Managed IT Services in Truckee, California
Managed IT services in Truckee, California means ongoing responsibility for system health, security, user support, and recovery readiness, so local businesses can keep operations moving, catch problems earlier, and avoid expensive downtime from preventable failures.
At a Truckee property management office, Andrea W. lost file shares, vendor portal access, and quoting tools after an unpatched remote access gateway and a forgotten admin account were abused overnight; emergency cleanup, manual re-entry, and missed bookings drove the disruption to $68,000.
{HOOK_DISCLOSURE}
This article reflects the operational perspective of Scott Morris, a managed IT and cybersecurity professional who helps businesses manage infrastructure stability, user support, cybersecurity exposure, recovery readiness, and continuity risk. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Managed IT Services in Truckee, California because reliable support is not just about fixing tickets; it requires disciplined monitoring, controlled change management, secure identity practices, documented recovery procedures, and practical risk reduction that lowers downtime and security exposure in real business environments.
Managed IT services in Truckee is not a retainer for occasional fixes. It is ongoing operational ownership of endpoints, Microsoft 365 or Google Workspace, network equipment, patching, identity controls, vendor coordination, documentation, and user support. A mature managed IT services model keeps those moving parts under one accountable process so a business is not discovering missing passwords, expired warranties, or neglected firewall updates during an outage.
That matters locally because many Truckee organizations run lean, depend heavily on cloud applications, and still have on-site dependencies such as Wi-Fi, printers, file access, VoIP, point-of-sale, or specialty software tied to a physical office. Weather events, ISP instability, seasonal staffing, and remote owners can turn a minor technical gap into a business interruption. In practice, the issue is rarely the tool alone; it is the process around it: who reviews alerts, who approves changes, who removes old accounts, and who knows what has to come back first if connectivity fails.
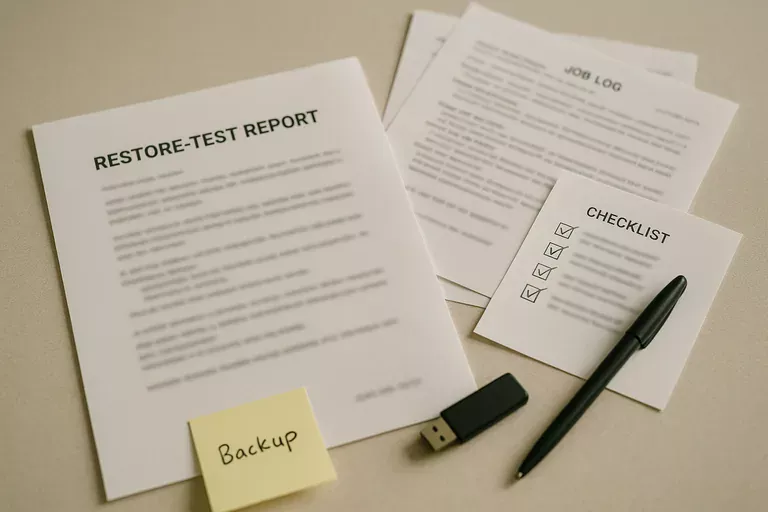
A common mistake is buying piecemeal tools and assuming that equals management. Antivirus without response workflow, backups without restore testing, and MFA without lifecycle review create a false sense of safety. Businesses comparing day-to-day support with a more security-focused support approach in Truckee should look at whether the provider is actually reducing operational risk, not just closing tickets.
What do managed IT services in Truckee, California actually include?
Managed IT services usually includes proactive monitoring, helpdesk support, patch management, endpoint protection oversight, user onboarding and offboarding, vendor coordination, documentation, and continuity planning. What usually separates a stable environment from a fragile one is ownership: someone is accountable for keeping the asset inventory current, standardizing configurations, reviewing security events, and making sure issues are handled before users notice them.
Why does managed IT matter operationally for Truckee businesses?
It matters because business operations now depend on dozens of interconnected systems that fail unevenly. When email, identity, internet access, phones, accounting software, and shared files are managed by different people with no documented handoff, small faults cascade into billing delays, missed customer communication, and avoidable downtime. Managed IT reduces that fragmentation by turning support, maintenance, and security into a repeatable operating function with defined accountability.
Which risks can managed IT services reduce before they become incidents?
- Identity drift: Former staff, seasonal users, and vendors often keep access longer than intended, which raises the risk of unauthorized entry and internal misuse.
- Patch lag: Firewalls, laptops, and line-of-business servers frequently fall behind on security updates when nobody owns maintenance windows and exception tracking.
- Monitoring gaps: Alerts may exist, but if thresholds, escalation, and after-hours ownership are unclear, the warning arrives without a response.
- Documentation failure: During an outage, missing network maps, admin credentials, ISP details, and vendor contacts can add hours to recovery because the environment cannot be reconstructed quickly.
How do managed IT services work in practice day to day?
Day-to-day management should run through a defined workflow: systems report health into monitoring, alerts are triaged by severity, routine patches are scheduled, exceptions are documented, and user changes follow an approval path. Guidance from NIST SP 800-63B matters here because authentication only reduces risk when identity is controlled across the full account lifecycle; in business terms, MFA, password policy, privileged access, and account removal must all be enforced consistently, not selectively. During a routine sign-in review, an experienced IT team may notice repeated after-hours logins from a shared service account that never prompts for MFA; the investigation often reveals an old application exception that was never revisited. The lesson is that mature environments track these exceptions, assign an owner, and review them on a schedule instead of letting temporary access become permanent exposure.

How can a Truckee business tell whether managed IT is being done competently?
A competent provider should be able to show evidence, not just describe intentions. Ask for a current asset inventory, patch compliance reports, alert escalation records, administrative account review logs, backup restore test results, and a documented onboarding and offboarding procedure; those artifacts show whether the environment is being actively managed or merely reacted to. When businesses review ongoing managed IT coverage, one of the first things experienced advisors check is whether reports match reality on the ground, because fragile environments often have tools installed but incomplete device coverage, silent alerting gaps, or servers excluded from policy without clear exception handling.
When does weak managed IT implementation become dangerous?
Weak implementation becomes dangerous when support looks busy but control ownership is missing. A common failure point is an inbox full of automated alerts that nobody reviews, shared local administrator passwords that persist for years, or email MFA enforced for staff but not for privileged and third-party accounts. Prepared organizations follow the evidence-oriented model reflected in CISA incident response guidance because log retention, containment authority, and documented response steps determine whether a business can identify scope, preserve evidence, and recover without guessing; when those pieces are missing, even a small security event becomes expensive and hard to explain.
What should a Truckee business do next before changing providers or expanding support?
Before changing providers or expanding support, leadership should define what the business cannot afford to lose: key applications, acceptable downtime, remote access dependencies, vendor relationships, and the order in which systems must be restored. Then request a plain-language review of current risks, open exceptions, internet and power dependencies, admin access ownership, and recovery evidence. That process usually exposes whether the environment is documented and governable or whether knowledge is still sitting informally in one technician’s head.

