IT Consulting & vCIO Services
IT consulting and vCIO services give leadership structured guidance for budgeting, risk decisions, infrastructure planning, vendor oversight, and recovery readiness, so technology supports operations instead of creating hidden cost, downtime, and accountability gaps.
At 9:17 a.m. on a quarter-close Tuesday, Aitana K. learned the aging storage array under the accounting server had failed after months of ignored capacity alerts, no escalation owner, and no replacement budget; invoicing stopped, payroll slipped, and the unplanned recovery and replacement bill reached $56,900.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
This article explains common operational patterns, decision points, and failure modes around strategic IT oversight. This is general technical information; specific network environments and compliance obligations change strategy. Regulatory, contractual, and business continuity requirements should always be matched to the actual systems and data involved.
IT consulting and vCIO services sit above daily troubleshooting. They give leadership a structured way to decide what must be replaced, what can be deferred, which risks need funding, and how technology choices affect uptime, security, vendor dependency, and cash flow.
This role is different from reactive support. Day-to-day managed IT services keep users working, but a vCIO should maintain the asset lifecycle, budget forecasting, standards, recovery objectives, licensing ownership, and decision records that prevent the environment from drifting into expensive surprise.
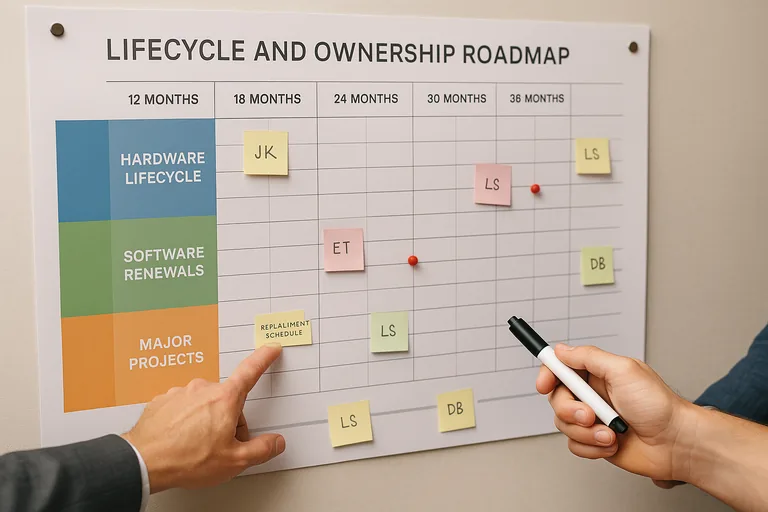
In mature environments, strategic IT oversight produces visible outputs: a current asset inventory, a roadmap tied to business priorities, a risk register, renewal calendars, documented recovery assumptions, and clear ownership for systems that would materially disrupt operations if they failed.
What are IT consulting and vCIO services actually responsible for?
These services are responsible for technology governance, not just technical tasks. That means translating business plans into system standards, replacement timelines, security priorities, vendor accountability, and budget decisions. A common failure point is assuming the role only selects products; in practice, it should also define who owns critical systems, which risks are accepted, and what operational dependencies would hurt revenue if they failed.
Why do these services matter before something breaks?
They matter before something breaks because most IT disruption starts as an ownership problem. Expired software maintenance, unsupported network gear, a single employee holding the only admin access to a cloud tenant, or a line-of-business application with no documented recovery objective can sit quietly for months. The outage is the visible event, but the real failure usually happened earlier when nobody was reviewing lifecycle, access, contracts, and business impact together.
What risks does a vCIO reduce before they become incidents?
- Lifecycle risk: Hardware and software age out, warranties lapse, and replacement costs hit as emergencies instead of planned capital decisions.
- Identity and vendor risk: Admin rights, third-party access, and SaaS ownership accumulate over time, increasing the chance of misuse or lockout during staff changes.
- Continuity risk: Recovery priorities are often undefined, so teams restore systems in the wrong order and the business waits on the wrong dependency.
- Compliance and reporting risk: Leadership may assume policies exist, yet no documented controls, review cadence, or evidence can be produced when regulators, insurers, or customers ask.
How does competent IT consulting and vCIO oversight work in practice?
Competent oversight usually runs on a monthly and quarterly cadence: asset and renewal review, budget forecasting, project prioritization, vendor management, patch and vulnerability trend review, access exceptions, and incident lessons translated into policy or design changes. During a routine leadership review, repeated VPN logins from a terminated user account can trigger deeper investigation; experienced teams often discover the account was disabled in email but left active in a remote access group and a SaaS admin role because offboarding was split across three owners. Guidance in NIST SP 800-63B matters here because identity controls only reduce risk when authentication and account lifecycle management are enforced consistently, which is why a competent vCIO function should require joiner-mover-leaver workflows, exception tracking, and review records rather than assuming MFA alone solves the problem.
How can a business tell whether the service is real or just a meeting on the calendar?
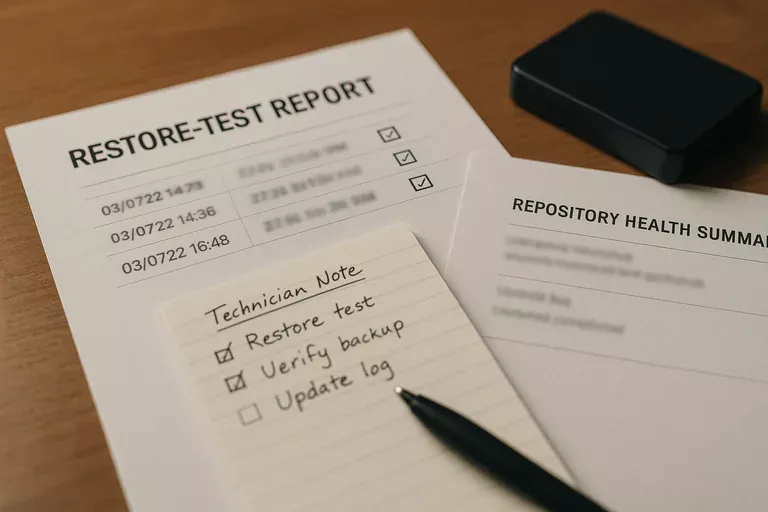
A business should ask for evidence, not adjectives. Competent delivery usually leaves behind a current asset inventory, a 12-to-36-month lifecycle plan, meeting notes with named owners and due dates, patch compliance reports, access review logs, vendor contract and renewal tracking, documented recovery objectives, and restore test results that show important systems were actually recovered within expected time. If the only artifact is a slide deck summarizing risks without dates, ownership, and follow-up status, the service is closer to advisory theater than operational management.
When does weak implementation become dangerous?
Weak implementation becomes dangerous when the title exists but the operating model does not. This tends to break down when a quarterly review is disconnected from helpdesk data, when monitoring alerts have no escalation owner, when standards are written but exceptions are never tracked, or when leadership is told backup, MFA, and endpoint protection are in place without any evidence of enforcement gaps. During incident response, it is common to discover shared admin credentials, undocumented internet failover settings, or obsolete servers still running a critical workflow because nobody maintained a decision log or replacement plan.
What should leadership do next?
Leadership should start by asking for seven concrete items: a current asset inventory, a system ownership map, a major vendor list, a replacement schedule, clear security priorities, documented recovery objectives, and proof of the last access review and restore test. What usually separates a stable environment from a fragile one is not the tool alone; it is whether the organization can produce current documentation, explain accepted risk, and show who is accountable for fixing exceptions before they become outages.

