IT Strategy Engagements
IT strategy engagements connect business priorities to technology decisions by mapping risk, costs, dependencies, and recovery needs before projects begin. Done well, they give leadership a practical roadmap instead of disconnected upgrades and recurring surprises.
Alana R. approved a warehouse expansion and a phone-system move without a formal IT strategy engagement; the old ERP print server was still tied to a legacy subnet no one documented. On the first shipping day after cutover, labels failed, trucks sat idle for nine hours, and expedited freight, overtime, and missed orders pushed the disruption to $58,000.
A sound engagement can reduce risks that stay hidden until a move, audit, or outage exposes them: undocumented line-of-business dependencies, privileged accounts with no review cadence, aging switches carrying voice and production traffic on the same flat network, and vendor contracts that leave no clear recovery path. For medical practices and other regulated offices, it should also connect technical decisions to HIPAA security responsibilities or similar obligations, because a system that is difficult to restore can quickly become a confidentiality, integrity, and availability problem.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage, secure, maintain, and recover technology environments where uptime, security, and recovery readiness materially affect operations. Scott Morris has 16+ years of managed IT and cybersecurity experience. His work with Reno and Sparks business environments is grounded in practical risk reduction, business continuity, secure infrastructure management, disaster recovery readiness, compliance-aware system management, and the operational resilience that makes IT strategy engagements useful rather than theoretical.
This article explains common operational patterns, evaluation points, and implementation signals used in business IT planning. This is general technical information; specific network environments and compliance obligations change strategy. Regulated offices, multi-site firms, and businesses with legacy applications often need narrower review before decisions are made.
An IT strategy engagement is a structured review of how revenue-producing work depends on systems, vendors, connectivity, security controls, support processes, and recovery capability. It sits upstream of projects and purchases. In practice, this is where IT consulting and vCIO planning should translate leadership goals into an asset baseline, dependency map, budget priorities, and a decision sequence that reduces avoidable disruption.
- Current-state baseline: Identify what is actually in use, who supports it, where it fails, and which business processes depend on it.
- Risk and dependency mapping: Expose hidden relationships between applications, vendors, internet circuits, licensing, identity systems, and recovery requirements.
- Roadmap and governance: Turn findings into sequenced actions with ownership, timing, budget expectations, and business justification.
During a routine review after repeated Wi-Fi complaints, an experienced team may find the wireless issue is only the symptom: an old DHCP scope, undocumented VLAN changes, and a cloud phone rollout sharing the same switch stack without capacity planning. That is why strategic IT leadership is less about buying tools and more about exposing hidden dependencies before a project, relocation, or audit turns them into downtime.
What is an IT strategy engagement?
An IT strategy engagement is a decision framework, not a product quote and not a one-time network scan. It identifies which systems support core workflows, where operational risk sits, what dependencies exist between vendors and infrastructure, and which changes should happen first. The useful output is a prioritized roadmap with business rationale, budget ranges, ownership, and timing so leadership can make technology decisions with fewer blind spots.
Why does it matter to operations and budgeting?
It matters because many business disruptions come from poorly sequenced change rather than a single dramatic failure. A company replaces circuits before validating VPN dependencies, migrates email without cleaning up stale accounts, or rolls out new software without checking bandwidth, retention, printing, or support ownership. Strategy work reduces that collision risk and usually improves budget quality because leaders see lifecycle costs, licensing overlap, project prerequisites, and recovery obligations before money is committed.
Which risks can it reduce before they become incidents?
How does an IT strategy engagement work in practice?
In practice, the engagement usually starts with business-process interviews, asset inventory validation, and review of diagrams, admin access, support contracts, and backup status. Experienced teams then map critical workflows to underlying systems, define recovery objectives, identify single points of failure, and compare current controls to a framework such as the NIST Cybersecurity Framework, which exists to make risk management measurable across identify, protect, detect, respond, and recover functions. Real output should include a current-state inventory, dependency map, risk register, 12-to-36-month roadmap, and decision records showing why each recommendation was made.
What evidence shows the strategy is actually working?
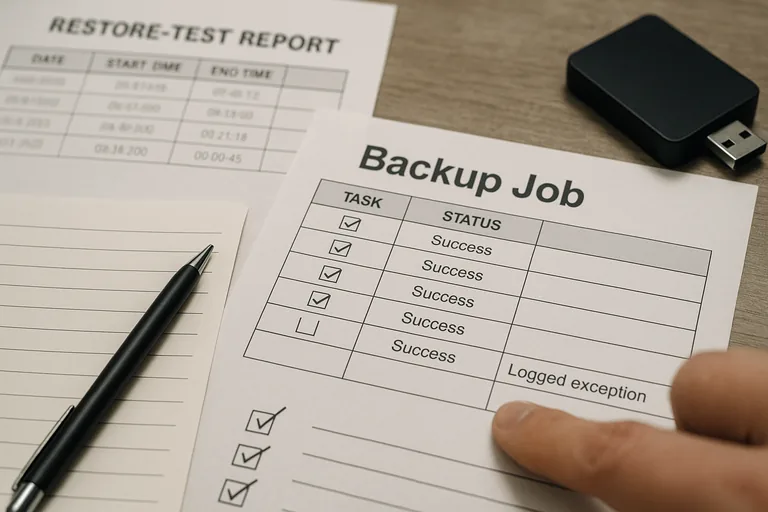
- Evidence exists: The environment should produce asset inventories, network diagrams, patch compliance reports, and named owners rather than a slide deck with generic recommendations.
- Reviews have cadence: Access reviews, backup restore tests, and vendor renewals should be scheduled and documented, not handled only when something breaks.
- Exceptions are visible: If a server cannot be patched or an application cannot support multifactor authentication, the exception should be logged with risk, compensating controls, and a target decision date.
- Roadmap ties to business events: Projects should align with lease changes, hiring plans, compliance deadlines, acquisitions, or software renewals so IT work supports operations instead of surprising them.
When does weak implementation become dangerous?
What should happen after the strategy is documented?
If the idea of trucks waiting, staff improvising, and costs stacking up because one undocumented dependency was missed feels uncomfortably familiar, speak with an experienced advisor before the next move, migration, or expansion. A disciplined IT strategy engagement can clarify what must be fixed first, what can wait, and how to reduce avoidable disruption.

