Managed Cybersecurity Services
Managed cybersecurity services combine continuous monitoring, threat detection, response support, and security maintenance to help businesses reduce preventable disruption, contain incidents faster, and make day-to-day technology operations more stable, accountable, and defensible.
Abigail T. called after her accounting team found vendor payments had been rerouted from a compromised Microsoft 365 mailbox. Multifactor authentication had been enforced for some users but not finance staff, hidden inbox rules suppressed warning messages, and the business spent three days unwinding fraud, downtime, and recovery work that totaled $50,750.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
This article explains common operational patterns, controls, and evaluation criteria used when reviewing managed cybersecurity programs. This is general technical information; specific network environments and compliance obligations change strategy.
Managed cybersecurity services are the ongoing security function wrapped around business technology: identity protection, endpoint security, email defense, vulnerability review, log monitoring, policy enforcement, and coordinated response when something looks wrong. A useful way to evaluate managed cybersecurity services is to ask whether they create operational visibility and accountability, not whether a provider can list enough tools.
In practice, this work overlaps with managed IT services because weak maintenance often becomes a security problem and poor security controls often become a downtime problem. A common failure point is assuming antivirus covers the risk while stale accounts remain active, operating systems drift out of patch compliance, and important alerts route to an inbox nobody checks after hours.
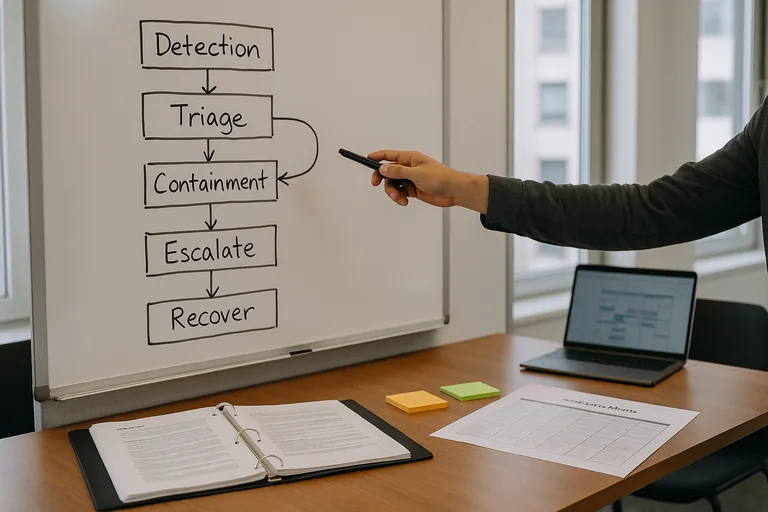
What usually separates a stable environment from a fragile one is operational ownership. A mature security management program maintains asset inventory, privileged account review, endpoint policy enforcement, and escalation rules so the business can answer basic questions quickly: what is affected, who is responding, what data may be exposed, and how long recovery is likely to take.
What are managed cybersecurity services?
Managed cybersecurity services are a continuous operating model for protecting business systems rather than a one-time software purchase. In mature environments, that means someone is responsible for endpoint detection, identity controls, email security, vulnerability management, logging, alert triage, incident coordination, and policy enforcement across the full environment. In practice, the issue is rarely the tool alone; it is the process around it, including who reviews alerts, who approves exceptions, and how response decisions are documented.
Why do they matter beyond antivirus?
Most business incidents no longer begin with a traditional virus signature. They begin with credential theft, inbox rule abuse, browser token theft, exposed remote access, unreviewed admin rights, or an overlooked cloud configuration change. Antivirus may catch malicious files, but it does not by itself manage account lifecycle, verify multifactor enforcement, investigate suspicious sign-ins, or coordinate containment when a user clicks a convincing phishing message. That is why businesses with security tools can still suffer real disruption when no one owns the surrounding workflow.
Which risks do they reduce in day-to-day operations?
How do managed cybersecurity services work in practice?
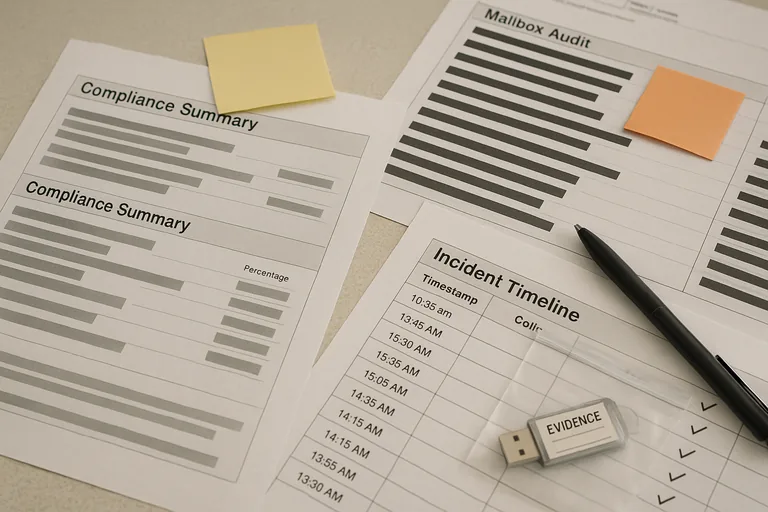
A competent provider collects telemetry from endpoints, identity platforms, email systems, firewalls, and cloud services, then triages events by severity and business impact. High-confidence events should trigger containment steps such as disabling an account, isolating a device, blocking a sender, or escalating to leadership with a documented timeline. During a routine review, an impossible-travel sign-in alert led to a dormant contractor account that was still synchronized from Active Directory and still sitting in an old multifactor exception group. That kind of discovery is common in inherited environments, and it is why guidance from CISA incident response training and guides emphasizes log availability, evidence preservation, and structured containment before the situation spreads.
How can a business verify the controls are real?
A mature environment should produce evidence, not reassurance. That evidence usually includes patch compliance reports, endpoint deployment status, vulnerability scan summaries, alert escalation logs, access review records, mailbox auditing, exception tracking, and incident timelines showing what was detected, who responded, and how the issue was contained. Without those records, businesses often assume protections are active when in reality the software is installed but unmanaged, the alerts are noisy but ignored, or the policy exists in documentation but not in actual enforcement.
What warning signs point to a weak or dangerous implementation?
What should a decision-maker do next?
Start with a current-state review that answers a few operational questions clearly: what devices and accounts exist, which systems are monitored, where privileged access lives, which alerts trigger human review, what exceptions are still open, and what evidence exists from the last security review. A competent provider should be able to explain coverage, gaps, response ownership, and recent verification results in plain language. If those answers are vague, delayed, or heavily tool-focused, the business is probably dealing with assumed security rather than managed security.
If the possibility of a finance mailbox compromise, hidden rules, and a $50,750 cleanup feels uncomfortably plausible, reach out to an experienced advisor who can help interpret the gaps, validate the controls, and turn assumptions into documented protection before the next incident tests the environment.

