where documentation and verification matter because operational claims must be supported by records.
When does weak implementation become dangerous in a manufacturing environment?
Weak implementation becomes dangerous when controls exist on paper but ownership is unclear. Shared HMI logins, dormant vendor accounts, antivirus deployed with broad exclusions nobody remembers approving, undocumented network changes, and production PC images that drift over time are all common warning signs. In environments that have not been reviewed recently, it is also common to discover that alert emails still go to former employees, PLC or HMI program backups are incomplete, and the one person who understands line-side connectivity is unavailable during a shift problem. This tends to break down when a small issue appears after hours, because the business is forced to troubleshoot without current diagrams, current access lists, or a verified recovery path.
What should a manufacturer do next if the environment feels stable on the surface but fragile underneath?
Start by mapping which systems directly affect scheduling, production release, traceability, quality records, label printing, and shipment completion, then rank them by the cost of one hour of downtime. After that, review remote access, shared accounts, restore capability, and network dependencies with a hard focus on what is documented and what is merely assumed. A competent advisor should be able to explain where current protections are strong, where they are thin, and what proof exists. If that review has not happened recently, compare the environment against your current managed IT support structure and ask for the reports, diagrams, and test evidence that show the plant is actually supportable under pressure.

