Managed IT Services in Carson City, Nevada
Managed IT services in Carson City, Nevada give businesses responsive local oversight of systems, users, security, and support so routine issues are handled early, outages are shorter, and leadership gets clearer visibility into operational technology risk.
During a Monday payroll run, Alyssa H. discovered the controller’s email account had been forwarding invoice threads for weeks because no one was reviewing sign-in alerts or stale admin access; by the time the Carson City business contained the fraud and rebuilt trust with vendors, the disruption had cost $65,250, which is exactly the type of preventable exposure managed IT services in Carson City, Nevada are meant to reduce.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
As documented on Scott Morris, Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure, secure user access, maintain stable systems, recover from operational failures, and improve continuity planning in real business environments. Scott Morris has 16+ years of managed IT and cybersecurity experience. That experience is directly relevant to Managed IT Services in Carson City, Nevada because competent technology management is not only about fixing tickets; it is about reducing downtime, controlling security exposure, maintaining recovery readiness, and building resilient, compliance-aware environments for businesses across Northern Nevada, including Reno and Sparks.
This article explains common operational patterns, controls, and evaluation points seen in business IT environments, but it is not a substitute for a review of your own systems. This is general technical information; specific network environments and compliance obligations change strategy.
Managed IT services is not just outsourced helpdesk coverage. For a Carson City business, it usually means one accountable function overseeing workstations, Microsoft 365, network equipment, line-of-business applications, vendor coordination, user support, and change control under a defined process. Good managed IT services reduce the number of surprises leadership has to absorb because maintenance, monitoring, and escalation are not left to whoever notices a problem first.
A common failure point is fragmented ownership. The copier vendor manages scanning, the internet provider manages the circuit, an office employee has the Microsoft 365 global admin password, and nobody owns patch approval, license cleanup, or offboarding. That is why mature environments connect day-to-day support with managed cybersecurity services in Carson City, identity controls, documented vendor contacts, and change records; in practice, the issue is rarely the tool alone, it is the process around it.
Operationally, the baseline should include an accurate asset inventory, patching with exception tracking, endpoint protection, monitored backups, access reviews, and written recovery steps for critical systems. What usually separates a stable environment from a fragile one is evidence, not intent: patch compliance reports, alert escalation logs, onboarding and offboarding checklists, and recovery test notes. That is the difference between casual support and structured IT management that leadership can actually evaluate.
What do managed IT services in Carson City, Nevada actually cover?
In a mature business environment, managed IT services cover device management, user support, software updates, vendor coordination, account administration, endpoint security, documentation, and response workflow when something fails. If a business depends on cloud email, accounting platforms, remote access, printers, Wi-Fi, and local line-of-business software, someone must maintain those dependencies as one operating system for the company rather than as separate tasks. What usually separates a stable environment from a fragile one is whether that responsibility is assigned clearly and reviewed consistently.
Why do Carson City businesses use managed IT services instead of waiting for something to break?
Reactive support looks less expensive until small issues compound into downtime, fraud exposure, or staff workarounds that create new risk. A common failure point is deferred maintenance: laptops stop receiving updates, storage alerts are ignored, and licensing changes happen without review until a user loses access during a deadline. Managed service models usually improve business continuity because monitoring, maintenance windows, and escalation paths are planned ahead of failure rather than invented during it.
Which operational risks do managed IT services reduce most effectively?
The largest risks are usually not dramatic attacks but neglected basics: stale user accounts, inconsistent multifactor authentication, unsupported devices, missing documentation, weak vendor handoffs, and no one reviewing warning signs. Guidance in NIST SP 800-63B matters here because identity controls only reduce risk when authentication is enforced consistently across the full account lifecycle, including onboarding, privilege changes, and offboarding. Nevada businesses handling personal information also need to understand Nevada Revised Statutes NRS 603A, which requires reasonable security measures; in business terms, that means user access, system protection, and incident handling cannot be informal habits. This is also why many organizations pair operations with cybersecurity management rather than treating security as a separate project that only appears after an incident.
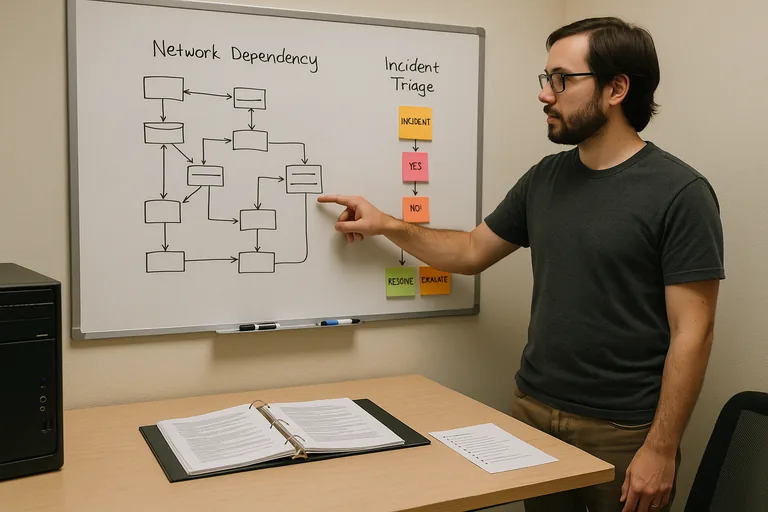
How do managed IT services work in practice inside a real business environment?
In practice, endpoints report health to a monitoring platform, patch deployment follows maintenance windows with exception notes, tickets are tied to users and assets, and alerts move through a documented triage path from detection to containment. During a routine review, repeated account lockouts from a disabled warehouse user triggered investigation; the source turned out to be a copier address book and a stale VPN profile, which showed that offboarding had been handled informally instead of through a checklist linked to devices, applications, and permissions. A competent provider should be able to explain who receives the alert, how the issue is investigated, when the business is notified, and where the remediation record is stored afterward.
How can a business tell whether its managed IT provider is actually doing the work?
Ask for observable records, not adjectives. Mature environments produce monthly asset inventory reports, patch compliance summaries by device group, backup success records paired with restore test dates, privileged access review logs, open exception lists, and escalation history for after-hours alerts. A common failure point is reporting that shows green check marks without naming excluded systems, unmanaged devices, or overdue remediation, because leadership then assumes risk is controlled when it has only been hidden from the dashboard.
When does weak managed IT implementation become dangerous?
Weak implementation becomes dangerous when controls exist on paper but ownership is blurry. In environments that have not been reviewed recently, it is common to find multifactor authentication enabled for employees but exempted for legacy admin accounts, monitoring installed but routed to an unattended mailbox, or backup jobs marked successful even though a critical database server has been excluded for months. This tends to break down during turnover, vacations, or vendor disputes, when undocumented knowledge disappears and a manageable issue becomes downtime, data exposure, or an expensive forensic exercise.
What should a Carson City business do before changing providers or formalizing managed IT services?
Leadership should identify business-critical systems, confirm who holds administrative control, and request concrete records: asset lists, Microsoft 365 admin roles, firewall and internet ownership, warranty status, backup restore evidence, and unresolved security exceptions. If those records are incomplete, the first project is usually not a new tool purchase; it is documentation cleanup, access review, and a transition plan that preserves continuity while responsibilities are clarified. That review tells a business whether it has a maintainable environment or a fragile one being held together by memory.

