Managed IT Services in Incline Village, Nevada
Managed IT services in Incline Village help local businesses keep systems stable, users supported, and security controls active through monitoring, helpdesk response, patching, and recovery planning that reduce downtime, confusion, and preventable operational risk.
At 9:12 a.m., Ana Maria F. lost access to her firm’s shared file system in Incline Village after a neglected firewall rule exposed remote management to password-spray attempts; nine staff sat idle for most of the day, and emergency recovery, lost billable time, and cleanup reached $67,250.
This opening scenario is derived from real operational incidents observed in managed IT environments. Names and identifying details have been modified for confidentiality.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure, secure user access, maintain stable systems, recover from outages, and improve operational resilience in environments where downtime and data exposure have direct business consequences. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Managed IT Services in Incline Village, Nevada because reliable operations depend on practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and the disciplined processes experienced IT teams use to reduce downtime and security exposure for Reno and Sparks area businesses.
Examples here are meant to help leadership evaluate operations, documentation, and risk rather than replace a technical assessment. This is general technical information; specific network environments and compliance obligations change strategy.
Managed IT services is the ongoing operational management of a business technology environment, not just break-fix support. For many companies in Incline Village, that means someone is accountable for workstation health, Microsoft 365 or Google Workspace administration, network stability, vendor coordination, patching, user onboarding, and the day-to-day processes covered under managed IT services.
- Stability: Monitoring and maintenance keep small faults from becoming business interruptions.
- Security: Account controls, patch discipline, and endpoint protection reduce the chance that a weak password or missed update becomes an entry point.
- Accountability: Documentation, escalation paths, and recovery procedures make it clear who acts when a system fails.
What does managed IT services actually include for an Incline Village business?
It includes ongoing ownership of devices, user accounts, cloud platforms, networking, patching, security tooling, vendor coordination, documentation, and helpdesk response. What usually separates a stable environment from a fragile one is that these tasks are tied together under one operating model instead of being handled ad hoc by different vendors or by an internal staff member whenever something breaks.
Why does managed IT matter so much to daily operations in Incline Village?
Many Incline Village offices run lean. When one firewall rule, one internet circuit, or one line-of-business application supports most of the workday, delays in support turn into idle payroll, missed appointments, and rushed workarounds. Managed IT matters because it shortens the time between detection and response, and it gives leadership a clearer picture of what systems are critical, who owns them, and how failures are contained.
Which risks does competent managed IT reduce before they become incidents?
Competent management usually reduces credential compromise, unpatched-system exposure, cloud misconfiguration, vendor access drift, and extended downtime after equipment or service failures. Guidance in NIST SP 800-63B exists because authentication controls only help when account creation, multifactor authentication enforcement, resets, and offboarding are handled consistently; in business terms, that lowers the chance that an old password or a lingering account becomes the path into email, files, or admin tools. Nevada businesses that store personal information also need reasonable security measures under Nevada Revised Statutes NRS 603A, so weak operational discipline can become both an outage problem and a legal exposure.
How does managed IT work in practice behind the scenes?
In practice, a managed environment runs on recurring workflows: health agents report status to a monitoring platform, alerts are triaged against documented thresholds, critical issues are escalated to named responders, patches are approved and checked for failures, endpoint policies are enforced, and user changes are tied to onboarding and offboarding tickets. During a routine alert review, repeated account lockouts from a conference-room PC led to a deeper check that found an old employee credential still cached in a login script and a forgotten legacy file share still in use. The symptom looked minor, but the real control issue was missing identity cleanup and outdated documentation.

What evidence shows that a managed IT environment is being handled competently?
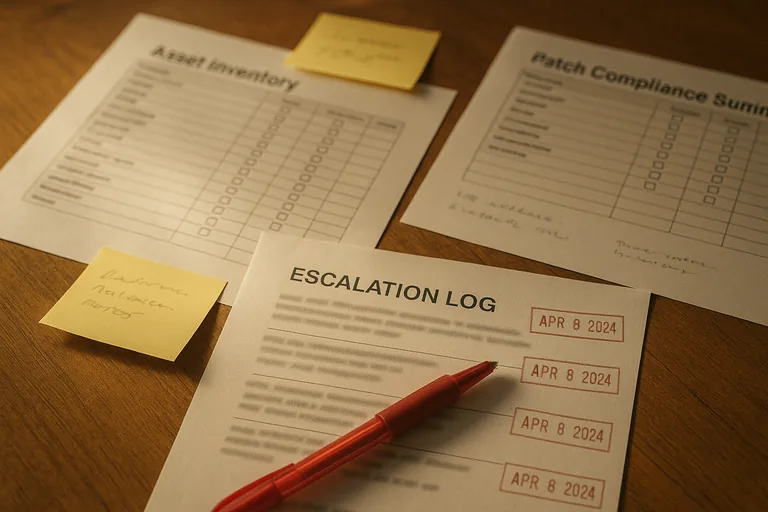
A mature environment produces visible evidence: asset inventory records that match real devices, patch compliance reports showing update status, alert escalation logs identifying who responded and when, access review records for privileged accounts, and change notes for firewall or cloud administration adjustments. If a provider describes broad IT management coverage but cannot show those artifacts, the environment may be running on memory and habit rather than controlled process. In practice, this often breaks down when a ticketing system exists but alerts bypass it, or when backups report success yet no one keeps restore test results.
When does weak managed IT implementation become dangerous?
What should a business review before making its next IT decision?
Before changing providers or renewing an agreement, leadership should review the current asset list, admin account inventory, support scope, after-hours escalation rules, recovery objectives, vendor dependencies, and any compliance obligations tied to customer or employee data. A competent provider should be able to explain what is monitored, how quickly critical alerts are triaged, how offboarding is verified, what exceptions remain unresolved, and which records prove those tasks are being done. That review usually reveals whether the business has a managed environment or only a collection of tools.

