Managed IT Services in Gardnerville, Nevada
Managed IT Services in Gardnerville, Nevada helps local businesses keep systems stable, users supported, and risks controlled through proactive monitoring, disciplined maintenance, and responsive troubleshooting before routine technology issues turn into costly downtime.
At 8:12 on a Tuesday, Ariadna F. found her Gardnerville office unable to process invoices because the server hosting the accounting database had run out of storage, capacity alerts had gone unanswered, and the resulting rework, delays, and lost collections reached $73,000.
This opening scenario is derived from real operational incidents observed in managed IT environments. Names and identifying details have been modified for confidentiality.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure, secure user access, maintain recoverable systems, and restore operations when outages or security incidents disrupt work. Scott Morris has 16+ years of managed IT and cybersecurity experience. His work across Reno and Sparks business technology environments is directly relevant to Managed IT Services in Gardnerville, Nevada because smaller organizations often carry serious operational exposure without large internal IT teams, and experienced support reduces risk through proactive maintenance, documented processes, recovery readiness, defense in depth, and operational resilience rather than ad hoc fixes.
This article explains common operational patterns, evaluation criteria, and control expectations for business IT environments in and around Gardnerville. This is general technical information; specific network environments and compliance obligations change strategy.
In practice, managed IT services is not just a helpdesk contract. It is the ongoing operating discipline around endpoint management, patching, account control, vendor coordination, monitoring, and documentation that keeps a business usable during ordinary weekdays. Businesses comparing managed IT services often miss that the real product is consistent execution, not software licenses.
For Gardnerville offices, a common issue is dependence on a small number of systems: Microsoft 365, a shared file repository, line-of-business software, internet connectivity, and a few key printers or scanners. When one of those dependencies fails, invoicing, scheduling, payroll, or customer service can stall. That is why infrastructure oversight such as network, server, and cloud management in Gardnerville belongs inside the managed service conversation rather than being treated as a separate afterthought.
What do managed IT services in Gardnerville, Nevada actually include?
Managed IT services means a business does not wait for failure before IT work begins. The scope usually includes managed endpoints, servers, Microsoft 365 or similar cloud platforms, user provisioning, patching, monitoring, backup oversight, security tooling, vendor coordination, and support for day-to-day issues. In mature environments, the provider also maintains documentation, standards, and change control so the business is not dependent on one technician’s memory when an outage occurs.
Why does reactive IT management create more business disruption?
Reactive IT looks less expensive until ordinary maintenance is skipped. Storage grows without review, firewall firmware lags, expired accounts stay active, and line-of-business applications break after untested updates. The operational risk is not just one outage; it is cumulative fragility. What usually separates a stable environment from a fragile one is whether somebody is accountable for routine tasks before users notice symptoms, because once staff are idle and vendors are blaming each other, even a modest technical fault becomes an expensive business event.
Which risks can competent managed IT services reduce?
Competent managed IT services usually reduce credential abuse, patch-related exposure, data loss, vendor coordination failures, and long recovery times after outages. Guidance in NIST SP 800-63B exists because user identity is often the easiest path into a business environment; in practice, that means multifactor authentication, consistent account lifecycle control, and review of privileged access activity. A common failure point is deploying security tools without enforcing them everywhere, which leaves one legacy admin account or one unmanaged laptop as the path of least resistance.
How do managed IT services work in practice day to day?
Day to day, competent management is repetitive and documented: monitoring watches servers, internet circuits, storage, and security events; alerts are triaged against written thresholds; failed patches are remediated; user changes are approved and logged; and recurring issues are tied back to root causes instead of being reset and forgotten. During one routine review pattern seen in real environments, a disk latency alert on a file server led to the discovery that a line-of-business database and general file storage were competing for the same aging volume, causing intermittent freezes users had been reporting for weeks; the lasting fix was capacity planning, workload separation, and documented thresholds rather than another reboot. Real evidence of this work includes monitoring dashboards, change records, asset inventories, patch compliance reports, and escalation notes showing who responded, when, and what was done.
How can a business tell whether its IT provider is actually doing the work?
- Asset accuracy: A competent provider can produce a current inventory of workstations, servers, network equipment, cloud services, and key software, with enough detail to show ownership and support status.
- Patch evidence: Mature environments generate patch compliance or exception reports that show which systems are current, which failed, and what remediation is scheduled.
- Access control records: Onboarding, offboarding, privileged account review, and multifactor enforcement should leave a visible record rather than relying on verbal confirmation.
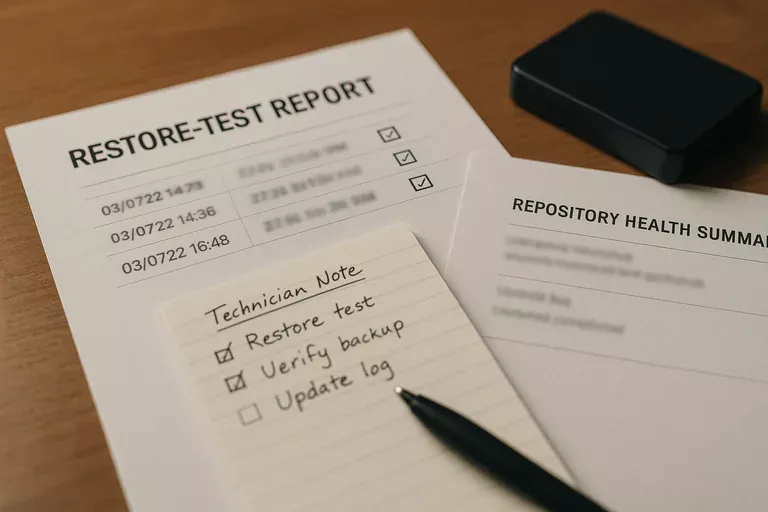
- Recovery proof: Backup software alone is not evidence; documented restore test results and a defined recovery sequence for critical systems are what show the environment is recoverable.
When does weak implementation become dangerous?
What should a Gardnerville business review before the next outage or security event?
Before the next outage or security event, leadership should be able to answer a few operational questions without guessing: which systems are truly critical, who approves access changes, what the acceptable downtime is for each major function, when the last restore test and access review occurred, and how after-hours escalation works. A competent provider should be able to explain those answers in plain business language and show the underlying records. If those answers depend on tribal knowledge, scattered emails, or a technician’s memory, the environment is more fragile than it appears.
If the situation described at the start feels uncomfortably plausible, speak with an experienced advisor today before a routine alert turns into the kind of interruption that costs real money. A short operational review can clarify whether the current IT approach is documented, monitored, and recoverable or whether hidden gaps are still waiting for a busy Tuesday morning.

